Researchers have discovered 14 new kinds of cross-site details leakage attacks versus a variety of fashionable web browsers, which include Tor Browser, Mozilla Firefox, Google Chrome, Microsoft Edge, Apple Safari, and Opera, among the other people.
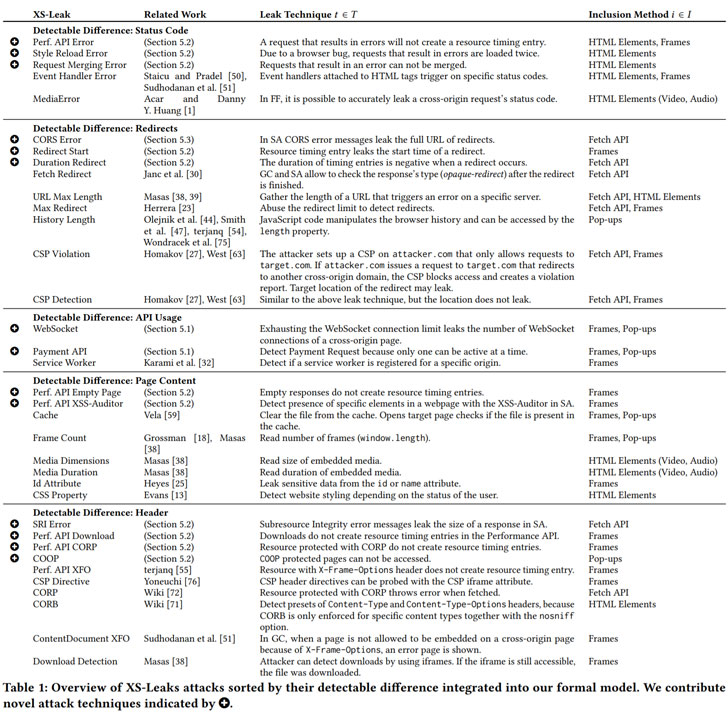
Collectively regarded as “XS-Leaks,” the browser bugs allow a destructive site to harvest personal details from its site visitors as they interact with other internet websites in the background without the need of the targets’ information. The findings are the outcome of a complete review of cross-web-site attacks carried out by a group of lecturers from Ruhr-Universität Bochum (RUB) and Niederrhein College.
“XS-Leaks bypass the so-termed exact-origin coverage, a single of a browser’s most important defences towards different styles of attacks,” the researchers explained in a assertion. “The function of the exact same-origin plan is to avoid details from staying stolen from a dependable site. In the case of XS-Leaks, attackers can nonetheless identify specific, little information of a internet site. If these information are tied to private details, these knowledge can be leaked.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Stemming from facet-channels designed into the web system that permits an attacker to acquire this facts from a cross-origin HTTP source, the cross-website bugs influence an array of well known browsers such as Tor, Chrome, Edge, Opera, Safari Firefox, Samsung Internet, spanning throughout various functioning techniques Windows, macOS, Android, and iOS.
The new class of vulnerabilities is also distinct from a cross-website request forgery (CSRF) attack in that unlike the latter, which exploits a web application’s believe in in a browser shopper to execute unintended actions on behalf of the user, they can be weaponized to infer information about a user.
“They are a important risk to Internet privacy because only browsing a web web site may possibly reveal if the victim is a drug addict or leak a sexual orientation,” the researchers spelled out. “XS-Leaks just take edge of tiny pieces of info which are uncovered for the duration of interactions concerning internet sites […] to reveal sensitive information and facts about buyers, this sort of as their knowledge in other web purposes, aspects about their local ecosystem, or interior networks they are related to.”
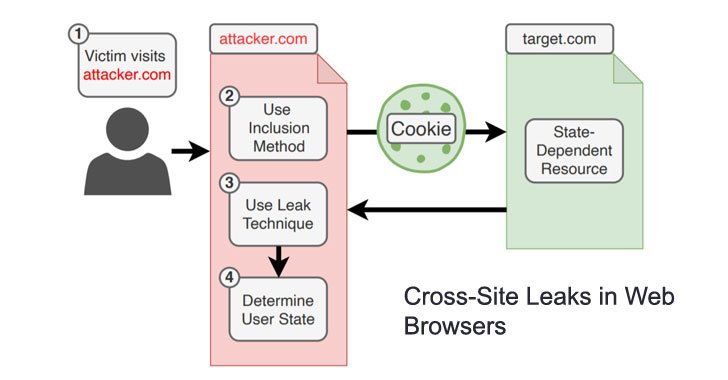
The core idea is that when sites are not allowed to directly obtain data (i.e., study server responses) on other web-sites for the reason that of similar-origin constraints, a rogue on-line portal can try to load a unique source or an API endpoint from a website, say, an online banking website, on the user’s browser and draw inferences about the victim’s transaction history. Alternatively, the supply of the leak could be timing-primarily based aspect-channels or speculative execution attacks like Meltdown and Spectre.

As mitigations, the scientists recommend denying all event handler messages, reducing mistake information occurrences, making use of world-wide limit limits, and producing a new heritage assets when redirection happens. At the conclude-user side, turning on initial-party isolation as very well as Enhanced Tracking Prevention in Firefox have been discovered to lessen the applicability of XS-Leaks. Smart Monitoring Prevention in Safari, which blocks third-party cookies by default, also helps prevent all leaks that are not based mostly on a pop-up.
“The root bring about of most XS-Leaks is inherent to the style and design of the web,” the scientists reported. “Quite often programs are vulnerable to some cross-internet site information leaks devoid of owning performed something completely wrong. It is hard to resolve the root result in of XS-Leaks at the browser degree simply because in many situations executing so would split present sites.”
Uncovered this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to browse extra exclusive information we post.
Some components of this post are sourced from:
thehackernews.com

 Pegasus Spyware Reportedly Hacked iPhones of U.S. State Department and Diplomats
Pegasus Spyware Reportedly Hacked iPhones of U.S. State Department and Diplomats