Cybersecurity researchers on Thursday took the wraps off a new, ongoing espionage campaign targeting company networks in Spanish-talking nations around the world, specifically Venezuela, to spy on its victims.
Dubbed “Bandidos” by ESET owing to the use of an upgraded variant of Bandook malware, the primary targets of the danger actor are company networks in the South American region spanning across producing, building, health care, application products and services, and retail sectors.
Prepared in both equally Delphi and C++, Bandook has a background of becoming bought as a business distant access trojan (RAT) courting all the way back to 2005. Considering that then, quite a few variants have emerged on the menace landscape and put to use in different surveillance campaigns in 2015 and 2017, allegedly by a cyber-mercenary group recognized as Dark Caracal on behalf of authorities passions in Kazakhstan and Lebanon.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In a continuing resurgence of the Bandook Trojan, Test Point last year disclosed three new samples — 1 of which supported 120 instructions — that ended up used by the same adversary to strike authorities, monetary, strength, meals marketplace, healthcare, education and learning, IT, and authorized establishments situated in Chile, Cyprus, Germany, Indonesia, Italy, Singapore, Switzerland, Turkey, and the U.S.
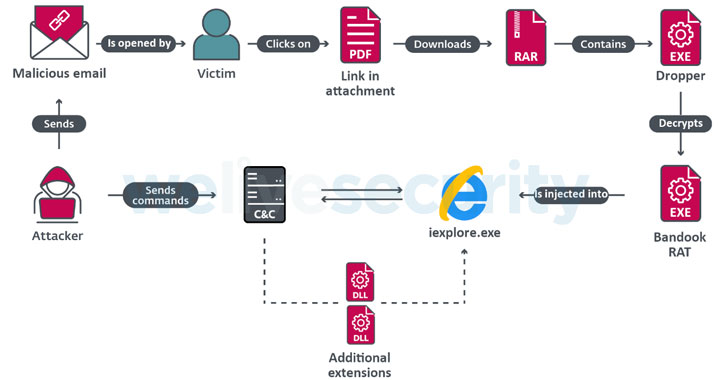
The latest attack chain commences with potential victims receiving malicious email messages with a PDF attachment, which is made up of a shortened URL to down load a compressed archive hosted on Google Cloud, SpiderOak, or pCloud and the password to extract it. Extracting the archive reveals a malware dropper that decodes and injects Bandook into an Internet Explorer system.
Apparently, the most recent variant of Bandook analyzed by ESET incorporates 132 commands, up from the 120 commands noted by Look at Issue, implying that the criminal team at the rear of the malware are advancing their destructive instruments with improved abilities and putting ability.
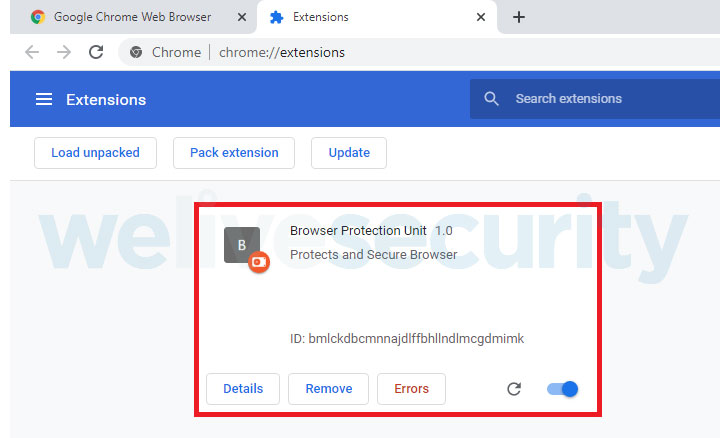
“Particularly attention-grabbing is the ChromeInject features,” mentioned ESET researcher Fernando Tavella. “When the conversation with the attacker’s command and handle server is founded, the payload downloads a DLL file, which has an exported strategy that creates a malicious Chrome extension. The malicious extension attempts to retrieve any credentials that the target submits to a URL. These credentials are saved in Chrome’s area storage.”

Some of the primary commands that the payload is able of processing involve listing directory contents, manipulating information, using screenshots, managing the cursor on the victim’s device, putting in destructive DLLs, terminating working processes, downloading information from a unique URL, exfiltrating the benefits of the operations to a remote server, and even uninstalling itself from the contaminated equipment.
If just about anything, the growth is nonetheless another indicator that adversaries can nonetheless leverage outdated crimeware answers to facilitate attacks.
“[Bandook’s] involvement in unique espionage campaigns […] reveals us that it is nevertheless a suitable resource for cybercriminals,” the scientists opined. “Also, if we contemplate the modifications created to the malware more than the many years, it shows us the fascination of cybercriminals to retain making use of this piece of malware in malicious strategies, earning it extra innovative and a lot more complicated to detect.”
Observed this article attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to examine much more exclusive written content we write-up.
Some components of this short article are sourced from:
thehackernews.com

 CTOs Keeping Quiet on Breaches to Avoid Cyber Blame Game
CTOs Keeping Quiet on Breaches to Avoid Cyber Blame Game