A critical vulnerability has been disclosed in hardware random amount generators made use of in billions of Internet of Factors (IoT) units whereby it fails to properly make random numbers, so undermining their security and putting them at risk of attacks.
“It turns out that these ‘randomly’ picked figures are not normally as random as you would like when it arrives to IoT units,” Bishop Fox scientists Dan Petro and Allan Cecil stated in an investigation printed last week. “In simple fact, in several circumstances, equipment are picking encryption keys of or worse. This can guide to a catastrophic collapse of security for any upstream use.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
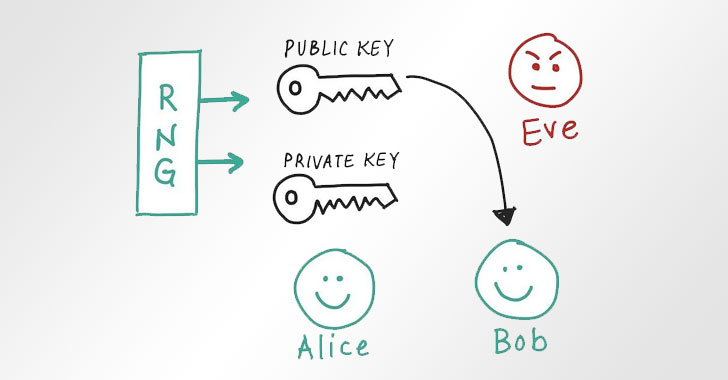
Random number era (RNG) is a essential approach that undergirds quite a few cryptographic purposes, like crucial era, nonces, and salting. On regular operating units, it’s derived from a cryptographically secure pseudorandom variety generator (CSPRNG) that employs entropy attained from a higher-good quality seed supply.
When it arrives to IoT equipment, this is supplied from a process-on-a-chip (SoC) that residences a committed hardware RNG peripheral identified as correct random amount turbines (TRNG) that is applied to capture randomness from actual physical procedures or phenomenа.
Stating that the fashion in which the peripheral is becoming current invoked was incorrect, the scientists pointed out the absence of checks for error code responses throughout the board, major to a scenario exactly where the random selection produced isn’t basically random, and worse, predictable, ensuing in partial entropy, uninitialized memory, and even crypto keys containing simple zeros.
“The HAL purpose to the RNG peripheral can fall short for a selection of causes, but by much the most prevalent (and exploitable) is that the gadget has operate out of entropy,” the researchers mentioned. “Hardware RNG peripherals pull entropy out of the universe through a variety of indicates (these types of as analog sensors or EMF readings) but don’t have it in infinite supply.
“They’re only able of making so many random bits for every 2nd. If you attempt contacting the RNG HAL purpose when it won’t have any random figures to give you, it will fall short and return an mistake code. Consequently, if the unit attempts to get also several random figures much too promptly, the phone calls will begin to fail.”

The challenge is exceptional to the IoT landscape as they lack an working method that usually will come with a randomness API (e.g., “/dev/random” in Unix-like OSes or BCryptGenRandom in Windows), with the scientists highlighting the more substantial entropy pool of a CSPRNG subsystem, thus taking away “any one details of failure among the the entropy sources.”
While the issues can be remediated with software program updates, the best alternative would be for IoT product manufacturers and builders to incorporate a CSPRNG API which is seeded from a set of varied entropy sources and assure the code would not ignore mistake situations, or are unsuccessful to block calls to the RNG when no a lot more entropy is obtainable.
“A single of the tricky parts about this vulnerability is that it really is not a uncomplicated situation of ‘you zigged wherever you must have zagged’ that can be patched effortlessly,” the researchers reported, stressing the need for utilizing CSPRNG in an IoT functioning technique. “In get to remediate this issue, a substantial and intricate aspect has to be engineered into the IoT unit.”
Identified this post appealing? Abide by THN on Fb, Twitter and LinkedIn to browse extra unique content we publish.
Some pieces of this article are sourced from:
thehackernews.com

 From zero to hero: The path to CIAM maturity
From zero to hero: The path to CIAM maturity