Initiatives to disrupt TrickBot may have shut down most of its critical infrastructure, but the operators driving the notorious malware aren’t sitting idle.
In accordance to new results shared by cybersecurity firm Netscout, TrickBot’s authors have moved parts of their code to Linux in an try to widen the scope of victims that could be focused.
TrickBot, a financial Trojan 1st detected in 2016, has been historically a Windows-centered crimeware alternative, using various modules to execute a vast variety of destructive activities on focus on networks, which includes credential theft and perpetrate ransomware attacks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
But around the previous several months, twin attempts led by the US Cyber Command and Microsoft have helped to get rid of 94% of TrickBot’s command-and-control (C2) servers that were in use and the new infrastructure the criminals functioning TrickBot tried to deliver on the web to replace the beforehand disabled servers.
Despite the methods taken to impede TrickBot, Microsoft cautioned that the danger actors powering the botnet would very likely make initiatives to revive their operations.
TrickBot’s Anchor Module
At the conclusion of 2019, a new TrickBot backdoor framework named Anchor was found out applying the DNS protocol to communicate with C2 servers stealthily.
The module “lets the actors — probable TrickBot clients — to leverage this framework in opposition to increased-profile victims, explained SentinelOne, adding the “skill to seamlessly integrate the APT into a monetization enterprise product is proof of a quantum shift.”
Indeed, IBM X-Drive spotted new cyberattacks before this April revealing collaboration amongst FIN6 and TrickBot teams to deploy the Anchor framework from corporations for economic profit.
The variant, dubbed “Anchor_DNS,” enables the contaminated customer to make use of DNS tunneling to create communications with the C2 server, which in change transmits info with solved IPs as a response, NTT scientists claimed in a 2019 report.
But a new sample uncovered by Phase 2 Security researcher Waylon Grange in July identified that Anchor_DNS has been ported to a new Linux backdoor edition identified as “Anchor_Linux.”
“Generally shipped as component of a zip, this malware is a light-weight Linux backdoor,” Grange reported. “Upon execution it installs by itself as a cron career, determines the general public IP [address] for the host and then begins to beacon by means of DNS queries to its C2 server.”
How the C2 Communication Works Employing Anchor
Netscout’s most recent exploration decodes this stream of communication in between the bot and the C2 server. In the course of the original setup period, the shopper sends “c2_command ” to the server alongside with information and facts about the compromised technique and the bot ID, which then responds with the information “signal /1/” again to the bot.
As an acknowledgment, the bot sends the similar message again to the C2, following which the server remotely issues the command to be executed on the client. In the previous action, the bot sends back the outcome of the execution to the C2 server.
“Each individual component of communication made to the C2 follows a sequence of 3 diverse DNS queries,” Netscout security researcher Suweera De Souza reported.
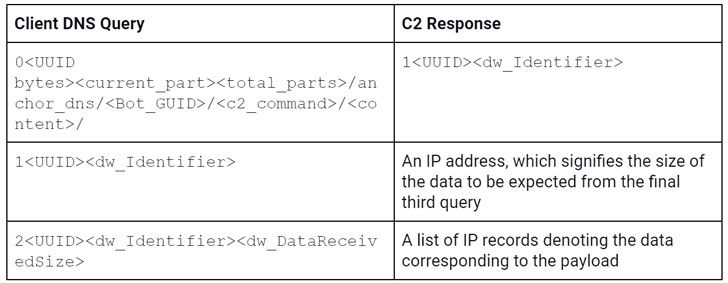
A checklist of IP data denoting the information corresponding to the payload
The end result of the third query is a listing of IP addresses that are subsequently parsed by the customer to develop the executable payload.
The last piece of facts despatched by the C2 server corresponds to a assortment of instructions (numbered -14 in Windows, and -4, 10-12, and 100 in Linux) for the bot to execute the payload through cmd.exe or by injecting it into many managing procedures these kinds of as Windows File Explorer or Notepad.
“The complexity of Anchor’s C2 communication and the payloads that the bot can execute replicate not only a portion of the Trickbot actors’ appreciable abilities, but also their potential to frequently innovate, as evidenced by their transfer to Linux,” De Souza explained.
Identified this report interesting? Adhere to THN on Fb, Twitter and LinkedIn to read through more exceptional information we put up.
Some pieces of this report are sourced from:
thehackernews.com

 Finnish psychotherapy center fires CEO for suppressing breach details
Finnish psychotherapy center fires CEO for suppressing breach details