Cybersecurity researchers have uncovered several vulnerabilities in Dnsmasq, a well-liked open-source application utilised for caching Domain Identify Process (DNS) responses, thereby probably allowing an adversary to mount DNS cache poisoning attacks and remotely execute malicious code.
The flaws, collectively named “DNSpooq” by Israeli research firm JSOF, echoes earlier disclosed weaknesses in the DNS architecture, creating Dnsmasq servers powerless from a assortment of attacks.
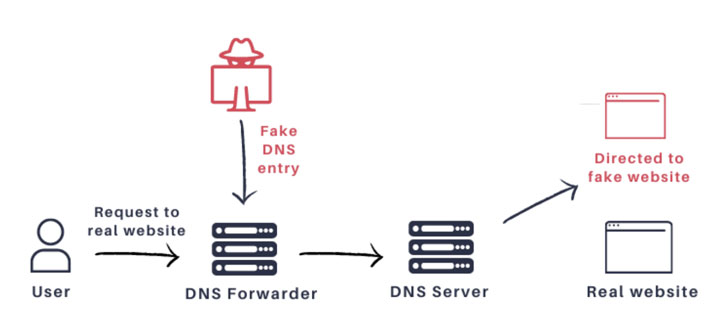
“We located that Dnsmasq is vulnerable to DNS cache poisoning attack by an off-route attacker (i.e., an attacker that does not observe the communication amongst the DNS forwarder and the DNS server),” the scientists observed in a report released now.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Our attack makes it possible for for poisoning of many domain names at the moment, and is a result of a number of vulnerabilities observed. The attack can be done properly beneath seconds or handful of minutes, and have no special demands. We also discovered that many instances of Dnsmasq are misconfigured to hear on the WAN interface, making the attack doable straight from the Internet.”
Dnsmasq, shorter for DNS masquerade, is a lightweight software for furnishing community DNS caching, consequently minimizing the load on upstream nameservers and bettering functionality.
As of September 2020, there ended up about 1 million susceptible Dnsmasq occasions, JSOF uncovered, with outstanding consumers becoming Cisco routers, Android smartphones, Aruba, Technicolor, Redhat, Siemens, Ubiquiti, and Comcast.
Revisiting Kaminsky Attack and Sad DNS
The idea of DNS cache poisoning is not new.
In 2008, security researcher Dan Kaminsky presented his conclusions of a widespread and critical DNS vulnerability that permitted attackers to start cache poisoning attacks towards most nameservers.
It exploited a basic style and design flaw in DNS — there can be only 65,536 feasible transaction IDs (TXIDs) — to flood the DNS server with cast responses, which is then cached and leveraged to route people to fraudulent websites.
The transaction IDs were released as a mechanism to thwart the likelihood that an authoritative nameserver could be impersonated to craft destructive responses. With this new set up, DNS resolvers hooked up a 16-bit ID to their requests to the nameservers, which would then ship back a reaction with the very same ID.
But the limitation in transaction IDs intended that when a recursive resolver queries the authoritative nameserver for a given domain (e.g., www.google.com), an attacker could flood the resolver with DNS responses for some or all of the 65 thousand or so probable transaction IDs.
If the destructive respond to with the appropriate transaction ID from the attacker arrives before the reaction from the authoritative server, then the DNS cache would be successfully poisoned, returning the attacker’s chosen IP tackle alternatively of the legit tackle for as lengthy as the DNS reaction was legitimate.
The attack banked on the point that the overall lookup approach is unauthenticated, that means there is no way to validate the identification of the authoritative server, and that DNS requests and responses use UDP (Consumer Datagram Protocol) rather of TCP, therefore generating it straightforward to spoof the replies.
To counter the difficulty, a randomized UDP port was utilised as a 2nd identifier together with the transaction ID, as opposed to just working with port 53 for DNS lookups and responses, as a result increasing the entropy in the buy of billions and creating it practically infeasible for attackers to guess the appropriate mixture of the source port and the transaction ID.
Whilst the success of cache poisoning attacks has taken a strike owing to the aforementioned supply port randomization (SPR) and protocols these as DNSSEC (Domain Identify Program Security Extensions), scientists final November identified a “novel” facet-channel to defeat the randomization by using ICMP amount boundaries as a side-channel to reveal irrespective of whether a provided port is open or not.
The attacks — named “Unfortunate DNS” or Aspect-channel AttackeD DNS — requires sending a burst of spoofed UDP packets to a DNS resolver, each individual despatched more than a different port, and subsequently working with ICMP “Port Unreachable” messages (or lack thereof) as an indicator to discern if the charge restrict has been achieved and finally slim down the specific supply port from which the ask for originated.
Mount Multi-Staged Attacks That Allow for Gadget Takeover
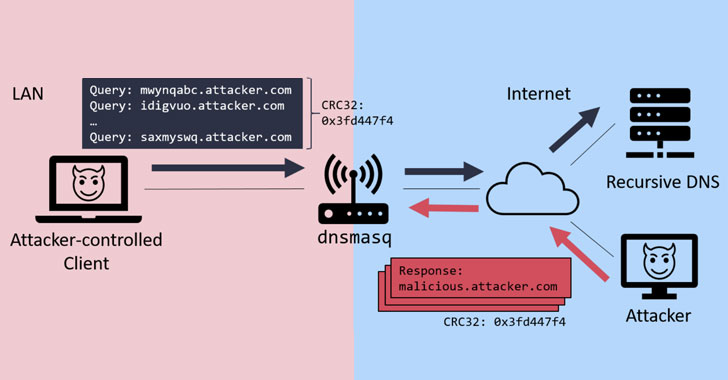
Apparently, the DNS cache poisoning attacks specific by JSOF bear similarities to Unhappy DNS in that the a few vulnerabilities (CVE-2020-25684, CVE-2020-25685, and CVE-2020-25686) aim to reduce the entropy of the Transaction IDs and source port that are required for a response to be approved.
Exclusively, the scientists observed that irrespective of Dnsmasq’s help for SPR, it “multiplexes several TXIDs on major of one port and does not backlink each port to details TXIDs,” and that the CRC32 algorithm applied for stopping DNS spoofing can be trivially defeated, main to a situation exactly where “the attacker wants to get any one of the ports right and any a person of the TXIDs right.”
Uncovered this article attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to read through much more exclusive material we put up.
Some elements of this report are sourced from:
thehackernews.com

 Most Financial Services Have Suffered COVID-Linked Cyber-Attacks
Most Financial Services Have Suffered COVID-Linked Cyber-Attacks