Getty Photos
Ukraine’s unofficial ‘army’ of IT vigilantes has created a new automatic attack resource to enhance the effectiveness of its cyber attacks in opposition to Russian domains.
Its “attack automation bot” was crafted to aid a lot more folks easily launch dispersed denial of provider (DDoS) cyber attacks in opposition to Russia. The new tool encourages individuals to donate their cloud means to the bot, which is capable of launching a “coordinated attack from all the obtainable servers”.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“To run all our attacks at the very same time we advocate to use our new DDoS bot,” the team said on its web-site. “All you have to have is [to] send credentials to your servers to our bot and test how [the] attack is heading by way of Telegram bot.”
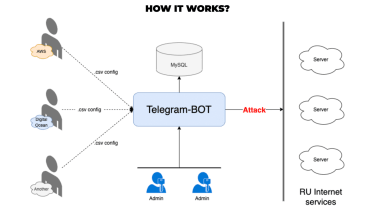
Really should they desire to, supporters are also encouraged to acquire and share the qualifications of new servers that can be acquired for the sole intent of strengthening the botnet’s attack.
The organised team of cyber-savvy persons who want to actively assist Ukraine from afar has been escalating in amount since the start off of the conflict. The team is assembled on Telegram and at this time has far more than 270,000 customers.
The group’s customers are fed guidance by leaders on a daily basis, comprehensive with IP addresses, specific ports, and web domains that need to be qualified to disrupt the Russian routine as the war continues.
Earlier targets have involved media organisations, financial institutions, airlines, and application suppliers.
Russian cyber attacks in opposition to Ukraine have been big and sustained, beginning weeks just before the conflict broke out.
The 5 Eye intelligence alliance verified past week that it thought with a superior diploma of assurance that Russia was at the rear of the attacks on Ukraine in the early stages of the war.
The attacks on Ukrainian authorities internet websites in January, which also associated the use of the destructive Whispergate ‘wiper’ malware, were attributed to Russia’s armed forces intelligence provider, the GRU, as was the 24 February attack on communications firm Viasat.
The attack on Viasat was carried out just one hour right before the Russia invasion of Ukraine turned official and it was afterwards discovered to have experienced results in wider Europe, as wind farms and specific internet buyers outdoors of Ukraine also endured outages.
The collateral results of the Viasat attack had been the most visceral illustrations of the ‘spillover effects’ lots of gurus thought would impact Europe in the ongoing war amongst Russia and Ukraine in cyber house.
Russia has a background of launching devastating attacks on Ukraine relationship back again many many years. Some of the most major incidents have included the use of Petya malware and recurring focusing on of the country’s power grid, to begin with in 2015, then all over again in 2016, and most not long ago in April 2022.
Some areas of this write-up are sourced from:
www.itpro.co.uk

 Google Russia files for bankruptcy, ends operations in the country
Google Russia files for bankruptcy, ends operations in the country