An ongoing malvertising marketing campaign tracked as “Tag Barnakle” has been at the rear of the breach of additional than 120 advertisement servers around the earlier calendar year to sneakily inject code in an try to serve destructive advertisements that redirect customers to rogue internet sites, as a result exposing victims to scamware or malware.
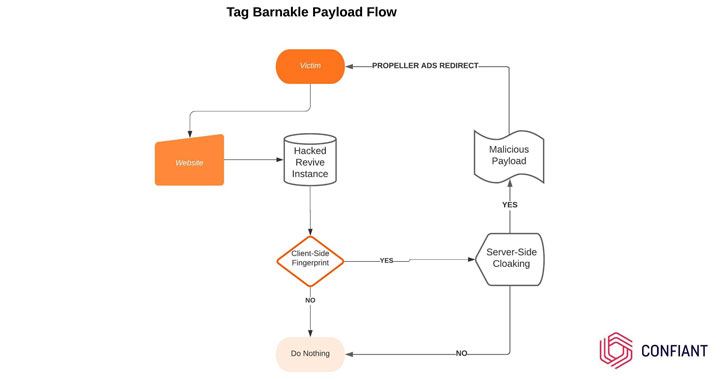
Not like other operators who set about their undertaking by infiltrating the advertisement-tech ecosystem utilizing “convincing personas” to invest in room on authentic internet websites for managing the destructive adverts, Tag Barnakle is “ready to bypass this preliminary hurdle completely by going straight for the jugular — mass compromise of advert serving infrastructure,” claimed Confiant security researcher Eliya Stein in a Monday create-up.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The progress follows a yr after the Tag Barnakle actor was located to have compromised nearly 60 advert servers in April 2020, with the infections mostly targeting an open up-resource advertising server called Revive.
The hottest slew of attacks is no distinctive, even though the adversaries look to have upgraded their equipment to focus on cell devices as perfectly. “Tag Barnakle is now pushing cell qualified campaigns, whilst final calendar year they were being happy to just take on desktop visitors,” Stein claimed.
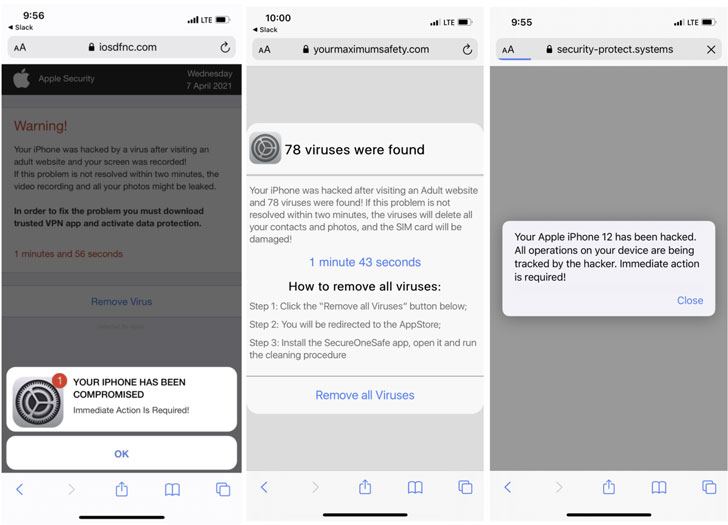
Specifically, the internet sites that acquire an ad by a hacked server carries out shopper-side fingerprinting to provide a 2nd-phase JavaScript payload — simply click tracker ads — when specified checks are contented, that then redirect users to destructive sites, aiming to entice the website visitors to an application keep listing for faux security, safety, or VPN applications, which appear with hidden membership charges or hijack the targeted visitors for other nefarious needs.

Provided that Revive is made use of by a superior variety of advertisement platforms and media businesses, Confiant pegs the get to of Tag Barnakle in the variety of “tens if not hundreds of thousands and thousands of products.”
“This is a conservative estimate that will take into consideration the point that they cookie their victims in order to expose the payload with lower frequency, possible to slow down detection of their presence,” Stein claimed.
Uncovered this post intriguing? Stick to THN on Facebook, Twitter and LinkedIn to study extra special information we put up.
Some parts of this short article are sourced from:
thehackernews.com

 Campus Still Closed as Portsmouth University Reels from Suspected Ransomware
Campus Still Closed as Portsmouth University Reels from Suspected Ransomware