A pair of reviews from cybersecurity firms SEKOIA and Pattern Micro sheds light on a new campaign undertaken by a Chinese danger actor named Lucky Mouse that entails leveraging a trojanized edition of a cross-system messaging application to backdoor devices.
An infection chains leverage a chat software identified as MiMi, with its installer documents compromised to down load and put in HyperBro samples for the Windows running program and rshell artifacts for Linux and macOS.
As many as 13 different entities situated in Taiwan and the Philippines have been at the acquiring conclusion of the attacks, eight of whom have been strike with rshell. The initially sufferer of rshell was reported in mid-July 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Lucky Mouse, also called APT27, Bronze Union, Emissary Panda, and Iron Tiger, is recognized to be active given that 2013 and has a background of attaining obtain to targeted networks in pursuit of its political and navy intelligence-collection targets aligned with China.

The advanced persistent menace actor (APT) is also adept at exfiltrating superior-value information utilizing a wide vary of tailor made implants these kinds of as SysUpdate, HyperBro, and PlugX.
The newest improvement is major, not minimum since it marks the risk actor’s introductory attempt at targeting macOS along with Windows and Linux.
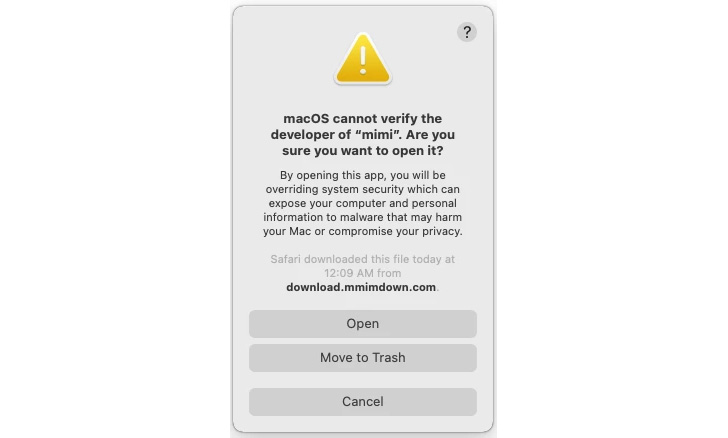
The marketing campaign has all the hallmarks of a source chain attack in that the backend servers hosting the application installers of MiMi are controlled by Lucky Mouse, therefore generating it doable to tweak the application to retrieve the backdoors from a remote server.
This is borne out by the actuality that the app’s macOS edition 2.3. was tampered to insert the malicious JavaScript code on Might 26, 2022. Although this may perhaps have been the initial compromised macOS variant, variations 2.2. and 2.2.1 built for Windows have been identified to incorporate equivalent additions as early as November 23, 2021.
rshell, for its portion, is a common backdoor that will come with all the common bells-and-whistles, making it possible for for the execution of arbitrary commands acquired from a command-and-manage (C2) server and transmitting the success of the execution back again to the server.

It really is not straight away distinct if MiMi is a legitimate chat plan, or if it was “made or repurposed as a surveillance resource,” even though the application has been utilised by one more Chinese-speaking actor dubbed Earth Berberoka (aka GamblingPuppet) aimed at on-line gambling internet sites – at the time again indicative of the common device sharing among the Chinese APT teams.
The operation’s connections to Fortunate Mouse stems from back links to instructure earlier recognized as made use of by the China-nexus intrusion established and the deployment of HyperBro, a backdoor completely place to use by the hacker group.
As SEKOIA factors out, this is not the initially time the adversary has resorted to utilizing a messaging app as a leaping-off stage in its attacks. In late 2020, ESET disclosed that a popular chat software called Equipped Desktop was abused to deliver HyperBro, PlugX, and a remote obtain trojan identified as Tmanger concentrating on Mongolia.
Located this report fascinating? Comply with THN on Facebook, Twitter and LinkedIn to read additional distinctive content material we submit.
Some components of this posting are sourced from:
thehackernews.com


 Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders
Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders