A blend of banking applications, cryptocurrency wallets, and browsing applications from the U.S. and Spain are the focus on of a newly found out Android trojan that could allow attackers to siphon individually identifiable facts from contaminated devices, together with banking credentials and open the door for on-gadget fraud.
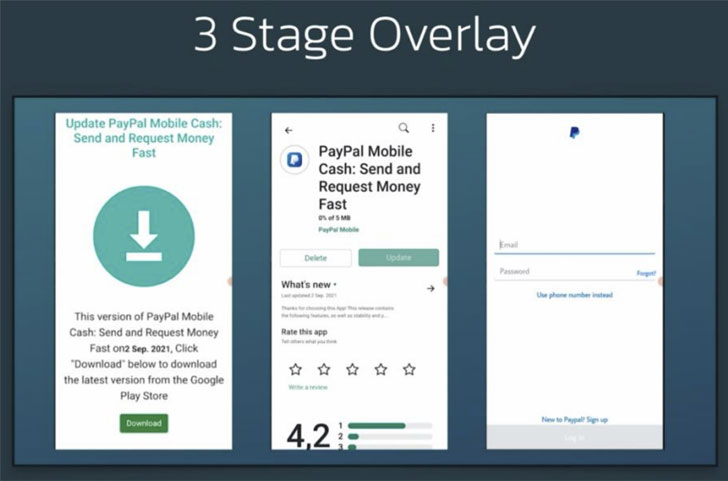
Dubbed S.O.V.A. (referring to the Russian term for owl), the present-day edition of the banking malware arrives with myriad attributes to steal credentials and session cookies via web overlay attacks, log keystrokes, conceal notifications, and manipulate the clipboard to insert modified cryptocurrency wallet addresses, with potential plans to include on-product fraud by means of VNC, have out DDoS attacks, deploy ransomware, and even intercept two-factor authentication codes.
The malware was discovered in the commencing of August 2021 by researchers from Amsterdam-based cybersecurity agency ThreatFabric.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Overlay attacks typically entail the theft of confidential user details making use of malware that overlays its have windows on prime of a different system. On the other hand, the pilfering of valid session cookies is notably awful as it permits the criminals to log in and just take more than accounts from the buyers with out the need for figuring out the banking credentials.
“The next set of options, additional in the long term developments, are incredibly innovative and would force S.O.V.A. into a different realm for Android malware, building it likely a person of the most state-of-the-art bots in circulation, combining banking malware with automation and botnet capabilities,” ThreatFabric said in a report shared with The Hacker News.
Even though the malware is considered to be in its nascent levels of progress, S.O.V.A.’s developers have been promotion the product on hacking community forums, searching to recruit testers to trial the malware on a substantial number of units and its bot abilities. “Not redistribution of Cerberus/Anubis, the bot is composed from scratch,” the discussion board put up browse.

“[S.O.V.A.] is nonetheless a venture in its infancy, and now delivers the very same basic attributes as most other modern Android banking malware,” the scientists stated. “Even so, the author powering this bot obviously has significant anticipations for his product or service, and this is demonstrated by the author’s perseverance to check S.O.V.A. with third parties, as properly as by S.O.V.A.’s explicit element roadmap.”
Observed this article intriguing? Observe THN on Fb, Twitter and LinkedIn to browse a lot more special information we post.
Some sections of this posting are sourced from:
thehackernews.com


 UK to Revamp ICO as Part of Data Rules Reform
UK to Revamp ICO as Part of Data Rules Reform