A cyber-attacker successfully breaks into your setting and starts sneaking all around to discover something precious – intellectual house, financial institution account qualifications, company plans, no matter what. The attacker tends to make his way to a certain host on a network node to look through the directories, and quickly, his relationship is slash off. The stolen username and password he acquired no longer functions.
Unknowingly, the attacker induced a very well-concealed lure that detected his presence, took rapid motion to sever his connection, and then blocked his reconnect capability. Pretty interesting.
The thought of Deception technology is rather great. And it can be an incredibly worthwhile security layer that comes into play when other security layers are productively bypassed. The dilemma, nonetheless, is that only really massive enterprises have been capable to leverage Deception technology owing to its expense and complexity to put into action and retain. Sad to say, compact to medium-sized enterprises, the so-referred to as SMEs, just really don’t have the budgets and personnel essential to leverage this worthwhile technology.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
A Recreation Changer for Deception Technology
Cybersecurity business Cynet recognizes the incredible value of deception technology. So much so, in actuality, that they developed deception technology natively into their XDR system (Read far more in this Deception whitepaper).
In this way, Cynet consumers instantly get strong Deception technology, pre-integrated as component of their XDR platform. In very simple text: as a substitute of buying deception technology on prime of the current endpoint protection (NGAV/EDR) – you get Deception as part of your endpoint safety alternative, with each other with other added benefits of XDR.
This is a boon for these corporations that could not find the money for to obtain Deception technology from a specialised vendor and for those that only did not want the headache of deploying, integrating, running, and protecting nonetheless one more cybersecurity remedy. Though cybersecurity appears to be to be having much more challenging, requiring more answers and much more oversight, the Cynet tactic is a breath of contemporary air.
The moment the Cynet XDR alternative is deployed, consumers simply just configure various kinds of decoys across their surroundings, and that’s that. Three forms of decoys are configurable in just the system:
File Deception
These are decoy knowledge documents and backlinks that show up specifically as an attacker would see for reputable facts information and links. When an attacker opens a decoy facts file, an alert is brought on alongside with details encompassing the file access, such as the attacker IP tackle, the target IP tackle, hostname, and file title.

Clients can use off-the-shelf decoy documents and even craft their have. Just be mindful that when naming a file “best mystery information and facts.docx,” it might idea off attackers that you have Deception technology in location. Continue to keep decoy file names reliable with your regular file naming strategies.
Consumer Deception
These are decoy consumer accounts that can be put throughout several endpoints. When an attacker works by using decoy qualifications to login with a person of the decoy consumers, an alert is produced. All over again, usernames and account information and facts need to mimic conventions utilised in just your group.

Network Deception
Incorporating decoy hosts within just your network setting is an additional way to uncover attackers on your network. The decoys are made to show up as useful techniques that reputable buyers interact with to complete their tasks. A single idea is to truly produce significantly extra decoy hosts than real hosts, putting the odds in your favor that a productive attacker will make the mistaken shift and expose his presence – which is the proper transfer from your perspective!
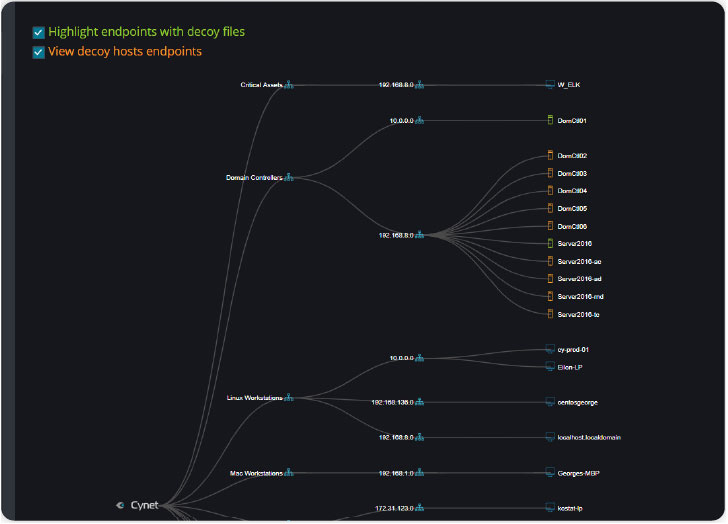 Case in point demonstrating Cynet deception hosts (shown in orange) on network
Case in point demonstrating Cynet deception hosts (shown in orange) on network
Deception As A System Element
It would seem that anything as useful as Deception technology really should be deployed as a critical part of each and every firm’s cybersecurity technology stack. Nevertheless, the expenditure and complexity of adding this technology have absolutely been a barrier to popular adoption. The strategy Cynet is taking – bundled Deception as just one ingredient of their strong XDR platform – alterations the narrative. Implementing Deception technology will not cost just about anything further and can be implemented with the click on of a mouse. And I’m not pretending!
Download Cynet Deception whitepaper right here
Uncovered this article interesting? Follow THN on Fb, Twitter and LinkedIn to go through extra distinctive content we put up.
Some areas of this write-up are sourced from:
thehackernews.com

 If You Don’t Have A SASE Cloud Service, You Don’t Have SASE At All
If You Don’t Have A SASE Cloud Service, You Don’t Have SASE At All