The U.S. Federal Bureau of Investigation (FBI) is warning that Barracuda Networks Email Security Gateway (ESG) appliances patched versus a lately disclosed critical flaw continue to be at risk of opportunity compromise from suspected Chinese hacking teams.
It also considered the fixes as “ineffective” and that it “carries on to observe active intrusions and considers all influenced Barracuda ESG appliances to be compromised and vulnerable to this exploit.”
Tracked as CVE-2023-2868 (CVSS score: 9.8), the zero-working day bug is claimed to have been weaponized as early as Oct 2022, far more than 7 months ahead of the security gap was plugged. Google-owned Mandiant is tracking the China-nexus action cluster beneath the title UNC4841.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The remote command injection vulnerability, impacting variations 5.1.3.001 as a result of 9.2..006, enables for unauthorized execution of process instructions with administrator privileges on the ESG solution.
In the attacks noticed so far, a effective breach functions as a conduit to deploy several malware strains this kind of as SALTWATER, SEASIDE, SEASPY, SANDBAR, SEASPRAY, SKIPJACK, WHIRLPOOL, and SUBMARINE (aka DEPTHCHARGE) that make it possible for for the execution of arbitrary instructions and defense evasion.
“The cyber actors utilized this vulnerability to insert destructive payloads onto the ESG appliance with a range of capabilities that enabled persistent access, email scanning, credential harvesting, and facts exfiltration,” the FBI stated.
The menace intelligence firm has characterised UNC4841 as the two aggressive and competent, demonstrating a aptitude for sophistication and immediately adapting their custom tooling to make use of additional persistence mechanisms and preserve their foothold into substantial priority targets.
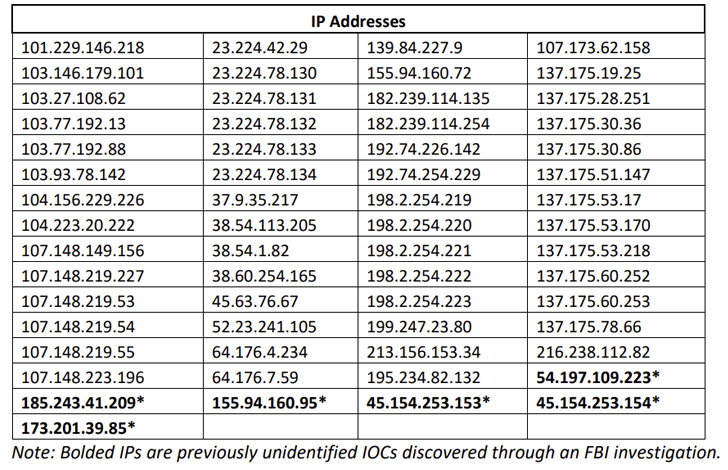
The federal company is recommending shoppers to isolate and swap all influenced ESG equipment with quick influence, and scan the networks for suspicious outgoing targeted traffic.
Discovered this posting attention-grabbing? Comply with us on Twitter and LinkedIn to read through extra unique articles we write-up.
Some elements of this report are sourced from:
thehackernews.com


 Lazarus Group Exploits Critical Zoho ManageEngine Flaw to Deploy Stealthy QuiteRAT Malware
Lazarus Group Exploits Critical Zoho ManageEngine Flaw to Deploy Stealthy QuiteRAT Malware