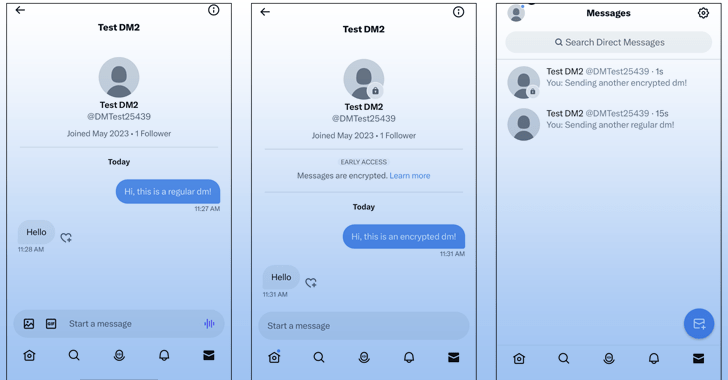
Twitter is formally commencing to roll out guidance for encrypted immediate messages (DMs) on the platform, a lot more than six months following its main executive Elon Musk verified plans for the attribute in November 2022.
The “Stage 1” of the initiative will surface as independent discussions alongside present immediate messages on users’ inboxes. Encrypted chats carry a lock icon badge to visually differentiate them.
That mentioned, the decide-in feature is now minimal to verified people or affiliate marketers to a confirmed group. It’s also important both equally the sender and recipient are on the most recent versions of the Twitter apps throughout Android, iOS, and desktop web.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
That stated, the element is at the moment minimal to verified buyers or affiliate marketers to a verified firm. It is really also vital both of those the sender and receiver are on the most current versions of the Twitter applications throughout Android, iOS, and desktop web.
An additional standards to send and get encrypted messages is that the receiver should comply with the sender, has despatched a message to the sender in the previous, or has approved a direct information request from the sender at some stage.
Although Twitter did not disclose the actual approach it employs to protected the messages, the corporation mentioned it employs a “blend of potent cryptographic schemes” to encrypt users’ messages, inbound links, and reactions.

It even further emphasised that the encrypted chat contents remain encrypted though stored on its infrastructure, which is then decrypted at the receiver’s end. The implementation is predicted to be open up sourced later on this calendar year.
That mentioned, the perform-in-development nature of the task also signifies that it does not guidance encrypted group conversations or trade media and other file attachments. Some other noteworthy limits are as follows –
- Consumers can only sign up a highest of up to 10 equipment to send and get encrypted messages.
- New products (where the Twitter app is re-set up) simply cannot partake in existing encrypted conversations
- Logging out from Twitter will phone calls all messages like encrypted DMs to be deleted from the present-day device
It also reported the current architecture does not “provide protections from male-in-the-middle attacks” and that it does not assure forward secrecy, a critical security evaluate that makes certain that a compromise of a one session crucial will not affect information shared in other periods.
“If the non-public important of a registered system was compromised, an attacker would be ready to decrypt all of the encrypted messages that have been despatched and been given by that device,” Twitter explained, introducing it does not plan to remediate the limitation trying to keep much larger consumer knowledge in brain.
Located this report interesting? Observe us on Twitter and LinkedIn to study much more exceptional written content we publish.
Some parts of this write-up are sourced from:
thehackernews.com

 GitHub Extends Push Protection to Prevent Accidental Leaks of Keys and Other Secrets
GitHub Extends Push Protection to Prevent Accidental Leaks of Keys and Other Secrets