Exploiting Microsoft Trade ProxyLogon & ProxyShell vulnerabilities, attackers are malspamming replies in existing threads and slipping past destructive-email filters.
Attackers are gnawing on the ProxyLogon and ProxyShell vulnerabilities in Microsoft Trade Server to hijack email chains, by malspamming replies to ongoing email threads, researchers say.
What is however underneath discussion: Irrespective of whether the offensive is delivering SquirrelWaffle, the new email loader that showed up in September, or no matter if SquirrelWaffle is just a person piece of malware amongst many that the strategies are dropping.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Cisco Talos researchers to start with got wind of the SquirrelWaffle malspam campaigns commencing in mid-September, when they observed boobytrapped Microsoft Office environment paperwork providing Qakbot malware and the penetration-testing device Cobalt Strike – two of the most frequent threats on a regular basis observed targeting businesses all over the world. The Office files infected devices with SquirrelWaffle in the first phase of the an infection chain.
SquirrelWaffle strategies are recognized for employing stolen email threads to maximize the likelihood that a sufferer will click on malicious links. Individuals rigged backlinks are tucked into an email reply, comparable to how the virulent Emotet malware – normally spread by way of destructive email messages or text messages – has been regarded to operate.
Slipping Beneath People’s Noses
In a report posted on Friday, Development Micro researchers Mohamed Fahmy, Sherif Magdy and Abdelrhman Sharshar stated that hijacking email replies for malspam is a very good way to slip earlier the two people’s spam suspicions and to avoid acquiring flagged or quarantined by email gateways.
“Delivering the destructive spam making use of this procedure to get to all the internal area people will minimize the chance of detecting or halting the attack, as the mail [gateways] will not be able to filter or quarantine any of these inside e-mail,” they wrote.
The attacker also did not drop, or use, equipment for lateral movement following gaining accessibility to the susceptible Exchange servers, Development Micro said. Consequently, they remaining no tracks, as “no suspicious network functions will be detected. Additionally, no malware was executed on the Trade servers that will cause any alerts right before the destructive email is distribute throughout the natural environment.”
Middle East Campaign
Development Micro’s Incident Response crew had made the decision to look into what scientists believe are SquirrelWaffle-related intrusions in the Middle East, to figure out no matter if the attacks involved the notorious Trade server vulnerabilities.
They shared a display capture, shown underneath, that is consultant of the malicious email replies that showed up in all of the consumer inboxes of 1 afflicted network, all sent as genuine replies to current threads, all created in English.
They found that other languages were being applied in diverse locations exterior of the Center East attack they examined. Nevertheless, in the intrusions they analyzed that ended up outdoors of the Center East, most of the destructive emails were being prepared in English, in accordance to the report.

Destructive spam been given by targets. Resource: Pattern Micro.
“With this, the attackers would be equipped to hijack genuine email chains and send their malicious spam as replies to the reported chains,” the researchers wrote.
Who’s Powering This?
Cryptolaemus researcher TheAnalyst disagreed with Craze Micro on its premise that SquirrelWaffle is in fact acting as a malware dropper for Qbot or other malwares. Rather, TheAnalyst asserted on Friday that the danger actor is dropping equally SquirrelWaffle and Qbot as discrete payloads, and the most the latest confirmed SquirrelWaffle drop it has viewed was essentially on Oct. 26.
it will make it effortless for us who tracks them to detect them. A TTP they constantly arrives again to is back links to maldocs in stolen reply chains. They are regarded to provide a multitude of malware like #QakBot #Gozi #IcedID #CobaltStrike and possibly other individuals. >
— TheAnalyst (@ffforward) November 19, 2021
With regards to who’s guiding the action, TheAnalyst claimed that the actor/activity is tracked as tr01/TR (its QakBot affiliate ID) TA577 by Proofpoint and as ChaserLdr by Cryptolaemus and that the exercise goes back to at the very least 2020. The actors are straightforward to monitor, TheAnalyst reported, specified compact tweaks to their methods, strategies and techniques (TTPs).
One these TTP that tr01 favors is incorporating inbound links to destructive paperwork included in stolen reply chains, TheAnalyst observed. The threat actor is recognized to supply “a multitude of malware,” they mentioned, these types of as QakBot, Gozi, IcedID, Cobalt Strike and potentially more.
The Old ‘Open Me’ Excel Attachment Trick
The malicious email messages carried one-way links (aayomsolutions[.]co[.]in/etiste/quasnam[]-4966787 and aparnashealthfoundation[.]aayom.com/quasisuscipit/totamet[-]4966787) that dropped a .ZIP file containing a destructive Microsoft Excel sheet that downloads and executes a destructive DLL linked to the Qbot banking trojan.
What’s significantly notable, Trend Micro reported, is that true account names from the victim’s area had been applied as sender and recipient, “which raises the chance that a receiver will simply click the hyperlink and open the malicious Microsoft Excel spreadsheets,” in accordance to the report.
As proven underneath, the Excel attachment does what destructive Excel paperwork do: It prompts targets to choose “Enable Content” to view a guarded file.

Malicious Microsoft Excel doc. Source: Craze Micro.
Trend Micro available the chart down below, which exhibits the Excel file infection chain.
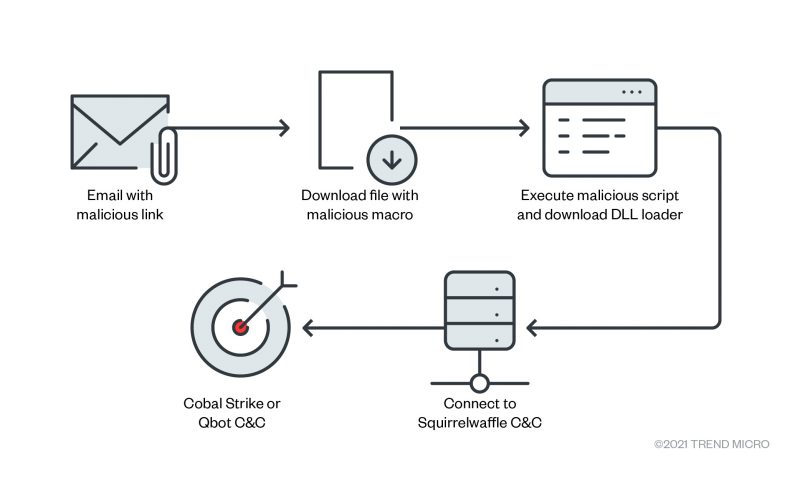
Excel file infection chain. Resource: Trend Micro.
The Exchange Inform-Tales
The scientists think that the actors are pulling it off by targeting people who are relying on Microsoft Trade servers that have not however been patched for the infamous, oft-picked-aside ProxyLogon and ProxyShell vulnerabilities.
Trend Micro discovered evidence in the IIS logs of three compromised Trade servers, every compromised in a independent intrusion, all having been exploited through the vulnerabilities CVE-2021-26855, CVE-2021-34473 and CVE-2021-34523 – the similar CVEs applied in ProxyLogon (CVE-2021-26855) and ProxyShell (CVE-2021-34473 and CVE-2021-34523) intrusions, in accordance to Development Micro.
The IIS log also showed that the threat actor is employing a publicly available exploit in its attack. “This exploit presents a menace actor the means to get users SID and emails” the researchers discussed. “They can even lookup for and down load a target’s e-mail.”
The scientists shared proof from the IIS logs, replicated below, that depicts the exploit code.
Exploiting CVE-2021-26855, as shown by the IIS logs. Source: Pattern Micro.
Microsoft preset the ProxyLogon vulnerabilities in March and the ProxyShell vulnerabilities in May possibly. These who’ve utilized the Might or July updates are secured from all of these. Microsoft has reiterated that all those who’ve used the ProxyLogon patch unveiled in March are not secured from ProxyShell vulnerabilities and must put in the far more recent security updates.
How to Fend Off ProxyLogon/ProxyShell Attacks
Exploiting ProxyLogon and ProxyShell enabled the attackers to slip previous checks for malicious email, which “highlights how customers [play] an vital portion in the results or failure of an attack,” Pattern Micro observed. These strategies “should make buyers cautious of the distinct ways used to mask malicious emails and data files,” the researchers wrote.
In other text, just mainly because email arrives from a trustworthy speak to is no ensure that any attachment or link it is made up of can be trusted, they said.
Of system, patching is the quantity one way to stay risk-free, but Development Micro gave these added recommendations if which is not doable:
- Permit digital patching modules on all Trade servers to offer critical level defense for servers that have not still been patched for these vulnerabilities.
- Use endpoint detection and reaction (EDR) remedies in critical servers, as it provides visibility to machine internals and detects any suspicious behavior operating on servers.
- Use endpoint security style and design for servers.
- Implement sandbox technology on email, network and web to detect comparable URLs and samples.
There’s a sea of unstructured info on the internet relating to the most up-to-date security threats. Sign-up Today to learn important concepts of normal language processing (NLP) and how to use it to navigate the details ocean and include context to cybersecurity threats (with no being an professional!). This Dwell, interactive Threatpost City Corridor, sponsored by Immediate 7, will aspect security scientists Erick Galinkin of Speedy7 and Izzy Lazerson of IntSights (a Swift7 corporation), moreover Threatpost journalist and webinar host, Becky Bracken.
Some sections of this report are sourced from:
threatpost.com


 Imunify360 Bug Leaves Linux Web Servers Open to Code Execution, Takeover
Imunify360 Bug Leaves Linux Web Servers Open to Code Execution, Takeover