Shutterstock
The scraped data of more than 500 million LinkedIn profiles has been place up for sale on a well known hacker discussion board.
The post’s writer has leaked two million data now as proof of the existence of the a great deal more substantial information trove, as reported by Cybernews.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The info, which is distribute across four information, is stated to involve comprehensive names, email addresses, phone quantities, and information and facts associated to their spot of operate.
So far, no exact determine has been established for the info, while the user has reported that fascinated parties must count on to shell out a 4-digit sum, probably in bitcoin.
Even though it has been verified that the information was scraped from LinkedIn, it can be unclear regardless of whether this is a new details breach or if the information has been taken from past LinkedIn breaches.
A LinkedIn spokesperson told IT Pro: “While we’re even now investigating this issue, the posted dataset seems to include publicly viewable info that was scraped from LinkedIn merged with facts aggregated from other sites or organizations.
“Scraping our members’ data from LinkedIn violates our terms of company and we are consistently functioning to protect our associates and their knowledge.”
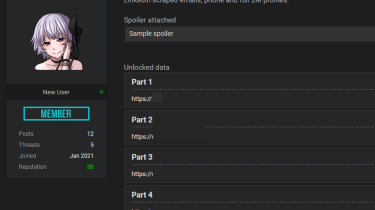
The entire leaked information comprise information and facts like LinkedIn IDs, whole names, email addresses, phone quantities, genders, hyperlinks to LinkedIn profiles, and qualified titles.
Despite the fact that there was no proof of delicate information like credit card details or lawful files in the sample posted to the forum, the leaked information can nonetheless be utilised for phishing or social engineering attacks.
Earlier this month, it emerged that a hacking group was focusing on LinkedIn people with bogus position features to infect them with malware that allowed them to acquire command of a victim’s computer system. The Golden Rooster hacking group distribute the malware by spear phishing victims with a destructive .ZIP file that would provide remote accessibility to their system.
The personal knowledge of 533 million Facebook users was also located on a hacking forum this thirty day period and was out there to obtain for free of charge. The records, which signify all-around a fifth of the company’s entire consumer base, contained entire names, birth dates, and the position of a user’s marriage.
Some components of this post are sourced from:
www.itpro.co.uk


 Fortinet FortiGate 60F: A fully-featured security appliance
Fortinet FortiGate 60F: A fully-featured security appliance