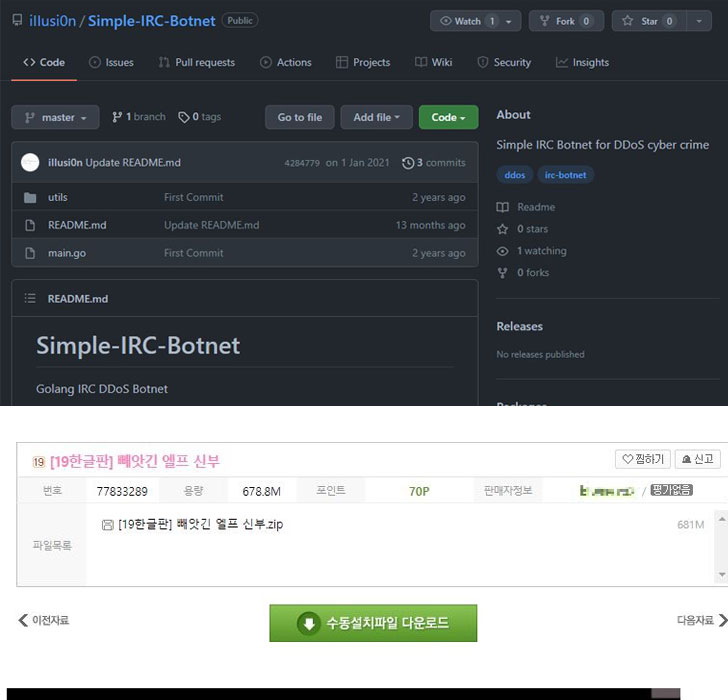
An IRC (Internet Relay Chat) bot pressure programmed in GoLang is remaining employed to start distributed denial-of-services (DDoS) attacks focusing on customers in Korea.
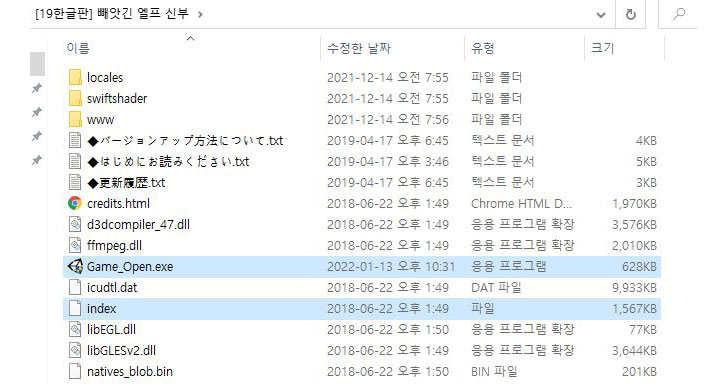
“The malware is getting distributed underneath the guise of grownup video games,” scientists from AhnLab’s Security Emergency-reaction Middle (ASEC) explained in a new report printed on Wednesday. “On top of that, the DDoS malware was installed via downloader and UDP RAT was used.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The attack works by uploading the malware-laced game titles to webhards, which refers to a web really hard push or a remote file hosting services, in the form of compressed ZIP archives that, when opened, incorporates an executable (“Sport_Open up.exe”) that’s orchestrated to operate a malware payload aside from launching the actual sport.
This payload, a GoLang-primarily based downloader, establishes connections with a distant command-and-management (C&C) server to retrieve extra malware, including an IRC bot that can execute DDoS attacks.
“It is also a form of DDoS Bot malware, but it employs IRC protocols to converse with the C&C server,” the researchers in depth. “Not like UDP Rat that only supported UDP Flooding attacks, it can also support attacks this sort of as Slowloris, Goldeneye, and Hulk DDoS.”
GoLang’s reduced improvement troubles and its cross-platform assistance have made the programming language a well-known option for danger actors, the scientists extra.
“The malware is becoming dispersed actively by way of file sharing websites this kind of as Korean webhards,” AhnLab mentioned. “As these kinds of, caution is encouraged when approaching executables downloaded from a file-sharing site. It is advocate[ed] for the people to download solutions from the official web sites of developers.”
Observed this report attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to study far more unique articles we put up.
Some components of this article are sourced from:
thehackernews.com



 Ukraine: Recent Cyber Attacks Part of Wider Plot to Sabotage Critical Infrastructure
Ukraine: Recent Cyber Attacks Part of Wider Plot to Sabotage Critical Infrastructure