A economically determined cybercrime group has been linked to an ongoing wave of attacks aimed at hospitality, resort, and journey businesses in Latin The united states with the aim of setting up malware on compromised units.
Company security business Proofpoint, which is monitoring the group below the title TA558 dating all the way again to April 2018, termed it a “modest criminal offense danger actor.”
“Because 2018, this team has employed reliable practices, procedures, and processes to attempt to install a wide range of malware which include Loda RAT, Vjw0rm, and Revenge RAT,” the company’s menace exploration staff reported in a new report.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
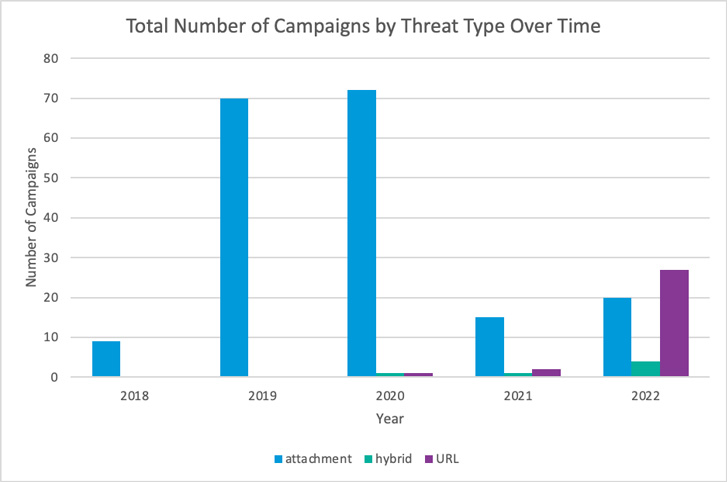
The team has been operational at a greater tempo in 2022 than normal, with intrusions generally geared to Portuguese and Spanish speakers in Latin America, and to a lesser extent in Western Europe and North The us.

Phishing campaigns mounted by the group entail sending malicious spam messages with reservation-themed lures this kind of as lodge bookings that include weaponized paperwork or URLs in a bid to entice unwitting end users into setting up trojans capable of reconnaissance, knowledge theft, and distribution of observe-on payloads.
The attacks have subtly developed around the a long time: The types noticed amongst 2018 and 2021 leveraged email messages with Word paperwork that both contained VBA macros or exploits for flaws these kinds of as CVE-2017-11882 and CVE-2017-8570 to download and install a combination of malware this kind of as AsyncRAT, Loda RAT, Revenge RAT, and Vjw0rm.
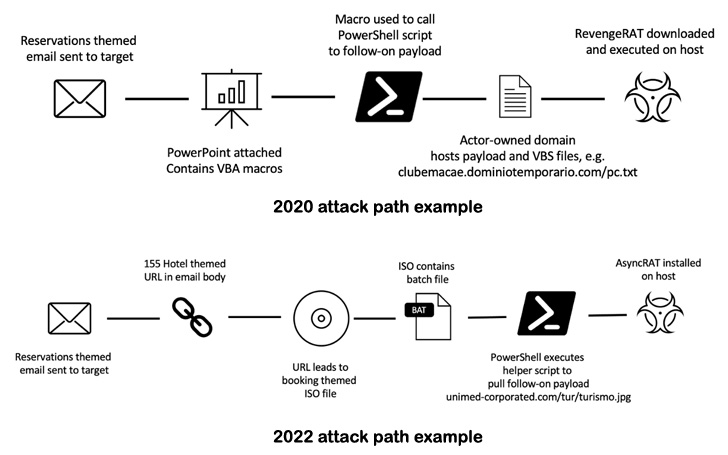
In new months, nonetheless, TA558 has been observed pivoting away from macro-laden Microsoft Business office attachments in favor of URLs and ISO information to accomplish preliminary an infection, a transfer possible in reaction to Microsoft’s choice to block macros in files downloaded from the web by default.
Of the 51 strategies carried out by the team so significantly this calendar year, 27 of them are reported to have included URLs pointing to ISO information and ZIP archives, in comparison to just five campaigns completely from 2018 via 2021.

Proofpoint additional noted that the intrusions chronicled under TA558 are part of a broader established of malicious functions focusing on victims in the Latin American area. But in the absence of any post-compromise activity, it can be suspected that TA558 is a monetarily motivated cybercriminal actor.
“The malware utilized by TA558 can steal details which includes lodge buyer person and credit history card knowledge, allow lateral motion, and provide follow-on payloads,” the researchers said. “Activity done by this actor could guide to data theft of equally company and shopper facts, as nicely as potential economic losses.”
Observed this report exciting? Adhere to THN on Fb, Twitter and LinkedIn to go through additional exceptional content material we put up.
Some parts of this short article are sourced from:
thehackernews.com


 Businesses Found to Neglect Cybersecurity Until it is Too Late
Businesses Found to Neglect Cybersecurity Until it is Too Late