The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday launched an industrial command programs (ICS) advisory warning of seven security flaws in Dataprobe’s iBoot-PDU electricity distribution unit product or service, primarily used in industrial environments and facts facilities.
“Profitable exploitation of these vulnerabilities could guide to unauthenticated remote code execution on the Dataprobe iBoot-PDU machine,” the agency explained in a discover.
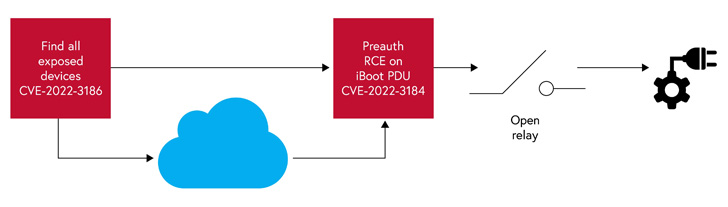
Credited with disclosing the flaws is industrial cybersecurity organization Claroty, which said the weaknesses could be remotely induced “possibly via a immediate web link to the unit or by using the cloud.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

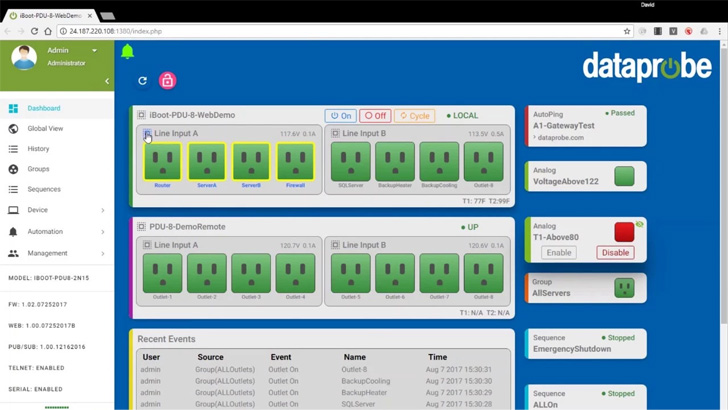
iBoot-PDU is a electric power distribution device (PDU) that delivers users with actual-time monitoring capabilities and advanced alerting mechanisms by way of a web interface so as to manage the electrical power provide to gadgets and other tools in an OT natural environment.
The vulnerabilities assume new importance when having into thing to consider the fact that no less than 2,600 PDUs are accessible on the internet, with Dataprobe units accounting for just about a third of individuals uncovered, according to a 2021 report from attack surface area management platform Censys.
Claroty’s investigation of the PDU firmware exhibits that the product is crippled by issues ranging from command injection to path traversal flaws, exposing shoppers to severe security hazards –
- CVE-2022-3183 (CVSS score: 9.8) – A command injection vulnerability stemming from a deficiency of sanitization of consumer enter
- CVE-2022-3184 (CVSS score: 9.8) – A route traversal vulnerability that enables access to an unauthenticated PHP web site, which could be abused to insert malicious code
Thriving distant exploitation of the flaws “puts an attacker inside of arm’s duration of disrupting critical products and services by cutting off electrical electricity to the machine and subsequently, anything at all plugged into it,” Clarory researcher Uri Katz reported.
The other five uncovered vulnerabilities (from CVE-2022-3185 via CVE-2022-3189) could be weaponized by a poor actor to entry the device’s key management web page from the cloud and even trick the server to link to arbitrary inner or external methods (aka SSRF), likely leaking sensitive details.

“Even an innocuous energy distribution device remotely managed about the internet or by using a cloud-based mostly management system can provide a decided attacker to concentrate on the network, or with a way to disrupt crucial products and services by cutting electrical power to units plugged into a PDU,” Katz stated.
Claroty additional disclosed that it identified a way to enumerate cloud-linked iBoot PDU equipment by exploiting a mix of a legitimate cookie and the gadget ID (a sequential numeric benefit that can be trivially guessed), thereby widening the accessible attack surface to all related devices.
End users of Dataprobe iBoot-PDU are proposed to improve to the latest firmware version (1.42.06162022) as nicely as disable SNMP, Telnet, and HTTP, if not in use, as a mitigation from some of these vulnerabilities.
Uncovered this short article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to examine a lot more special content material we put up.
Some parts of this short article are sourced from:
thehackernews.com


 Product Review: Stellar Cyber Open XDR Platform
Product Review: Stellar Cyber Open XDR Platform