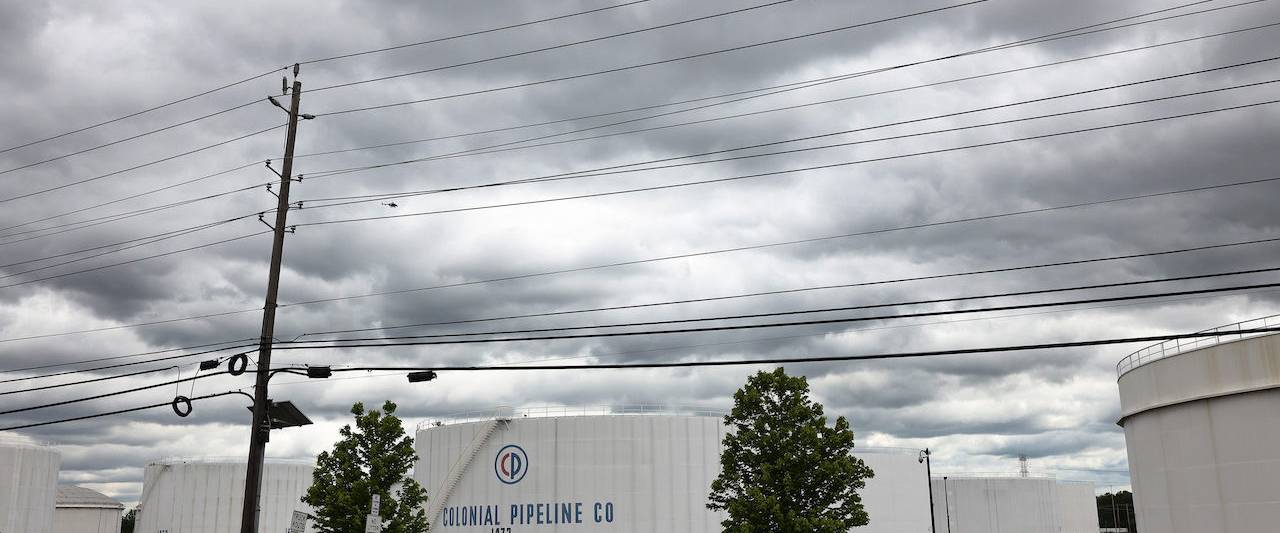
Gasoline holding tanks are observed at Colonial Pipeline’s Linden Junction Tank Farm on May well 10, 2021 in Woodbridge, New Jersey. Alpharetta, Georgia-based mostly Colonial Pipeline, which has the largest gas pipeline, was pressured to shut down its oil and fuel pipeline process on Friday after a ransomware attack that has slowed down the transportation of oil in the japanese U.S. (Image by Michael M. Santiago/Getty Illustrations or photos)
A May perhaps 7 ransomware attack on Colonial Pipeline has largely shut down the greatest refined products and solutions pipeline process in the U.S., demonstrating the unique cybersecurity risks and vulnerabilities associated with geographically dispersed networks.
Just as oil and gas can stream up and down the pipeline, so can malware, reaching remote amenities whose IT and operational technology programs may perhaps not be adequately fortified to protect towards an attack. As a result, 1 position of compromise can have a cascading impact that impacts fuel distribution throughout the country, which in transform can harm enterprises that depend on these assets, spike gasoline price ranges and harm the overall economy.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
John Cusimano, vice president at aeCyberSolutions, claimed that cybersecurity in the pipeline industry is “far powering that of other power sectors,” noting that a frequent problem is“the lack of segmentation of the pipeline supervisory manage and details acquisition networks, which “connect the pipeline regulate centre to each individual terminal, pumping station, distant isolation valve and tank farm along the pipeline.”
“These are really massive networks masking considerable distances but they are ordinarily ‘flat’ from a network segmentation standpoint,” Cusimano added. “This indicates that once anyone gains access to the SCADA network they have accessibility to each individual system on the network.”
The Colonial Pipeline, which runs amongst the U.S. Gulf Coast and New York, is about 5,500-miles prolonged and reportedly transports about 45 p.c of fuel, diesel, jet gas and dwelling heating oil consumed on the East Coast. The route it carves is dotted with different amenities that are linked to the over-all network.
“Some of those services are in pretty remote places with little to no actual physical security – meaning that if an attacker breached the security of one of those people amenities, they could attain obtain to the network” as a whole, Cusimano ongoing.
Although IT and OT have ordinarily remained isolated from every other, that’s not normally the circumstance as these devices significantly converge.
For instance, Cusimano said that sure data or software package systems can pass in between the firewalls frequently separating IT networks from pipeline SCADA networks. This features creation figures, operational metrics, back again-up and restoration software package, antivirus program and network monitoring software program from companies these kinds of as SolarWinds. “This was just one of my best problems when I discovered of the Solarwinds attack,” he reported.
Grant Geyer, chief solution officer at Claroty, identified a different risk factor involved with highly distributed environments: “the tools that are employed to help asset operators’ remote connectivity are optimized for simple accessibility and not for security,” he explained. “This gives attackers alternatives to sneak as a result of cyber defenses as we saw in the water utility attack in Oldsmar, Florida before this yr.”
Other critical infrastructure operators that encounter related dispersed network challenges include things like the electrical grid and drinking water and wastewater treatment method utilities, claimed experts.
With electric electricity, for instance, “you have property that are unmanned in the field… that are quite considerably operating 24-7,” explained Tobias Whitney, vice president, strength security solutions, at Fortress Information and facts Security. “There’s not a incredible volume of time to plan outages to perform updates, there are a ton of suppliers and technology sellers that present technologies to the footprint. So there are some unique troubles. When you have a far more regular IT-oriented breach, there are usually problems about [if] this particular breach or menace will traverse into the OT facet of the equation.”
Indeed, the simple fact that Alpharetta, Georgia-dependent Colonial Pipeline has shut down its four principal pipelines, despite stating in a push release that its IT networks were being contaminated, is a stressing sign to some gurus. It is probable this transfer is for precautionary reasons to make sure the malware didn’t migrate into the OT ecosystem it’s also doable that the problem is worse than the general public realizes at this time.
“We do a great deal of work with pipeline firms on incident reaction preparing and talking via diverse eventualities – and the selection to shut down an overall pipeline naturally is a single that does not get created flippantly. So there experienced to be sizeable problem. It would have had to be an govt determination to shut down the full pipeline,” stated Cusimano.
It’s telling, he famous, that Colonial Pipeline is not even hoping to functioning the pipeline manually. “It practically implies that their full IT infrastructure could have been compromised [and] it may perhaps have bled into SCADA,” or at the really the very least, “their functions are so tightly coupled that they did not sense that they could safely and securely function.”
“It would strike me to be a bit odd that you do that level of a precautionary activity because of a cyberattack [supposedly] isolated to your IT ecosystem,” stated Whitney, noting the palpable “downstream implications” of slicing off the distribution of oil and fuel. This “tells me that there could have been some convergence there. There could have been some points where by the IT risk exposure could have cascaded into the OT aspect.”
There is no sign as of yet as to irrespective of whether Colonial Pipeline administration plans to pay out the ransomware actors – determined as the DarkSide Russian cybercriminal gang – in purchase to hasten the restoration of its disrupted techniques. If that is not a viable selection, then Colonial Pipeline and its downstream consumers could be sensation the results for pretty some time, as restoration will be tiresome.
“You have to have the backups – and that is where by it definitely receives demanding,” reported Cusimano. While the main command centers of central functions probably have strong backup courses in location for their servers, “it receives a lot far more demanding when you go out to the industry. All the pump stations and terminals and tank farms – they all have desktops out there as properly, and they could not have been backed up with the very same degree of rigor than generally what we see. The more you get away from the company major working centers and knowledge facilities, backup and restoration receives a large amount weaker.”
If malicious code did finish up proliferating across the OT network, then restoration could be even far more laborious. “We’d be speaking about months,” claimed Whitney, “especially if the code was operated in this kind of a way to trigger bodily hurt to the infrastructure.”
It might be early for takeaways, but Whitney stated this incident demonstrates that critical infrastructure operators – and frankly all businesses – “need to be more practiced, a lot more operationally well prepared for ransomware-style gatherings,” such as “how they’re likely to mitigate and regulate these attempts whilst they are occurring.”
“Colonial Pipeline carries on to devote large sources to restoring pipeline functions speedily and safely and securely,” Colonial Pipeline reported in a assertion that was up to date on Monday. “Segments of our pipeline are getting introduced back on the web in a stepwise style, in compliance with suitable federal rules and in near session with the Section of Strength, which is major and coordinating the federal government’s reaction.”
“Restoring our network to normal functions is a process that involves the diligent remediation of our units, and this takes time. In reaction to the cybersecurity attack on our process, we proactively took selected systems offline to comprise the risk, which temporarily halted all pipeline operations, and impacted some of our IT devices. To restore company, we ought to do the job to make sure that every single of these units can be brought back again on the net securely.”
Some areas of this report are sourced from:
www.scmagazine.com

 Four Confess to ‘Bulletproof Hosting’
Four Confess to ‘Bulletproof Hosting’