Modern-day password procedures are comprised of quite a few distinctive factors that add to its effectiveness. A single of the elements of an productive recent password coverage would make use of what is regarded as a custom dictionary that filters out specified words that are not permitted as passwords in the setting.
Employing tailor made dictionaries, corporations can appreciably make improvements to their cybersecurity posture and filter out clear passwords that deliver weak security for consumer accounts.
When working with password dictionaries in your password plan, there are many different strategies to take into account. First, let’s contemplate crafting a personalized dictionary for your password policy, such as common direction on how these are designed, configured, and how you can conveniently use custom dictionaries in an active directory atmosphere.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Why customize your dictionary?
Custom made dictionaries are born from the will need to “feel as a hacker thinks.” Compromised qualifications are a person of the primary causes of malicious data breaches throughout the board. They are also 1 of the most high priced to companies. IBM’s Expense of a Info Breach Report 2020, compromised qualifications increased the typical overall price of a breach by approximately $1 million to $4.77 million.
Hackers usually use credential-centered attacks to compromise weak passwords, passwords that have been formerly breached, prevalent passwords used in a particular company sector, or typical spelling transformations.
Sadly, all of us are likely to use passwords that we can easily don’t forget. In addition, finish-people frequently add common numbers or image patterns to the commencing or conclude of passwords to get around password complexity specifications.
Each human nature and the technology equipment available enable conveniently cracking or guessing weak, common, or expected passwords. Even though attackers have obtain to big databases of breached and or else popular or weak passwords, the “excellent fellas” can put into action a password file in a very good way – the custom made dictionary.
The custom password dictionary performs in favor of securing the passwords in your ecosystem.
When applied, the personalized dictionary provides a signifies to filter the chosen password or conclude-end users in this kind of a way as to disallow passwords or versions of the passwords contained in the personalized dictionary.
So, aren’t all passwords that meet the Energetic Listing Password Policy necessities safe? Not just.
Whilst password plan necessities described by Lively Directory Password Coverage are a excellent starting place, they go away a great deal to be desired when contemplating the cracking and other password instruments that cybercriminals are making use of now.
As an example, a password coverage may well require that an finish-user meet up with the pursuing demands:
- Least of 8 characters
- Password must meet complexity prerequisites (Ought to consist of uppercase, lowercase, quantities, and non-alphabetic people such as symbols)
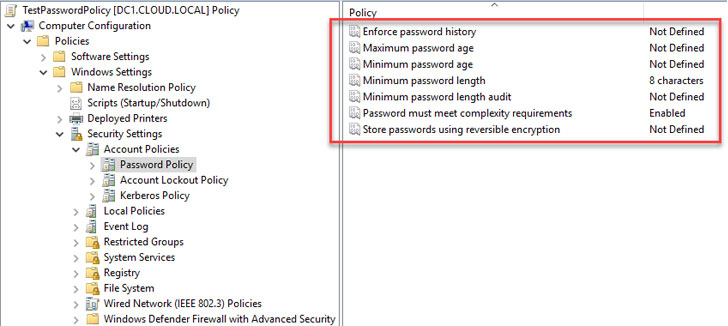 A password coverage outlined in Energetic Directory Domain Providers
A password coverage outlined in Energetic Directory Domain Providers
Working with the native Lively Directory Password Policy settings earlier mentioned, a consumer could probably set passwords this kind of as:
- P@$$w0rd123
- MybusinessName123!
- Letmein1$
The above passwords satisfy all the standards described as part of the length and complexity prerequisites.
Even so, they are weak and simply guess because of to diverse motives. As the previously mentioned illustrations exhibit, these could be identified variants of typical terms these kinds of as “Password,” associated to your precise enterprise title or industry, or a prevalent phrase contained in a cracked password database this sort of as “Letmein1$.”
Downloadable custom made password dictionaries
You could not want to “reinvent the wheel” when it will come to collecting passwords to use in a personalized dictionary for your password plan. There are out-of-the-box password dictionaries and password information that can be freely downloaded as the foundation for a custom made password dictionary. An instance includes the Have I Been Pwned password checklist: Have I Been Pwned: Pwned Passwords.
Companies can also use easily offered tools these kinds of as Crunch, out there in Kali Linux or installable from your Linux distribution repository. In Ubuntu, you can put in Crunch making use of the command:
- sudo apt-get put in crunch
It lets making a wordlist that can be employed for brute pressure or password toughness auditing by SecOps groups in your corporation. In addition, these readily available applications can provide the foundation for making your very own custom made password lists in your atmosphere.
Using a Password filter .dlls
Even so, there is a lot more involved than simply generating a password dictionary file. Companies that want to put into practice their possess tailor made password filter .dll, alongside with text that contains their enterprise identify or market-precise keywords and phrases, need to have the advancement talent and resources accessible to generate the .dll file needed for the password filter functionality in Lively Directory.
Microsoft outlines the system of registering and installing a password filter .dll in this article: Putting in and Registering a Password Filter DLL – Earn32 apps | Microsoft Docs.
Tailor made dictionary solutions in your password policy tools
Is there an straightforward way to craft a tailor made dictionary for your password coverage? Specops Password Coverage usually takes the more durable operate out of employing tailor made dictionaries for your password policies and permits for the negation of about 2 billion regarded breached passwords moreover any personalized conditions like your business title, or area, to be added to a password policy tool.
High-excellent password coverage tools like this combine with your indigenous Active Directory Password Policies applied at the Team Plan degree.
With simple checkboxes, the Specops resolution lets IT admins to simply and speedily apply several password dictionaries as element of the password rules configured for their organization.
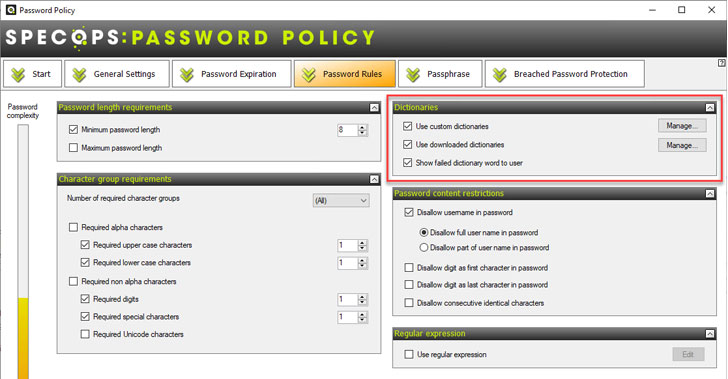 Specops Password Policy dictionary options
Specops Password Policy dictionary options
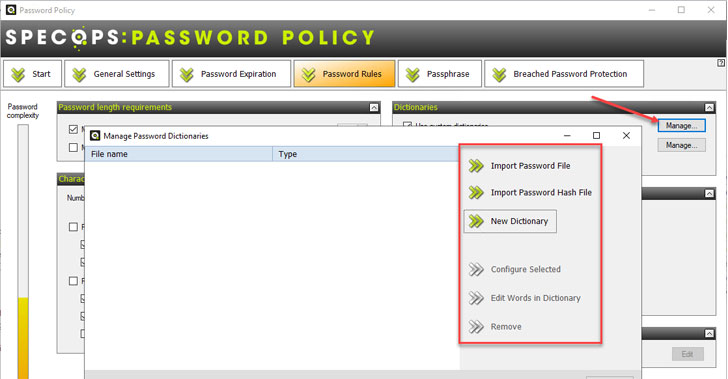 Configuring the custom dictionaries setting in Specops Password Plan
Configuring the custom dictionaries setting in Specops Password Plan
Configuring the Use personalized dictionaries allows importing password documents, hash documents, or producing new dictionaries right from the interface.
Below the downloaded dictionaries configuration, admins have accessibility to easily out there password dictionary data files that can be downloaded straight from the Specops Password Policy interface.
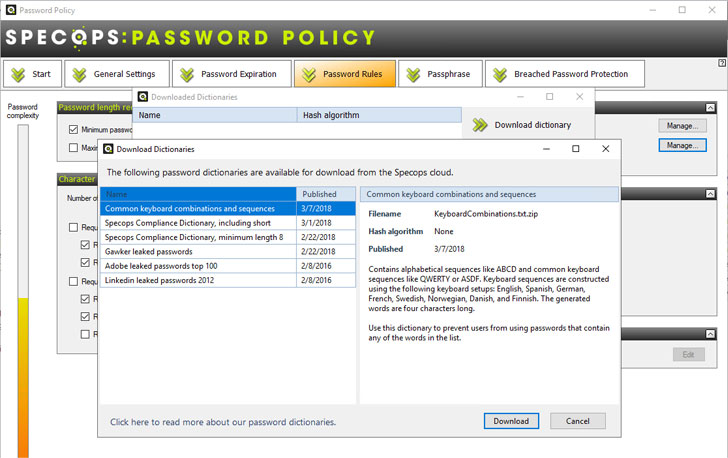 Downloading password dictionary information from the Specops Password Policy interface
Downloading password dictionary information from the Specops Password Policy interface
Specops Password Plan helps make configuring, employing, and sustaining customized dictionary files for your organization’s password policy easier—with no programming information or abilities necessary.
Get began using a personalized dictionary in your password plan
Businesses currently need to bolster the security of account passwords to strengthen their over-all cybersecurity posture. Applying personalized dictionaries as aspect of their password insurance policies is a fantastic way to factor in an offensive technique to your cybersecurity endeavours.
On the other hand, implementing a tailor made password filter .dll in the surroundings requires creating the custom made password filter .dll file demanded by Lively Listing. This advancement can present roadblocks to organizations implementing customized dictionaries like price tag, upkeep, and efficiency blockers.
Specops Password Coverage enables implementing numerous custom dictionary information with just a number of clicks, getting rid of the complexity and security issues included with utilizing this effectively.
Study additional about Specops Password Coverage or get started your cost-free demo.
Discovered this post interesting? Observe THN on Fb, Twitter and LinkedIn to examine much more exceptional material we submit.
Some pieces of this write-up are sourced from:
thehackernews.com


 Treasury wiped data from over 100 gov-issued smartphones in 2020
Treasury wiped data from over 100 gov-issued smartphones in 2020