An effective cybersecurity method can be difficult to implement properly and typically requires many levels of security. Aspect of a sturdy security strategy will involve doing what is recognised as a penetration check (pen check). The penetration test aids to find out vulnerabilities and weaknesses in your security defenses prior to the poor men discover these. They can also enable validate remedial efforts and answers set in put to prevail over earlier identified security vulnerabilities.
Let us appear far more carefully at the pen exam. What is included in a penetration exam? How are they done, and by whom? What measures need to be taken following a penetration exam?
What is a penetration exam?
1 — Simulated cyberattack

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A penetration test is, for all practical functions, a simulated cyberattack on your business enterprise. Having said that, it is carried out by the “good men.” An outside useful resource usually conducts a penetration exam, no matter if a 3rd-party security consulting company or one more security entity. Security consultants typically have the security expertise and are remaining existing with practices and techniques applied by present-day threat actors.
2 — Organized beforehand
Penetration tests are arranged with a security specialist times or weeks in progress. Right before the penetration take a look at will take area, there is commonly an engagement get in touch with to understand the scope of the penetration exam. Pen checks can be general or can be centered on a precise location or technology for a lot more thorough tests. When arranging for a pen take a look at, a scoping contact will aid build the specifics of the penetration testing and the scope of vulnerabilities staying examined.
3 — Build rules to reduce disrupting enterprise-critical routines
There is always a likelihood when stressing output infrastructure to cause issues with company-critical manufacturing actions. So, though it is great with a pen test to examination from your production infrastructure to assure all potential cybersecurity vulnerabilities are observed, it is also excellent to establish boundaries. For instance, there may perhaps want to be “blackout” durations wherever no disruptive pen tests or intrusive things to do arise.
4 — Create cybersecurity aims for the pen examination
There are numerous factors for accomplishing a pen check. These can array from compliance specifications, general bolstering of cybersecurity defenses, setting up a security baseline, validating security improvements or new cybersecurity implementations, and numerous other folks.
The business carrying out the pen test will typically get info needed for the pen take a look at. This information and facts could contain network names, resources, pertinent person accounts, and other facts expected to simulate regime day-to-day workflows. These are utilised to validate the security steps, opportunity escalation of privileges, weak cybersecurity controls, and other discovery duties.
5 — Stages of the pen test
The levels of a pen exam can include things like but are not confined to the subsequent:
- Scope of work, reconnaissance – The plans and scope of the pen check are founded, and preliminary reconnaissance is carried out
- Automatic pen testing – Automatic scanners and other tools may perhaps initially be utilized to locate open up ports, vulnerabilities, and other weaknesses
- Manual pen tests – Matter make any difference professionals may possibly manually perform certain attacks from recognised systems and methods.
- The exploitation of vulnerabilities – If a vulnerability is identified, the scope of the vulnerability will be assessed. How far-achieving is the vulnerability? What is criticality?
- Examination and report – Pen testers will generally produce an analysis of the pen check success, position the criticality of any vulnerabilities observed. The moment these are analyzed, a report is usually a portion of the deliverables from the pen take a look at.
Leading-rated penetration tests companies
According to Cybersecurity Ventures, the pursuing organizations give top-rated penetration tests expert services:
- BreachLock
- Bugcrowd
- CrowdStrike
- HackerOne
- ImmuniWeb
- Mitnick Security
- Offensive Security
- Raxis
- SecureLayer7
- Synack
Search for dependable pen examination corporations with a good observe report that aligns with your business enterprise.
Ways to acquire following a penetration test
1 — Consider and critique the pen check effects
Commonly, a person of the deliverables with a pen take a look at is a in depth report of any conclusions in the ecosystem. These reports supply companies with the vital details to transfer forward with any remediations important to shut significant or critical security gaps. It also aids firms with bolstering their total cybersecurity posture.
In addition, as lots of compliance laws involve evidence of penetration screening, the shipping and delivery of the pen take a look at report offers the documentation desired for compliance audits if asked for.
The pen test final results eventually deliver corporations with the data wanted to enable guarantee any chinks in their cybersecurity armor are solved with the suitable actions and cybersecurity answers if needed. In addition, if it is the first pen examination done for the firm, it can help build the security baseline that is a commencing level for enhancement. Each and every subsequent pen exam can then gauge the development of strengthening overall security.
2 — Remediate results from the pen examination
Pen exam results normally are prioritized dependent on the criticality or chance the discovered vulnerability will be exploited. Nonetheless, it is also sensible for organizations to study the probable repercussions of a thriving exploit on the small business. In other words, how big would it be for the company if a particular vulnerability is exploited? What methods would be impacted? How will enterprise continuity be affected?
Companies can use the prioritization of any security results in the pen examination report to prioritize the remediation of the vulnerabilities. Nonetheless, the selection and criticality of pen test findings might influence the time desired to remediate the conclusions.
3 — Repeat the course of action
Cybersecurity is consistently changing. New threats and hazards surface on the scene each and every working day. As a final result, bolstering cybersecurity defenses and posture is under no circumstances-ending. Pen checks are part of the all round procedure essential to keep on examining for vulnerabilities in the ecosystem. Scheduling frequent pen assessments of the natural environment allow for gaining visibility to new exploits or new results that could not have existed when the very last pen examination was carried out.
With just about every pen examination, the approach carries on to repeat. Enterprises prioritize the conclusions, master from these, and remediate the issues based on the criticality and importance assigned. Executing pen checks regularly aids to assure cybersecurity is not an afterthought, but instead it is a normal part of the total risk evaluation approach.
Qualifications and pen tests
Pen test firms usually inquire for valid credentials to entry your ecosystem. It may possibly include credentialed sources. Why? It assists drop mild on any likely for entry to knowledge they shouldn’t have or other risks. 2nd, attackers frequently attack environments applying legitimate qualifications.
In truth, in accordance to the IBM Price of a Data Breach Report 2021:
Compromised qualifications were being the most popular first attack vector, responsible for 20% of breaches.
They also consider the longest to determine and consist of:
Breaches brought on by stolen/compromised qualifications took the longest quantity of days to establish (250) and comprise (91) on ordinary, for an regular full of 341 days.
Currently, organizations ought to have solid password policies to enable defend versus weak or overused passwords and actively secure their surroundings from breached passwords. How can this be finished properly?
Specops Password Plan presents solid Lively Directory password guidelines, allowing businesses to extend the Energetic Directory password policy capabilities considerably beyond what is incorporated by default. In addition, with Specops Breached Password Protection, companies obtain continuous protection from breached passwords, encouraging corporations to defend from conclusion-customers applying passwords located on breach password lists.
Specops Breached Password Safety also shields from newly found out passwords using brute power or password spraying. Specops integrates recently identified breached passwords into the Breached Password Security module making use of its network of honeypots throughout the world that capture breached password telemetry info. The data collected is used to bolster the Breached Password defense provided in Specops Password Coverage.
Breached Password Defense Express checklist can:
- Avoid people from transforming to a leaked password
- Continuously examine for leaked passwords and force people to improve them
- Notify end users if passwords develop into breached, and they have to have to transform their password
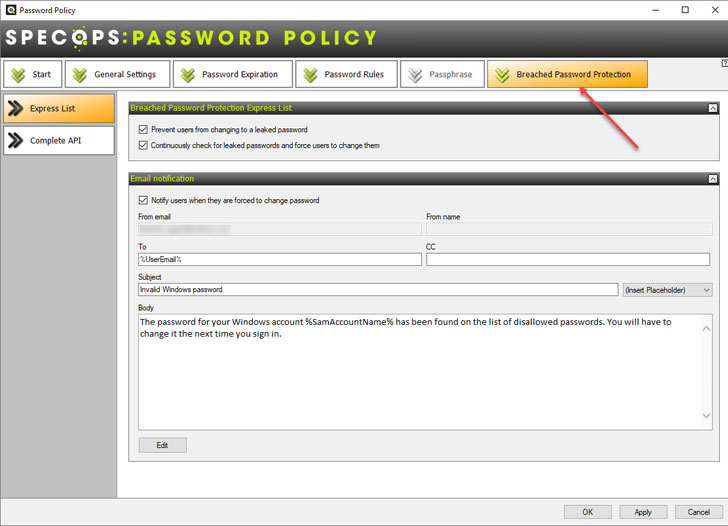 Specops Breached Password Security
Specops Breached Password Security
In addition to the Express List, the Specops Total API solution offers more abilities.
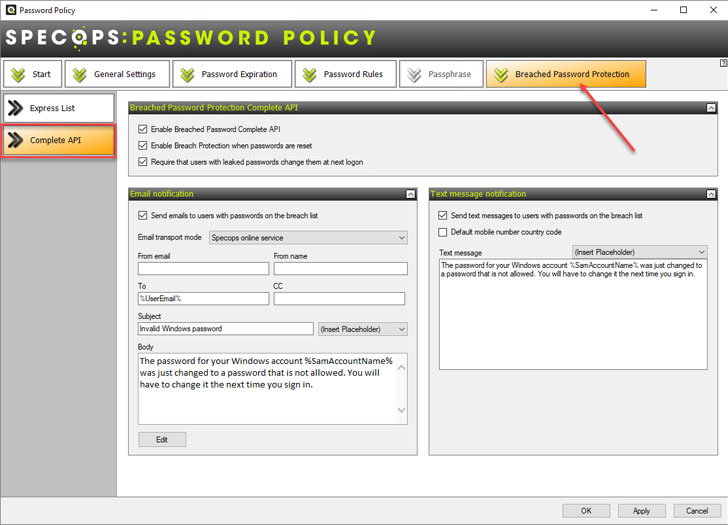 Specops Breached Password Protection Entire API
Specops Breached Password Protection Entire API
As pen tests usually show, credentialed obtain can have a lot more privileges than desired or obtain to information they should not have. On top rated of making certain the least privileged accessibility for end users, organizations ought to secure passwords in the surroundings with strong password guidelines and breached password defense. Study far more about Specops Password Policy tools and see how you can bolster Lively Listing password protection in your surroundings.
Uncovered this report exciting? Observe THN on Facebook, Twitter and LinkedIn to read more distinctive material we write-up.
Some areas of this post are sourced from:
thehackernews.com


 Gigabyte Allegedly Hit by AvosLocker Ransomware
Gigabyte Allegedly Hit by AvosLocker Ransomware