The suspected Pakistan-connected danger actor recognised as Transparent Tribe is utilizing malicious Android applications mimicking YouTube to distribute the CapraRAT mobile remote entry trojan (RAT), demonstrating the continued evolution of the action.
“CapraRAT is a highly invasive tool that provides the attacker management above a great deal of the details on the Android equipment that it infects,” SentinelOne security researcher Alex Delamotte reported in a Monday evaluation.
Transparent Tribe, also regarded as APT36, is acknowledged to target Indian entities for intelligence-accumulating uses, relying on an arsenal of resources capable of infiltrating Windows, Linux, and Android methods.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

A important ingredient of its toolset is CapraRAT, which has been propagated in the sort of trojanized protected messaging and contacting apps branded as MeetsApp and MeetUp. These weaponized applications are distributed making use of social engineering lures.
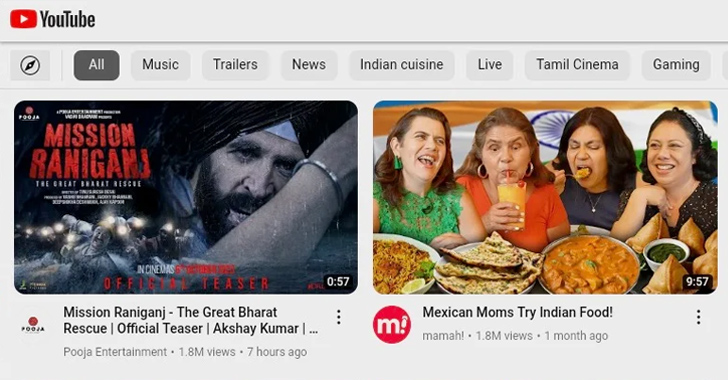
The newest established of Android deal (APK) files found out by SentinelOne are engineered to masquerade as YouTube, 1 of which reaches out to a YouTube channel belonging to “Piya Sharma.”
The application is named soon after its namesake, indicating that the adversary is employing romance-based mostly phishing methods to entice targets into setting up the applications. The record of applications is as follows –
- com.Foundation.media.service
- com.moves.media.tubes
- com.films.watchs.share
When set up, the applications ask for intrusive permissions that make it possible for the malware to harvest a wide assortment of sensitive info and exfiltrate it to an actor-managed server. CapraRAT is also able of initiating phone phone calls as well as intercepting and blocking incoming SMS messages.
“Clear Tribe is a perennial actor with trusted practices,” Delamotte explained. “The fairly small operational security bar allows swift identification of their equipment. People today and corporations related to diplomatic, armed forces, or activist issues in the India and Pakistan locations need to evaluate protection versus this actor and threat.”
Found this post appealing? Comply with us on Twitter and LinkedIn to read through a lot more unique content we put up.
Some components of this write-up are sourced from:
thehackernews.com

 Microsoft AI Researchers Accidentally Expose 38 Terabytes of Confidential Data
Microsoft AI Researchers Accidentally Expose 38 Terabytes of Confidential Data