Google on Tuesday launched a new edition of Chrome web-browsing software package for Windows, Mac, and Linux with fixes for two security vulnerabilities, both of those of which it claims are beneath lively exploitation.
1 of the two flaws concerns an inadequate validation of untrusted input in its V8 JavaScript rendering engine (CVE-2021-21220), which was demonstrated by Dataflow Security’s Bruno Keith and Niklas Baumstark at the Pwn2Individual 2021 hacking contest final 7 days.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
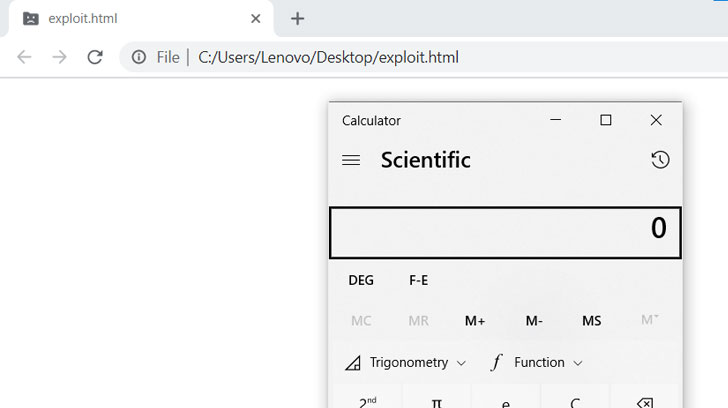
Though Google moved to correct the flaw swiftly, security researcher Rajvardhan Agarwal posted a working exploit in excess of the weekend by reverse-engineering the patch that the Chromium team pushed to the open up-resource component, a factor that could have played a important purpose in the launch.
Also fixed by the enterprise is a use-after-free vulnerability in its Blink browser engine (CVE-2021-21206). An nameless researcher has been credited with reporting the flaw on April 7.
“Google is informed of stories that exploits for CVE-2021-21206 and CVE-2021-21220 exist in the wild,” Chrome Complex Application Manager Prudhvikumar Bommana noted in a web site submit.
With this update, Google has set 5 flaws in Chrome that have been underneath attack given that the start of the 12 months, which includes CVE-2021-21148, CVE-2021-21166, and CVE-2021-21193.
Chrome 89..4389.128 is expected to roll out in the coming days. Users can update to the most recent edition by heading to Options > Help > About Google Chrome to mitigate the risk associated with the flaws.
Uncovered this write-up appealing? Stick to THN on Fb, Twitter and LinkedIn to read through a lot more special material we put up.
Some elements of this write-up are sourced from:
thehackernews.com


 NSA Discovers New Vulnerabilities Affecting Microsoft Exchange Servers
NSA Discovers New Vulnerabilities Affecting Microsoft Exchange Servers