Cybersecurity researchers nowadays took the wraps off a advanced, multi-useful peer-to-peer (P2P) botnet published in Golang that has been actively focusing on SSH servers given that January 2020.
Known as “FritzFrog,” the modular, multi-threaded and file-much less botnet has breached additional than 500 servers to date, infecting nicely-regarded universities in the US and Europe, and a railway enterprise, in accordance to a report produced by Guardicore Labs these days.
“With its decentralized infrastructure, it distributes handle among all its nodes,” Guardicore’s Ophir Harpaz said. “In this network with no solitary stage-of-failure, peers constantly talk with each and every other to hold the network alive, resilient and up-to-day.”
In addition to implementing a proprietary P2P protocol which is been published from scratch, the communications are done over an encrypted channel, with the malware able of generating a backdoor on target methods that grants continued obtain for the attackers.
A Fileless P2P Botnet
Although GoLang based botnets have been observed ahead of, such as Gandalf and GoBrut, FritzFrog seems to share some similarities with Rakos, a different Golang-primarily based Linux backdoor that was previously located to infiltrate goal systems by means of brute force attempts at SSH logins.
But what can make FritzFrog exceptional is that it really is fileless, which means it assembles and executes payloads in-memory, and is far more intense in carrying out brute-drive assaults, even though also getting successful by distributing the targets evenly in just the botnet.
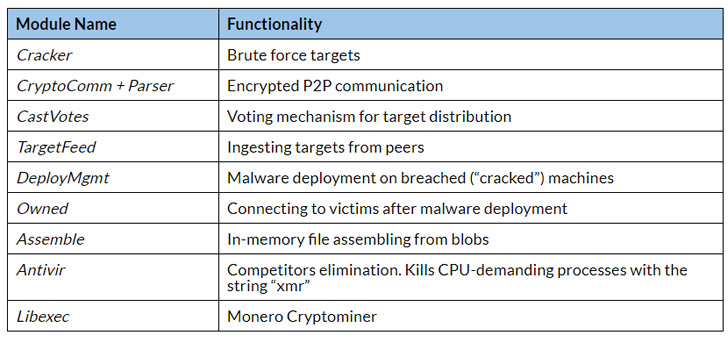
After a concentrate on machine is recognized, the malware performs a series of responsibilities involving brute-forcing it, infecting the equipment with malicious payloads upon a prosperous breach, and introducing the victim to the P2P network.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
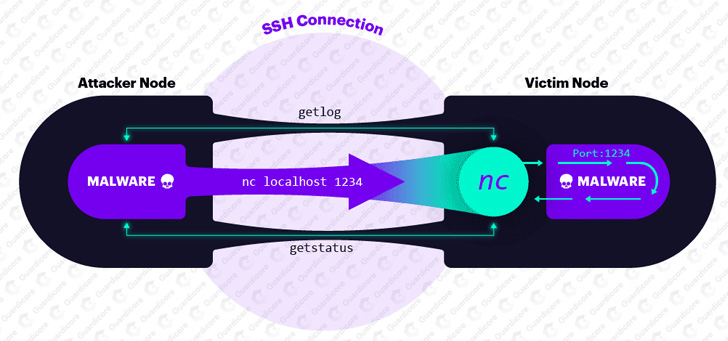
To slip less than the radar, the malware operates as ifconfig and NGINX, and commences listening on port 1234 to receive additional instructions for execution, such as people for syncing the target with the database of network friends and brute-pressure targets.
The commands by themselves are transmitted to the malware via a collection of hoops built to stay clear of detection. The attacker node in the botnet to start with latches on to a unique victim more than SSH and then works by using the NETCAT utility to create a connection with a remote server.
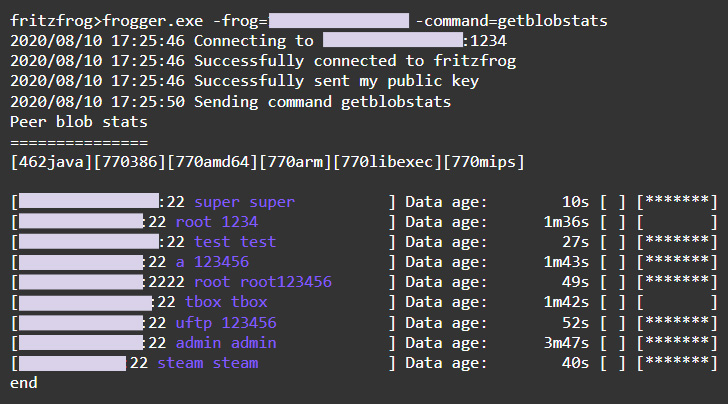
What is actually much more, the payload files are exchanged concerning nodes in BitTorrent-style, using a segmented file transfer strategy to mail blobs of details.
“When a node A wishes to receive a file from its peer, node B, it can query node B which blobs it owns using the command getblobstats,” Harpaz mentioned. “Then, node A can get a specific blob by its hash, both by the P2P command getbin or over HTTP, with the URL ‘https://node_IP:1234/blob_hash.’ When node A has all the required blobs, it assembles the file utilizing a unique module named Assemble and operates it.”
Apart from encrypting and encoding the command responses, the malware runs a independent course of action, named “libexec,” to mine Monero coins and leaves a backdoor for future entry to the sufferer by introducing a general public crucial to the SSH’s “licensed_keys” file so that logins can be authenticated without having owning to count on the password all over again.
13,000 Assaults Spotted Given that January
The campaign began on January 9, in accordance to the cybersecurity agency, before reaching a cumulative of 13,000 attacks considering the fact that its to start with visual appearance spanning throughout 20 distinctive versions of the malware binary.
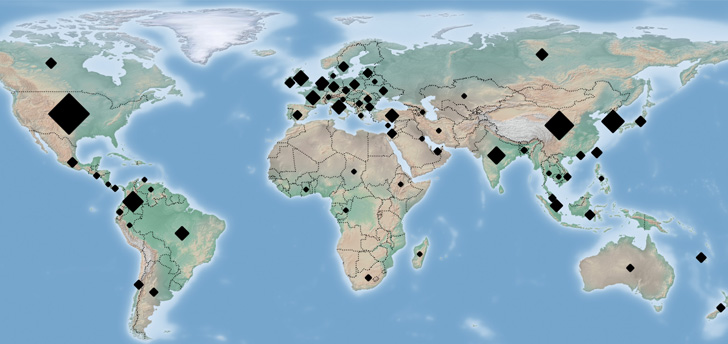
Aside from focusing on educational establishments, FritzFrog has been uncovered to brute-drive tens of millions of IP addresses belonging to governmental organizations, medical centers, banking companies, and telecom companies.
Guardicore Labs has also designed readily available a detection script that checks if a server has been contaminated by FritzFrog, together with sharing the other indicators of compromise (IoCs).
“Weak passwords are the fast enabler of FritzFrog’s attacks,” Harpaz concluded. “We advocate selecting strong passwords and employing public important authentication, which is a great deal safer. Routers and IoT products generally expose SSH and are so susceptible to FritzFrog — take into account transforming their SSH port or totally disabling SSH accessibility to them if the assistance is not in use.”
Observed this write-up intriguing? Follow THN on Fb, Twitter and LinkedIn to study additional distinctive articles we submit.


 Law enforcement and Sector Consider Down $42m “Bulletproof Exchange”
Law enforcement and Sector Consider Down $42m “Bulletproof Exchange”