The threat actors behind the Vidar malware have produced alterations to their backend infrastructure, indicating makes an attempt to retool and conceal their on the net path in response to general public disclosures about their modus operandi.
“Vidar menace actors proceed to rotate their backend IP infrastructure, favoring companies in Moldova and Russia,” cybersecurity firm Workforce Cymru reported in a new evaluation shared with The Hacker News.
Vidar is a commercial data stealer that is regarded to be active considering the fact that late 2018. It’s also a fork of one more stealer malware called Arkei and is supplied for sale between $130 and $750 dependent on the membership tier.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Generally shipped as a result of phishing campaigns and web pages advertising and marketing cracked program, the malware arrives with a huge selection of abilities to harvest sensitive info from infected hosts. Vidar has also been observed to be distributed by means of rogue Google Ads and a malware loader dubbed Bumblebee.

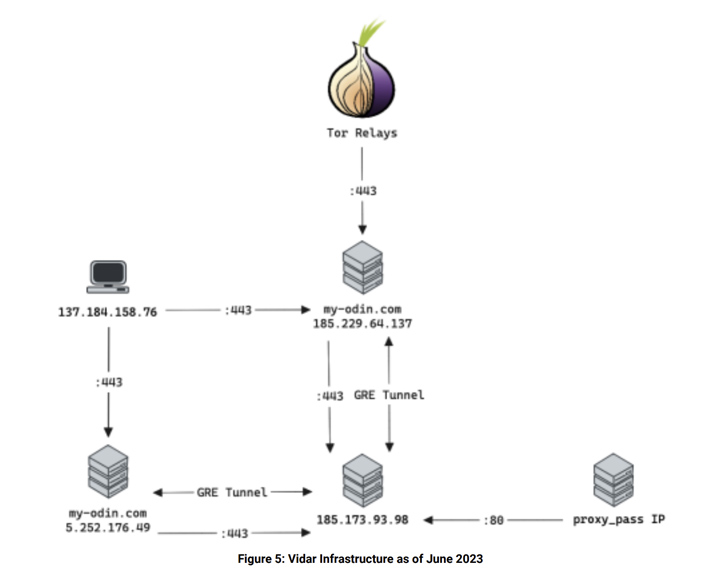
Workforce Cymru, in a report published previously January, observed that “Vidar operators have split their infrastructure into two areas a single focused to their typical consumers and the other for the administration staff, and also most likely quality / essential customers.”
A vital area utilised by the Vidar actors is my-odin[.]com, which serves as the one particular-halt vacation spot to manage the panel, authenticate affiliate marketers, and share information.
Although beforehand it was attainable to down load information from the web-site without the need of any authentication, executing the same motion now redirects the user to a login web page. A further modify includes updates to the IP deal with hosting the area alone.
This includes transferring from 186.2.166[.]15 to 5.252.179[.]201 to 5.252.176[.]49 by the stop of March 2023, with the menace actors accessing the latter using VPN servers about the similar time.
Approaching WEBINAR🔐 Mastering API Security: Knowing Your Accurate Attack Surface area
Find the untapped vulnerabilities in your API ecosystem and consider proactive techniques toward ironclad security. Be part of our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:just afterdisplay screen:inline-block.look at_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px sound #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-appropriate-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:followingwidth:50pxheight:6pxcontent:”border-top:2px reliable #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-weight:900text-align:leftline-peak:33px.wn-descriptiontextual content-align:leftfont-size:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-colour:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-excess weight:500letter-spacing:.2px
“By working with VPN infrastructure, which in at the very least aspect was also utilized by numerous other benign consumers, it is clear that the Vidar threat actors may perhaps be getting methods to anonymize their management activities by hiding in normal Internet sound,” Group Cymru observed.
The cybersecurity enterprise stated it also detected outbound connections from 5.252.176[.]49 to a genuine website named blonk[.]co as well as a host found in Russia (185.173.93[.]98:443).
The Vidar infrastructure has been uncovered to receive still one more facelift helpful May 3, 2023, with the introduction of a new IP handle 185.229.64[.]137 hosting the my-odin[.]com area along with the use of TOR relays by the operators to entry their accounts and malware repositories.
The conclusions “offers further more perception into the ‘behind-the-scenes’ operation of Vidar, demonstrating the evolution of its administration infrastructure as very well as proof of measures taken by the risk actors to perhaps deal with their tracks,” the corporation stated.
Found this post fascinating? Follow us on Twitter and LinkedIn to browse far more unique content material we publish.
Some elements of this post are sourced from:
thehackernews.com

 Warning: GravityRAT Android Trojan Steals WhatsApp Backups and Deletes Files
Warning: GravityRAT Android Trojan Steals WhatsApp Backups and Deletes Files