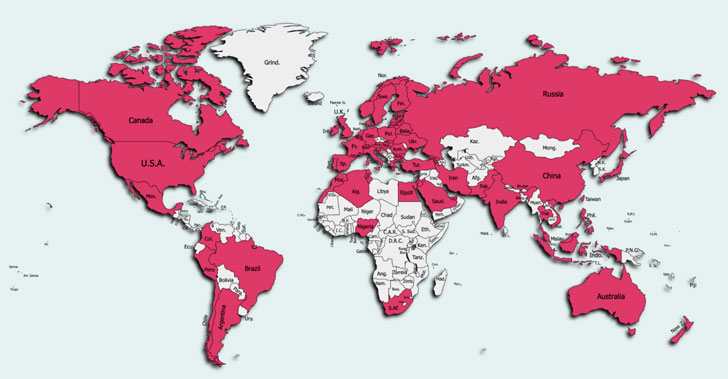
A freshly found “intense” cellular marketing campaign has contaminated north of 10 million consumers from around 70 countries via seemingly innocuous Android applications that subscribe the people to premium solutions costing €36 (~$42) for each thirty day period with no their expertise.
Zimperium zLabs dubbed the destructive trojan “GriftHorse.” The dollars-producing scheme is thought to have been underneath active enhancement starting from November 2020, with victims documented throughout Australia, Brazil, Canada, China, France, Germany, India, Russia, Saudi Arabia, Spain, the U.K., and the U.S.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
No less than 200 trojan purposes had been used in the marketing campaign, earning it a person of the most prevalent scams to have been uncovered in 2021. What is actually much more, the destructive apps catered to a diversified established of types ranging from Equipment and Amusement to Personalization, Life-style, and Dating, successfully widening the scale of the attacks. Just one of the apps, Helpful Translator Pro, amassed as substantially as 500,000 downloads.
“While regular quality assistance ripoffs just take gain of phishing tactics, this particular world wide scam has concealed guiding malicious Android applications performing as Trojans, allowing it to just take edge of user interactions for greater spread and an infection,” Zimperium researchers Aazim Yaswant and Nipun Gupta explained in a report shared with The Hacker News.
“These destructive Android applications surface harmless when wanting at the shop description and requested permissions, but this untrue perception of confidence alterations when buyers get charged thirty day period above thirty day period for the premium assistance they get subscribed to with out their awareness and consent.”
Like other banking trojans, GriftHorse does not exploit flaws in the Android running procedure, but fairly socially engineers customers into subscribing their phone quantities to premium SMS expert services on downloading the applications.

Following a successful an infection, the victims are bombarded with deceptive alerts promising a cost-free “Gift” that, when clicked, redirect them to a geo-precise webpage to submit their phone quantities for verification. “But in truth, they are distributing their phone variety to a premium SMS service that would start charging their phone monthly bill around €30 per month,” the researchers said.
Subsequent responsible disclosure to Google, the apps have been purged from the Enjoy Retail store. But they keep on to be out there on untrusted third-party app repositories, after all over again underscoring the dangers involved with sideloading arbitrary purposes and how they can emerge as an intrusion route for malware.
“General, GriftHorse Android Trojan usually takes benefit of smaller screens, community rely on, and misinformation to trick users into downloading and setting up these Android Trojans, as well frustration or curiosity when accepting the faux cost-free prize spammed into their notification screens,” Yaswant and Gupta concluded.
Located this article attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to examine much more unique information we submit.
Some components of this report are sourced from:
thehackernews.com

![[ebook] your first 90 days as ciso — 9 steps](https://thecybersecurity.news/data/2021/09/eBook-Your-First-90-Days-as-CISO-—-9-Steps-80x80.jpg) [eBook] Your First 90 Days as CISO — 9 Steps to Success
[eBook] Your First 90 Days as CISO — 9 Steps to Success