A formerly undocumented malware downloader has been spotted in the wild in phishing attacks to deploy credential stealers and other destructive payloads.
Dubbed “Saint Bot,” the malware is said to have first appeared on the scene in January 2021, with indications that it is below active enhancement.
“Saint Bot is a downloader that appeared very recently, and bit by bit is getting momentum. It was noticed dropping stealers (i.e. Taurus Stealer) or even further loaders (illustration), still its design makes it possible for [it] to make use of it for distributing any type of malware,” mentioned Aleksandra “Hasherezade” Doniec, a danger intelligence analyst at Malwarebytes.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Also, Saint Bot employs a wide wide variety of techniques which, whilst not novel, point out some stage of sophistication taking into consideration its somewhat new visual appearance.”
The infection chain analyzed by the cybersecurity organization begins with a phishing email that contains an embedded ZIP file (“bitcoin.zip”) that claims to be a bitcoin wallet when, in truth, it is a PowerShell script under the guise of .LNK shortcut file. This PowerShell script then downloads the next phase malware, a WindowsUpdate.exe executable, which, in turn, drops a next executable (InstallUtil.exe) that can take care of downloading two extra executables named def.exe and putty.exe.
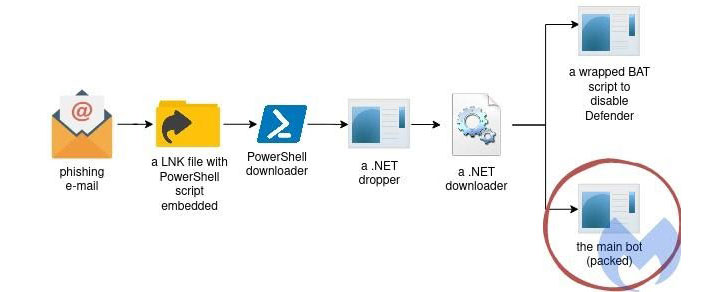
Although the previous is a batch script dependable for disabling Windows Defender, putty.exe contains the malicious payload that at some point connects to a command-and-regulate (C2) server for further exploitation.
The obfuscation present in each and every phase of the infection, coupled with the anti-evaluation tactics adopted by the malware, makes it possible for the malware operators to exploit the products they were being set up on without the need of attracting consideration.
Aside from accomplishing “self defense checks” to confirm the existence of a debugger or a digital environment, Saint Bot is designed to not execute in Romania and pick out nations inside the Commonwealth of Unbiased States (CIS), which incorporates Armenia, Belarus, Kazakhstan, Moldova, Russia, and Ukraine.
The record of instructions supported by the malware contain —
- downloading and executing other payloads retrieved from the C2 server
- updating the bot malware, and
- uninstalling by itself from the compromised machine
Whilst these capabilities might feel quite little, the simple fact that Saint Bot serves as a downloader for other malware tends to make it hazardous sufficient.
Apparently, the payloads are on their own fetched from information hosted on Discord, a tactic that has develop into more and more prevalent between menace actors, who are abusing respectable functions of this sort of platforms for C2 communications, evade security, and supply malware.
“When documents are uploaded and saved in just the Discord CDN, they can be accessed using the hardcoded CDN URL by any method, no matter of irrespective of whether Discord has been put in, just by browsing to the CDN URL wherever the material is hosted,” scientists from Cisco Talos disclosed in an evaluation previously this 7 days, consequently turning application like Discord and Slack into lucrative targets for hosting destructive articles.
“Saint Bot is yet an additional very small downloader,” Hasherezade stated. “”[It is] not as experienced as SmokeLoader, but it is really new and now actively developed. The author would seem to have some information of malware layout, which is noticeable by the huge array of strategies utilised. Nevertheless, all the deployed procedures are properly-identified and very normal, [and] not demonstrating significantly creativeness so far.”
Observed this short article fascinating? Observe THN on Facebook, Twitter and LinkedIn to read additional unique written content we write-up.
Some components of this report are sourced from:
thehackernews.com


![[whitepaper] how to achieve cmmc security compliance for your business](https://thecybersecurity.news/data/2021/04/WHITEPAPER-How-to-Achieve-CMMC-Security-Compliance-for-Your-Business-80x80.jpg) [WHITEPAPER] How to Achieve CMMC Security Compliance for Your Business
[WHITEPAPER] How to Achieve CMMC Security Compliance for Your Business