
Google has taken techniques to ax dozens of fraudulent applications from the formal Enjoy Retailer that ended up noticed propagating Joker, Facestealer, and Coper malware family members as a result of the virtual marketplace.
While the Android storefront is thought of to be a dependable supply for identifying and putting in apps, terrible actors have consistently discovered strategies to sneak earlier security boundaries erected by Google in hopes of luring unsuspecting customers into downloading malware-laced apps.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The most current results from Zscaler ThreatLabz and Pradeo are no distinctive. “Joker is one particular of the most distinguished malware family members concentrating on Android devices,” researchers Viral Gandhi and Himanshu Sharma claimed in a Monday report.
“Inspite of public consciousness of this certain malware, it keeps discovering its way into Google’s official application store by routinely modifying the malware’s trace signatures such as updates to the code, execution procedures, and payload-retrieving approaches.”

Classified as fleeceware, Joker (aka Bread) is designed to subscribe end users to unwanted paid products and services or make calls to high quality figures, whilst also accumulating SMS messages, make contact with lists, and device information. It was initial observed in the Play Retailer in 2017.
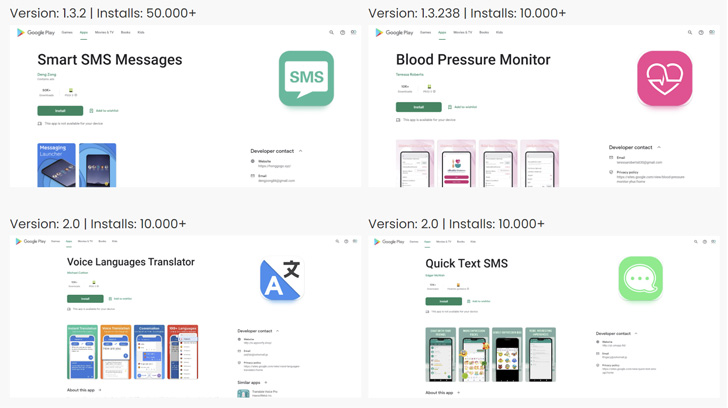
A total of 53 Joker downloader apps have been discovered by the two cybersecurity firms, with the programs downloaded cumulatively about 330,000 instances. These applications commonly pose as SMS, photograph editors, blood tension monitor, emoji keyboards, and translation apps that, in flip, request elevated permissions for the system to have out its functions.
“As a substitute of waiting for applications to attain a specified volume of installs and reviews before swapping for a malware-laced edition, the Joker developers have taken to hiding the malicious payload in a prevalent asset file and bundle application employing commercial packers,” the researchers discussed the new tactic adopted by the persistent malware to bypass detection.
It truly is not just Joker, as security researcher Maxime Ingrao last 7 days disclosed eight applications containing a distinct variant of the malware called Autolycos that racked up a whole of in excess of 3 million downloads prior to their removal from the app shop just after additional than 6 months.
“What is new about this variety is that it no for a longer time necessitates a WebView,” Malwarebytes researcher Pieter Arntz explained. “Not necessitating a WebView significantly minimizes the odds that the consumer of an affected system notices some thing fishy is going on. Autolycos avoids WebView by executing URLs on a distant browser and then including the final result in HTTP requests.”
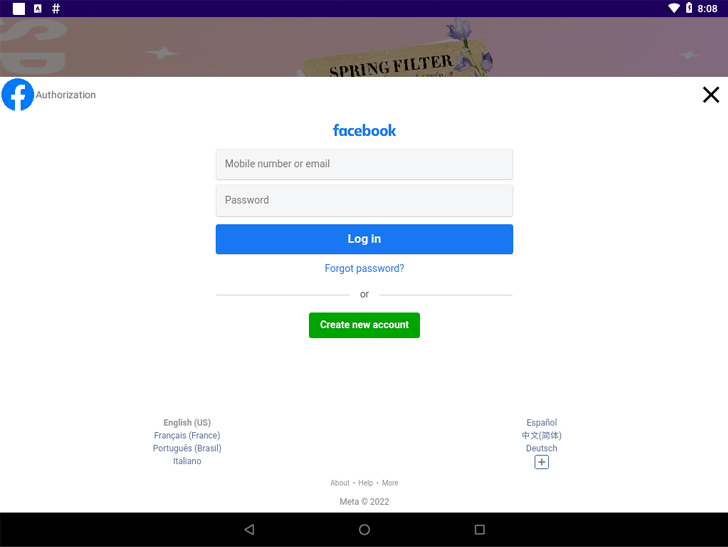
Also found out in the official market were applications embedding Facestealer and Coper malware. Although the previous allows the operators to siphon Facebook qualifications and auth tokens, Coper — a descendant of the Exobot malware — functions as a banking trojan that can steal a huge array of details.

Coper is “capable of intercepting and sending SMS textual content messages, making USSD (Unstructured Supplementary Company Details) requests to mail messages, keylogging, locking/unlocking the system screen, performing overly attacks, preventing uninstalls and typically permitting attackers to get control and execute instructions on infected unit by means of distant link with a C2 server,” the scientists said.
The malware, like other banking trojans, is also known to abuse the accessibility permissions on Android to achieve total handle of the victim’s phone. The list of Facestealer and Coper dropper applications is as follows –
- Vanilla Camera (cam.vanilla.snapp)
- Unicc QR Scanner (com.qrdscannerratedx)
If anything, the findings insert to Google’s storied heritage of struggling to retain this sort of fleeceware and adware applications off its mobile application retailer, in aspect owing to a multitude of evolving strategies adopted by menace actors to fly less than the radar.
Apart from the standard principles of thumb when it arrives to downloading applications from app suppliers, customers are suggested to chorus from granting unnecessary permissions to apps and verify their legitimacy by checking for developer info, reading through opinions, and scrutinizing their privacy guidelines.
Uncovered this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to study far more special content we publish.
Some elements of this article are sourced from:
thehackernews.com


 FBI Warns of Fake Cryptocurrency Apps Stealing Millions from Investors
FBI Warns of Fake Cryptocurrency Apps Stealing Millions from Investors