Networking machines organization Netgear has produced nonetheless yet another spherical of patches to remediate a substantial-severity remote code execution vulnerability impacting various routers that could be exploited by distant attackers to take manage of an influenced process.
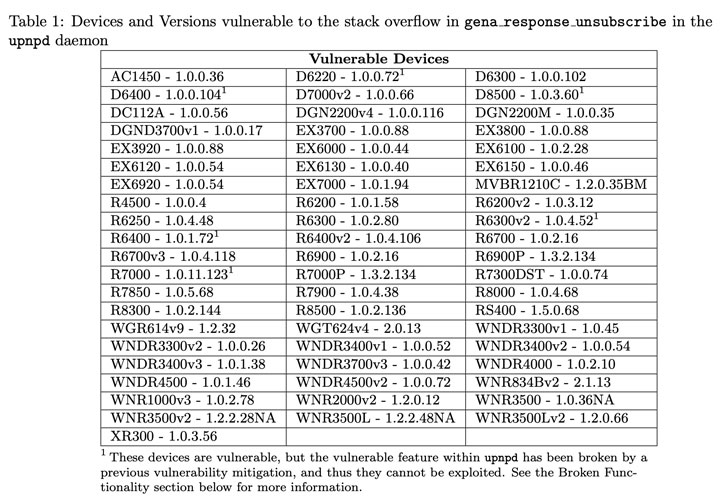
Tracked as CVE-2021-34991 (CVSS rating: 8.8), the pre-authentication buffer overflow flaw in little business and household place of work (SOHO) routers can guide to code execution with the optimum privileges by getting edge of an issue residing in the Universal Plug and Enjoy (UPnP) aspect that will allow devices to learn each other’s presence on the very same community network and open up ports wanted to link to the public Internet.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Since of its ubiquitous mother nature, UPnP is applied by a extensive assortment of devices, together with individual computers, networking devices, online video sport consoles and internet of factors (IoT) units.
Precisely, the vulnerability stems from the truth that the UPnP daemon accepts unauthenticated HTTP SUBSCRIBE and UNSUBSCRIBE requests — which are function notification alerts that devices use to acquire notifications from other gadgets when sure configuration modifications, this sort of as media sharing, take place.
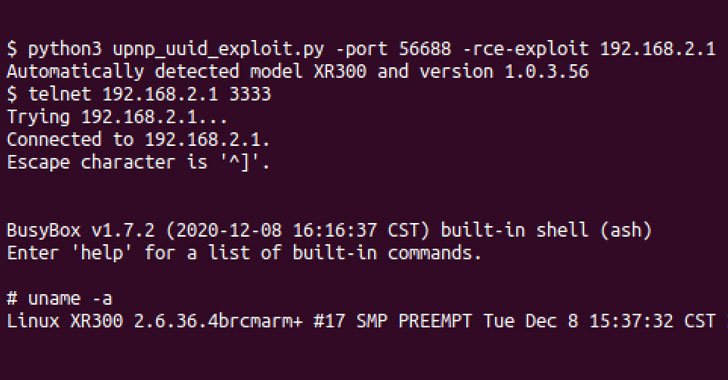
But according to GRIMM security researcher Adam Nichols, there exists a memory stack overflow bug in the code that handles the UNSUBSCRIBE requests, which permits an adversary to deliver a specially crafted HTTP ask for and operate destructive code on the influenced system, which includes resetting the administrator password and providing arbitrary payloads. After the password has been reset, the attacker can then login to the webserver and modify any settings or launch additional attacks on the webserver.
“Considering the fact that the UPnP daemon operates as root, the greatest privileged user in Linux environments, the code executed on behalf of the attacker will be run as root as very well,” Nichols claimed. “With root accessibility on a device, an attacker can examine and modify all targeted traffic that is handed through the device.”

This is much from the initially time vulnerable implementations of UPnP have been uncovered in networked equipment.
In June 2020, security researcher Yunus Çadirci found what is called a CallStranger vulnerability (CVE-2020-12695, CVSS score: 7.5) whereby a distant, unauthenticated attacker may well be in a position to abuse the UPnP SUBSCRIBE functionality to send visitors to arbitrary destinations, resulting in amplified DDoS attacks and details exfiltration. What is actually additional, no fewer than 45,000 routers with vulnerable UPnP companies had been formerly leveraged in a 2018 marketing campaign to deploy EternalBlue and EternalRed exploits on compromised systems.
Found this article intriguing? Observe THN on Fb, Twitter and LinkedIn to browse far more distinctive articles we post.
Some pieces of this write-up are sourced from:
thehackernews.com

 How to Build a Security Awareness Training Program that Yields Measurable Results
How to Build a Security Awareness Training Program that Yields Measurable Results