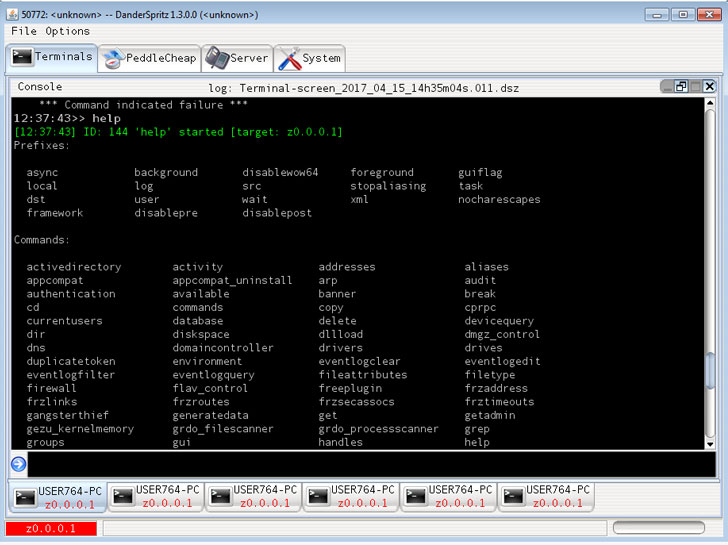
Cybersecurity researchers have available a detailed glimpse into a system named DoubleFeature that’s focused to logging the different levels of put up-exploitation stemming from the deployment of DanderSpritz, a comprehensive-featured malware framework used by the Equation Group.
DanderSpritz came to mild on April 14, 2017, when a hacking team recognised as the Shadow Brokers leaked the exploit device, among the many others, beneath a dispatch titled “Lost in Translation.” Also included in the leaks was EternalBlue, a cyberattack exploit formulated by the U.S. National Security Agency (NSA) that enabled danger actors to have out the NotPetya ransomware attack on unpatched Windows desktops.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The device is a modular, stealthy, and absolutely practical framework that depends on dozens of plugins for article-exploitation functions on Windows and Linux hosts. DoubleFeature is a single among them, which capabilities as a “diagnostic resource for sufferer equipment carrying DanderSpritz,” researchers from Look at Level explained in a new report published Monday.
“DoubleFeature could be used as a kind of Rosetta Stone for greater comprehension DanderSpritz modules, and devices compromised by them,” the Israeli cybersecurity company added. “It’s an incident response team’s pipe aspiration.”
Made to retain a log of the kinds of instruments that could be deployed on a target machine, DoubleFeature is a Python-dependent dashboard that also doubles up as a reporting utility to exfiltrate the logging facts from the infected machine to an attacker-controlled server. The output is interpreted applying a specialized executable named “DoubleFeatureReader.exe.”
Some of the plugins monitored by DoubleFeature involve remote accessibility tools called UnitedRake (aka EquationDrug) and PeddleCheap, a stealthy info exfiltration backdoor dubbed StraitBizarre, an espionage platform known as KillSuit (aka GrayFish), a persistence toolset named DiveBar, a covert network access driver referred to as FlewAvenue, and a validator implant named MistyVeal that verifies if the compromised system is in fact an genuine sufferer machine and not a research ecosystem.
“Sometimes, the world of high-tier APT equipment and the world of regular malware can appear like two parallel universes,” the scientists said. “Country-point out actors are inclined to [maintain] clandestine, gigantic codebases, sporting a massive gamut of features that have been cultivated in excess of a long time thanks to useful will need. It turns out we as well are nevertheless bit by bit chewing on the 4-year-previous leak that revealed DanderSpritz to us, and gaining new insights.”
Observed this short article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to browse extra exclusive information we submit.
Some elements of this report are sourced from:
thehackernews.com



 The scariest security horror stories of 2021
The scariest security horror stories of 2021