A North Korean hacking group has been uncovered deploying the RokRat Trojan in a new spear-phishing marketing campaign focusing on the South Korean government.
Attributing the attack to APT37 (aka Starcruft, Ricochet Chollima, or Reaper), Malwarebytes explained it identified a malicious doc final December that, when opened, executes a macro in memory to set up the aforementioned remote entry device (RAT).
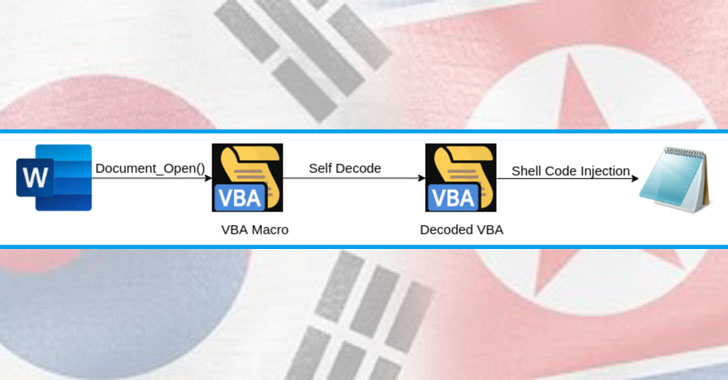
“The file incorporates an embedded macro that makes use of a VBA self decoding technique to decode by itself in the memory areas of Microsoft Place of work with out crafting to the disk. It then embeds a variant of the RokRat into Notepad,” the researchers pointed out in a Wednesday assessment.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Considered to be active at the very least because 2012, the Reaper APT is known for its emphasis on public and non-public entities primarily in South Korea, this sort of as chemical substances, electronics, production, aerospace, automotive, and healthcare entities. Due to the fact then, their victimization has expanded beyond the Korean peninsula to include Japan, Vietnam, Russia, Nepal, China, India, Romania, Kuwait, and other components of the Middle East.
Whilst the past attacks leveraged malware-laced Hangul Word Processor (HWP) paperwork, the use of self-decoding VBA Office environment files to produce RokRat suggests a improve in practices for APT37, the researchers said.
The Microsoft VBA document uploaded to VirusTotal in December purported to be a conference request dated January 23, 2020, implying that attacks took area just about a yr in the past.
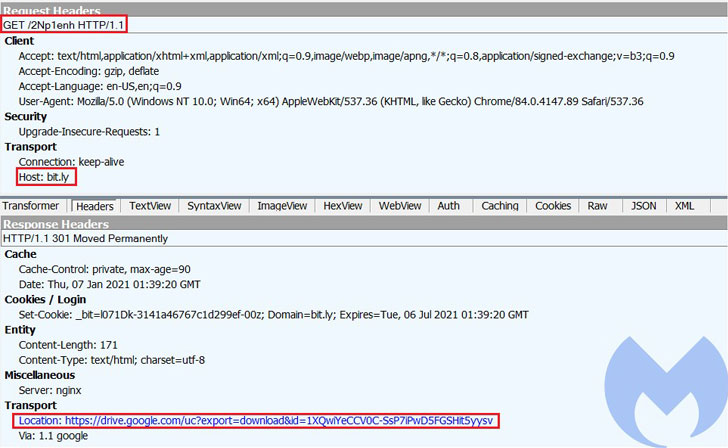
Main amid the obligations of the macro embedded in the file is to inject shellcode to a Notepad.exe process that downloads the RokRat payload in encrypted structure from a Google Drive URL.
RokRat — first publicly documented by Cisco Talos in 2017 — is a RAT of decision for APT37, with the team employing it for a range of strategies due to the fact 2016. A Windows-centered backdoor distributed through trojanized documents, it is capable of capturing screenshots, logging keystrokes, evading analysis with anti-virtual machine detections, and leveraging cloud storage APIs these kinds of as Box, Dropbox, and Yandex.
In 2019, the cloud service-dependent RAT gained extra features to steal Bluetooth system information as element of an intelligence-accumulating effort directed from financial commitment and trading organizations in Vietnam and Russia and a diplomatic agency in Hong Kong.
“The circumstance we analyzed is a single of the few the place they did not use HWP information as their phish documents and alternatively utilised Microsoft Business office paperwork weaponized with a self decode macro,” the researchers concluded. “That method is a intelligent option that can bypass several static detection mechanisms and hide the major intent of a destructive document.”
Uncovered this write-up exciting? Adhere to THN on Fb, Twitter and LinkedIn to study more exclusive content we article.
Some components of this report are sourced from:
thehackernews.com

 Bugs in Firefox, Chrome, Edge Allow Remote System Hijacking
Bugs in Firefox, Chrome, Edge Allow Remote System Hijacking