Cybersecurity scientists on Tuesday took the wraps off a mass quantity email attack staged by a prolific cybercriminal gang impacting a large assortment of industries, with a single of its region-distinct operations notably focusing on Germany and Austria.
Enterprise security firm Proofpoint tied the malware campaign with higher self-assurance to TA505, which is the name assigned to the monetarily inspired danger group that’s been energetic in the cybercrime company because at the very least 2014, and is powering the infamous Dridex banking trojan and other arsenals of malicious resources these types of as FlawedAmmyy, FlawedGrace, Neutrino botnet, and Locky ransomware, among the other individuals.
The attacks are mentioned to have begun as a sequence of small-quantity email waves, providing only many thousand messages in every period, in advance of ramping up in late September and as not too long ago as October 13, ensuing in tens to hundreds of 1000’s of e-mail.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“A lot of of the campaigns, in particular the significant volume ones, strongly resemble the historic TA505 exercise from 2019 and 2020,” the researchers explained. “The commonalities involve identical area naming conventions, email lures, Excel file lures, and the shipping of the FlawedGrace distant entry trojan (RAT).”
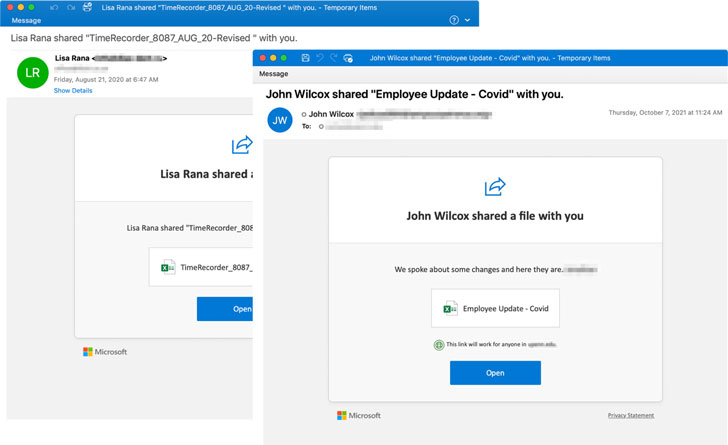
The team has a observe report of placing exploration institutes, banking companies, retail companies, electricity providers, healthcare institutions, airways, and governing administration businesses for gain-searching for motives, with the destructive activities commonly commencing upon opening malware-laced attachments in phishing messages purported to be connected to COVID-19 updates, insurance policies statements, or notifications about Microsoft OneDrive shared data files.
“More than time, TA505 evolved from a lesser partner to a experienced, self-subsisting and adaptable criminal offense operation with a wide spectrum of targets,” NCC Group said in an investigation revealed in November 2020. “Through the a long time the team closely relied on 3rd party products and services and tooling to support its fraudulent actions, even so, the group now largely operates independently from original an infection right until monetization.”
The achievement of the hottest marketing campaign, however, hinges on people enabling macros after opening the destructive Excel attachments, publish which an obfuscated MSI file is downloaded to fetch following-phase loaders prior to the delivery of an updated variation of the FlawedGrace RAT that incorporates assistance for encrypted strings and obfuscated API phone calls.
FlawedGrace — initial noticed in November 2017 — is a absolutely-featured remote obtain trojan (RAT) prepared in C++ that’s deliberately intended to thwart reverse-engineering and analysis. It comes with a roster of capabilities that allow for it to establish communications with a command-and-command server to get guidelines and exfiltrate the final results of those instructions back to the server.

The actor’s October attack wave is also major for its change in techniques, which contain the use of retooled intermediate loaders scripted in uncommon languages like Rebol and KiXtart in position of Get2, a downloader formerly deployed by the team to conduct reconnaissance, and obtain and install final-stage RAT payloads.
“TA505 is an recognized danger actor that is fiscally inspired and acknowledged for conducting malicious email strategies on a formerly unprecedented scale,” Proofpoint claimed. “The team regularly modifications their TTPs and are regarded trendsetters in the entire world of cybercrime. This threat actor does not limit its focus on established, and is, in actuality, an equivalent opportunist with the geographies and verticals it chooses to attack.”
“This merged with TA505’s capacity to be flexible, focusing on what is the most valuable and shifting its TTPs as necessary, make the actor a continued threat,” the cybersecurity agency added.
Found this posting intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read through far more unique written content we post.
Some sections of this post are sourced from:
thehackernews.com


 Kaspersky Internet Security review: Powerful, highly configurable protection
Kaspersky Internet Security review: Powerful, highly configurable protection