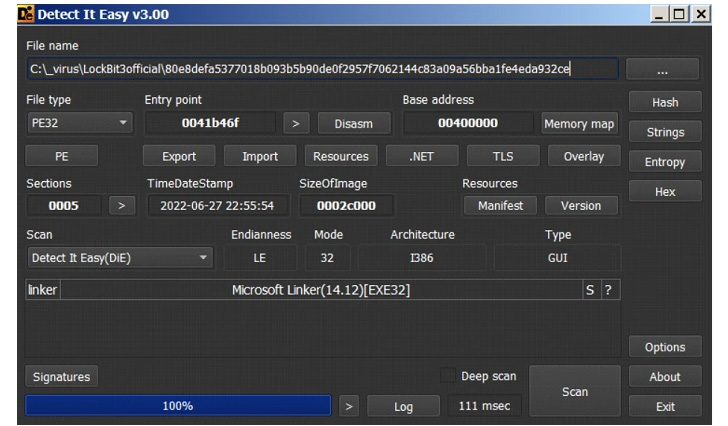
Cybersecurity researchers have reiterated similarities involving the hottest iteration of the LockBit ransomware and BlackMatter, a rebranded variant of the DarkSide ransomware strain that closed store in November 2021.
The new variation of LockBit, identified as LockBit 3. aka LockBit Black, was launched in June 2022, launching a manufacturer new leak web site and what is the incredibly very first ransomware bug bounty plan, together with Zcash as a cryptocurrency payment possibility.
Its encryption system requires appending the extension “HLJkNskOq” or “19MqZqZ0s” to each individual and each file and modifying the icons of the locked data files to that of the .ico file that’s dropped by the LockBit sample to kick-begin the an infection.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The ransomware then drops its ransom take note, which references ‘Ilon Musk’ and the European Union’s Basic Information Security Regulation (GDPR),” Development Micro researchers said in a Monday report. “Lastly, it changes the wallpaper of the victim’s machine to advise them of the ransomware attack.”

LockBit’s comprehensive similarities to BlackMatter appear from overlaps in the privilege escalation and harvesting routines applied to recognize APIs needed to terminate processes and other features as well as the use of anti-debugging and threading approaches built to thwart examination.
Also of note is its use of a “-pass” argument to decrypt its major plan, a conduct noticed in one more defunct ransomware family named Egregor, proficiently producing the binary more challenging to reverse if the parameter is not available.
In addition, LockBit 3. is intended to verify the target machine’s display language to steer clear of compromising systems associated with the Commonwealth of Unbiased States (CIS) states.
“1 notable behavior for this third LockBit version is its file deletion technique: Instead of working with cmd.exe to execute a batch file or command that will conduct the deletion, it drops and executes a .tmp file decrypted from the binary,” the scientists claimed.
This .tmp file then overwrites the contents of the ransomware binary and then renames the binary many moments, with the new file names based mostly on the length of the first file name, like the extension, in an endeavor to prevent restoration by forensic instruments and address its tracks.
The results appear as LockBit infections have emerged as the most lively ransomware-as-a-company (RaaS) groups in 2022, the most current allegedly currently being the Italian Interior Revenue Company (L’Agenzia delle Entrate).

In accordance to Palo Alto Networks 2022 Unit 42 Incident Response Report revealed today based mostly on 600 scenarios managed amongst Could 2021 and April 2022, the ransomware family members accounted for 14% of the intrusions, next only to Conti at 22%.
The improvement also highlights the ongoing results of the RaaS enterprise product, reducing the barrier to entry for extortionists and increasing the get to of ransomware.
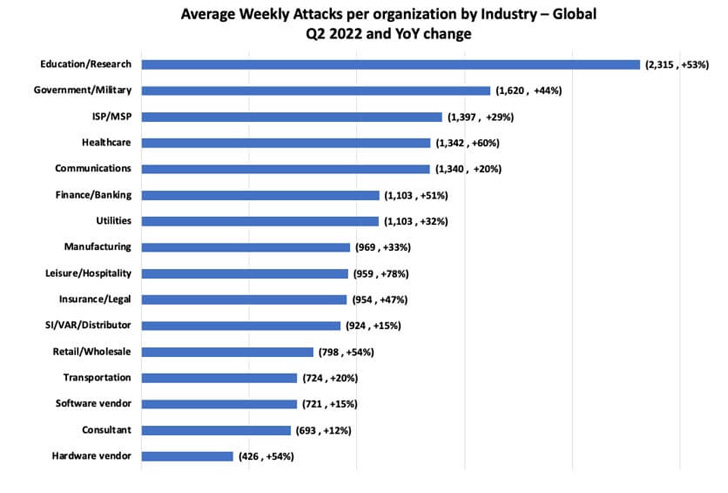
Check out Point’s analysis of cyberattack traits for Q2 2022 shows that the weekly normal of impacted corporations by ransomware reached 1 out of 40, a 59% maximize YoY from one particular out of 64 businesses in Q2 2021.
“Latin The usa has witnessed the most significant maximize in attacks, spotting just one out of 23 businesses impacted weekly, a 43% boost YoY, in comparison to one particular out of 33 in Q2 2021, followed by Asia location that has found a 33% increase YoY, achieving 1 out of 17 corporations impacted weekly,” the Israeli cybersecurity business reported.
Discovered this post interesting? Comply with THN on Fb, Twitter and LinkedIn to study a lot more distinctive content we post.
Some components of this short article are sourced from:
thehackernews.com

 4 Steps Financial Industry Can Take to Cope With Their Growing Attack Surface
4 Steps Financial Industry Can Take to Cope With Their Growing Attack Surface