New vulnerabilities have been discovered in Fortress S03 Wi-Fi Residence Security System that could be probably abused by a destructive party to gain unauthorized accessibility with an intention to change technique behavior, together with disarming the products with out the victim’s know-how.
The two unpatched issues, tracked less than the identifiers CVE-2021-39276 (CVSS rating: 5.3) and CVE-2021-39277 (CVSS rating: 5.7), have been identified and noted by cybersecurity agency Fast7 in May 2021 with a 60-working day deadline to repair the weaknesses.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Fortress S03 Wi-Fi Home Security Method is a do-it-you (Diy) alarm program that allows customers to safe their residences and small corporations from burglars, fires, fuel leaks, and drinking water leaks by leveraging Wi-Fi and RFID technology for keyless entry. The firm’s security and surveillance programs are employed by “countless numbers of clientele and ongoing consumers,” in accordance to its website.
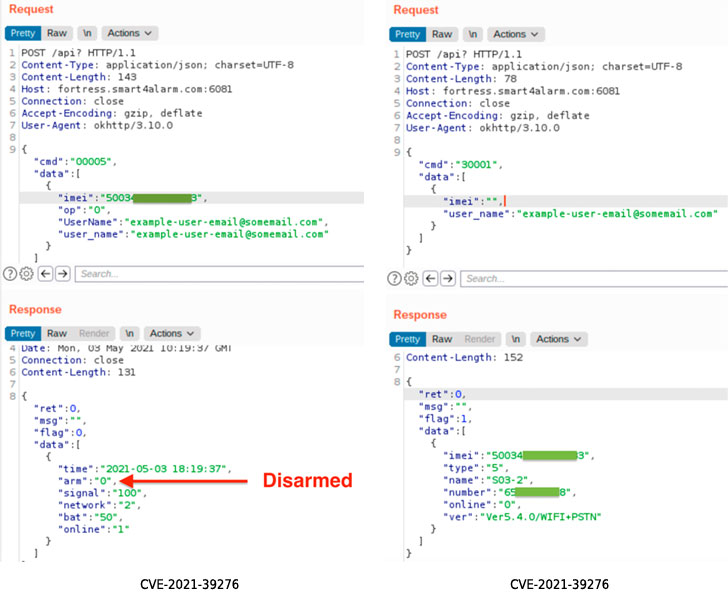
Contacting the vulnerabilities “trivially simple to exploit,” Quick7 scientists famous CVE-2021-39276 issues an unauthenticated API Obtain that enables an attacker in possession of a victim’s email address to question the API to leak the device’s Worldwide Cellular Tools Id (IMEI) selection, which also doubles up as the serial variety. Armed with the device’s IMEI variety and the email deal with, the adversary can progress to make a amount of unauthorized variations, this kind of as disabling the alarm program by means of an unauthenticated Put up ask for.
CVE-2021-39277, on the other hand, relates to an RF Sign replay attack, whereby a absence of adequate encryption grants the poor actor the capability to seize the radio frequency command and handle communications around the air working with application-defined radio (SDR), and playback the transmission to complete specific features, these types of as “arm” and “disarm” operations, on the concentrate on product.
“For CVE-2021-39276, an attacker with the expertise of a Fortress S03 user’s email handle can very easily disarm the put in home alarm without having that user’s expertise,” the researchers explained in a report shared with The Hacker Information.
“CVE-2021-39277 offers identical problems, but involves less prior expertise of the victim, as the attacker can simply just stake out the home and wait for the victim to use the RF-controlled gadgets inside radio selection. The attacker can then replay the ‘disarm’ command later, with no the victim’s expertise.”

Fast7 mentioned it notified Fortress Security of the bugs on May well 13, 2021, only for the firm to close the report 11 days afterwards on May perhaps 24. We have attained out to Fortress Security for comment, and we will update the story if we listen to again.
In gentle of the actuality that the issues continue on to persist, it really is advised that people configure their alarm units with a exceptional, a person-time email handle to function close to the IMEI amount exposure.
“For CVE-2021-39277, there seems to be pretty minimal a person can do to mitigate the consequences of the RF replay issues absent a firmware update to implement cryptographic controls on RF alerts. Buyers concerned about this exposure need to prevent using the crucial fobs and other RF gadgets connected to their household security methods,” the researchers reported.
Discovered this post attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to go through much more distinctive content material we submit.
Some elements of this article are sourced from:
thehackernews.com


 Ransomware May Have Cost US Schools Over $6bn in 2020
Ransomware May Have Cost US Schools Over $6bn in 2020