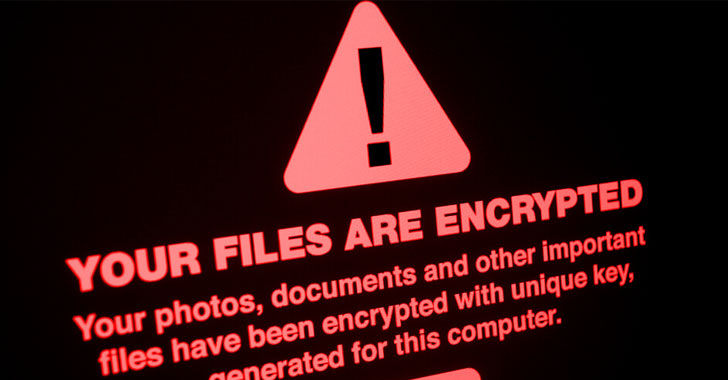
The new tsunami of ransomware has brought to lifetime the fears of downtime and information decline cybersecurity execs have warned about, as attacks on the power sector, food stuff offer chain, healthcare field, and other critical infrastructure have grabbed headlines.
For the marketplace specialists who track the evolution of this danger, the elevated frequency, sophistication, and destructiveness of ransomware suggests that firms nevertheless have some significant gaps in their defense techniques.
It’s no surprise that a new, multi-layered tactic to defense is necessary to stem the destruction induced by ransomware. But what alterations really should an IT team put into practice to close these gaps?

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
All through a current panel, a staff of cybersecurity professionals outlined a 3-stage plan to do just that — centered about embracing new technologies, enhancing security processes, and making certain their folks know how to aid control the risk.
1 — New Strains Overwhelm Old Defenses
Numerous new ransomware strains now act like innovative persistent threats (APTs), laying dormant in the corporate network for months, quietly accumulating data and thieving info.
This trend is why some analysts predict information exfiltration will overtake encryption as the favored approach of ransomware attackers.
Even with their change in solution, attackers even now rely on familiar techniques early in these attacks, these kinds of as phishing to steal credentials and inject malware. In fact, Topher Tebow, senior cybersecurity researcher at Acronis, says that 94% of thriving malware attacks now start out with phishing.
To deny attackers entry, he advises businesses to update their email security and deploy URL filtering if they experienced not already finished so. These defensive levels can block phishing email messages from achieving a user’s inbox and avert a malware payload from infecting the process. Simple tech investments like these, Tebow notes, can be an quick, helpful way to conclusion a ransomware attack right before it starts.
Dylan Pollock, a senior network engineer at NASCAR’s Hendrik Motorsports, provides that attackers also appreciate to goal recognised vulnerabilities that keep on being unpatched in buy to target operating systems, programs, and products. Unpatched vulnerabilities “are like catnip to cybercriminals,” which is why he endorses businesses take into account adopting instruments that can automate vulnerability scanning and patch management initiatives.
Organizations can not continue to depend only on signature-centered defenses to halt cyber threats.
That’s mainly because, as Acronis VP of Cyber Defense Analysis Candid Wüest factors out, cybercriminals are producing new versions of ransomware each and every day. That indicates every new attack is a zero-working day risk that regular signature-dependent defenses will miss.
Wüest suggests what corporations need to have is a lot more adaptive defenses that use behavioral-dependent detection to establish and cease threats. Options driven by device intelligence – the following stage of synthetic intelligence and machine understanding – that are adept at recognizing new designs of attack actions and quickly reply in genuine-time to mitigate the attack.
2 — Far better Procedures Prevent Ransomware
When using modern methods to defeat modern day threats is critical, upgraded defenses on your own are not enough in a globe where ransomware is regarded an inevitability by experts. The treatments corporations use to safeguard their information need to have to address that truth. “It cannot be overstated how important a very well-believed-out and religiously executed backup plan is as a last line of defense,” warns Graham Cluley.
A cybercrime researcher and host of the Smashing Security podcast, Cluley swiftly adds that backups by itself are not sufficient. Standard screening of these backups is necessary to assure they allow an group to restore immediately following an attack – normally, the company may perhaps stop up paying the ransom in any case.
When it arrives to analyzing procedures, Wüest provides that companies need to lock down all of the operational application used in their atmosphere. That’s since ransomware attackers progressively are using a “dwelling off the land” tactic, exactly where they hijack frequent equipment this sort of as RDP and Mimikatz to steal passwords, escalate privileges, and consider manage of remote desktop resources.
That will make stealing and encrypting data substantially less complicated. He suggests that in addition to limiting elevated privileges, providers really should implement arduous password treatments such as multi-factor authentication.
3 — Folks Aware of Ransomware Stay clear of It
Combatting ransomware falls down, while, if people are not concerned in defending the business. Security recognition training is as vital to endpoint security as is defensive technology. Just instruction finish-end users to acknowledge and steer clear of social engineering attempts could go a lengthy way to avoiding an attack from succeeding, advises Pollock.
“If we could get buyers to feel just two additional seconds before they simply click on a suspicious email, several ransomware attacks would never ever get a toehold in our organizations,” he mentioned.
Security groups have efficiently tailored to combat ransomware, but Cluley cautioned towards letting up on the fuel. Cybercriminals carry on to modify and advance their attacks, so companies have to regularly increase as well – deploying a number of levels of defense, making sure security awareness, and screening their incident reaction plan. Then, he said, “you can have a fighting prospect.”
Listen to these cybersecurity experts’ comprehensive tips in the recording of their Acronis virtual meeting panel, “See Within a Stay Ransomware Attack, Then Understand How to Reduce All of Them.”
Located this article appealing? Comply with THN on Fb, Twitter and LinkedIn to examine a lot more distinctive material we put up.
Some parts of this report are sourced from:
thehackernews.com

 Microsoft Discloses Critical Bugs Allowing Takeover of NETGEAR Routers
Microsoft Discloses Critical Bugs Allowing Takeover of NETGEAR Routers