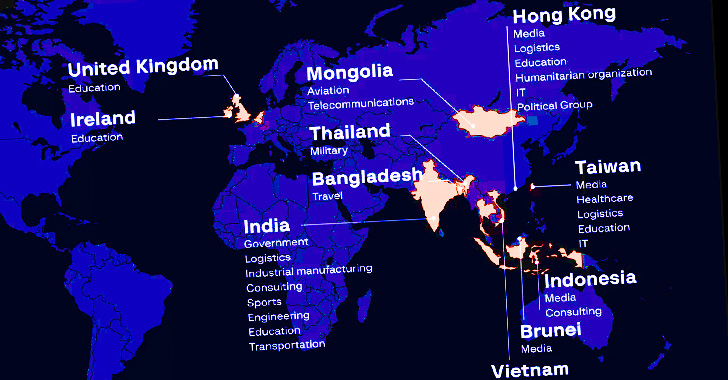
The Chinese highly developed persistent menace (APT) actor tracked as Winnti (aka APT41) has targeted at the very least 13 organizations geographically spanning throughout the U.S, Taiwan, India, Vietnam, and China towards the backdrop of 4 different campaigns in 2021.
“The focused industries included the public sector, producing, healthcare, logistics, hospitality, education, as very well as the media and aviation,” cybersecurity agency Team-IB stated in a report shared with The Hacker Information.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
This also integrated the attack on Air India that arrived to light-weight in June 2021 as element of a campaign codenamed ColunmTK. The other 3 campaigns have been assigned the monikers DelayLinkTK, Mute-Pond, and Light-Voice dependent on the area names utilised in the attacks.
APT41, also regarded as Barium, Bronze Atlas, Double Dragon, Wicked Panda, or Winnti, is a prolific Chinese cyber menace group that’s identified to carry out condition-sponsored espionage exercise in parallel with financially inspired operations at minimum due to the fact 2007.
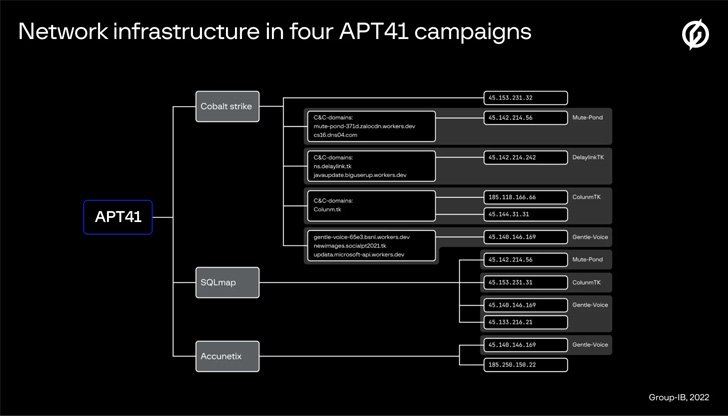
Describing 2021 as an “intensive year for APT41,” attacks mounted by the adversary included generally leveraging SQL injections on focused domains as the original entry vector to infiltrate victim networks, adopted by offering a custom made Cobalt Strike beacon on to the endpoints.
“APT41 customers typically use phishing, exploit several vulnerabilities (which includes Proxylogon), and perform watering hole or source-chain attacks to in the beginning compromise their victims,” the scientists reported.
Other actions carried out submit-exploitation ranged from setting up persistence to credential theft and conducting reconnaissance via living-off-the-land (LotL) procedures to collect info about the compromised ecosystem and laterally go across the network.

The Singapore-headquartered organization claimed it recognized 106 distinctive Cobalt Strike servers that were exclusively applied by APT41 in between early 2020 and late 2021 for command-and-handle. Most of the servers are no for a longer time lively.
The conclusions mark the ongoing abuse of the respectable adversary simulation framework by distinctive menace actors for article-intrusion destructive pursuits.
“In the earlier, the instrument was appreciated by cybercriminal gangs concentrating on banking companies, while right now it is popular amongst several menace actors regardless of their motivation, including infamous ransomware operators,” Group-IB Threat Analyst, Nikita Rostovtsev, said.
Identified this article fascinating? Observe THN on Facebook, Twitter and LinkedIn to examine more unique information we post.
Some pieces of this article are sourced from:
thehackernews.com

 Estonia fends off major cyber attack following Soviet-era monuments ousting
Estonia fends off major cyber attack following Soviet-era monuments ousting