Microsoft has awarded an independent security researcher $50,000 as section of its bug bounty method for reporting a flaw that could have allowed a malicious actor to hijack users’ accounts without the need of their know-how.
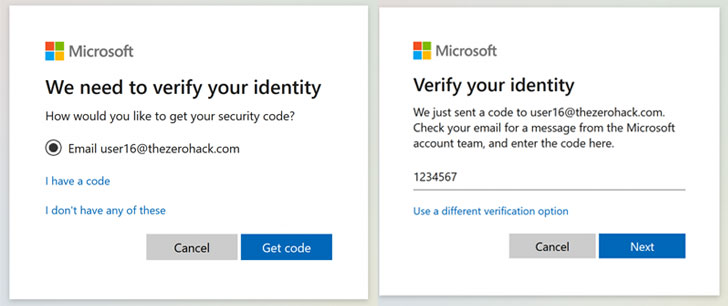
Noted by Laxman Muthiyah, the vulnerability aims to brute-pressure the seven-digit security code that is despatched to a user’s email deal with or cellular range to corroborate his (or her) id prior to resetting the password in purchase to get better obtain to the account.
Put differently, the account takeover circumstance is a consequence of privilege escalation stemming from an authentication bypass at an endpoint which is made use of to validate the codes despatched as element of the account recovery approach.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The firm addressed the issue in November 2020, prior to aspects of the flaw arrived to gentle on Tuesday.
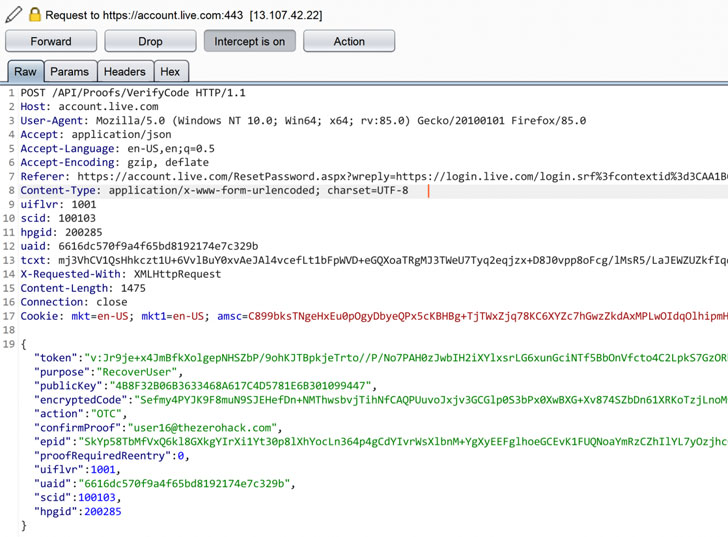
Though there are encryption obstacles and amount-limiting checks made to avert an attacker from continuously publishing all the 10 million combinations of the codes in an automatic vogue, Muthiyah claimed he eventually cracked the encryption purpose employed to cloak the security code and send out several concurrent requests.
Without a doubt, Muthiyah’s assessments showed that out of 1000 codes that ended up despatched, only 122 of them acquired as a result of, with the other individuals blocked with the mistake code 1211.
“I realized that they are blacklisting the IP handle [even] if all the requests we send really don’t hit the server at the same time,” the researcher reported in a compose-up, including that “a several milliseconds delay in between the requests allowed the server to detect the attack and block it.”
Subsequent this discovery, Muthiyah said he was capable to get all around the fee-limiting constraint and access the upcoming step of altering the password, thereby enabling him to hijack the account.
Although this attack only will work in cases where by the account is not secured by two-factor authentication, it can even now be extended to defeat the two layers of security and modify a target account’s password — a thing that could be prohibitive specified the amount of computing methods necessary to mount an attack of this sort.
“Putting all collectively, an attacker has to deliver all the possibilities of 6 and 7 digit security codes that would be around 11 million request makes an attempt and it has to be sent concurrently to alter the password of any Microsoft account (such as individuals with 2FA enabled),” Muthiyah explained.
Independently, Muthiyah also employed a comparable strategy to Instagram’s account recovery movement by sending 200,000 concurrent requests from 1,000 distinct equipment, obtaining that it was doable to obtain account takeover. He was rewarded $30,000 as part of the company’s bug bounty program.
“In a real attack circumstance, the attacker needs 5000 IP addresses to hack an account,” Muthiyah observed. “It seems significant but that is actually easy if you use a cloud company provider like Amazon or Google. It would expense all around 150 dollars to execute the finish attack of a person million codes.”
Discovered this short article intriguing? Stick to THN on Fb, Twitter and LinkedIn to examine a lot more exceptional information we post.
Some parts of this write-up are sourced from:
thehackernews.com

 BlueVoyant Appoints James M. Aquilina as Advisor
BlueVoyant Appoints James M. Aquilina as Advisor