An not known Chinese-talking risk actor has been attributed to a new kind of refined UEFI firmware rootkit known as CosmicStrand.
“The rootkit is located in the firmware visuals of Gigabyte or ASUS motherboards, and we discovered that all these visuals are linked to patterns applying the H81 chipset,” Kaspersky researchers claimed in a new report printed currently. “This implies that a widespread vulnerability could exist that authorized the attackers to inject their rootkit into the firmware’s image.”
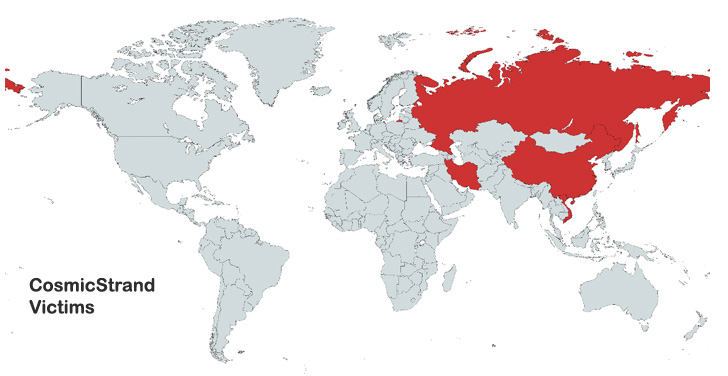
Victims determined are stated to be personal persons situated in China, Vietnam, Iran, and Russia, with no discernible ties to any firm or sector vertical. The attribution to a Chinese-talking risk actor stems from code overlaps among CosmicStrand and other malware these types of as the MyKings botnet and MoonBounce.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Rootkits, which are malware implants that are capable of embedding them selves in the deepest layers of the functioning program, are morphed from a rarity to an increasingly popular prevalence in the risk landscape, equipping threat actors with stealth and persistence for prolonged periods of time.

This kind of kinds of malware “make certain a laptop or computer stays in an infected point out even if the working system is reinstalled or the consumer replaces the machine’s hard push solely,” the researchers claimed.
CosmicStrand, a mere 96.84KB file, is also the next strain of UEFI rootkit to be found out this yr just after MoonBounce in January 2022, which was deployed as part of a targeted espionage campaign by the China-connected innovative persistent threat group (APT41) acknowledged as Winnti.
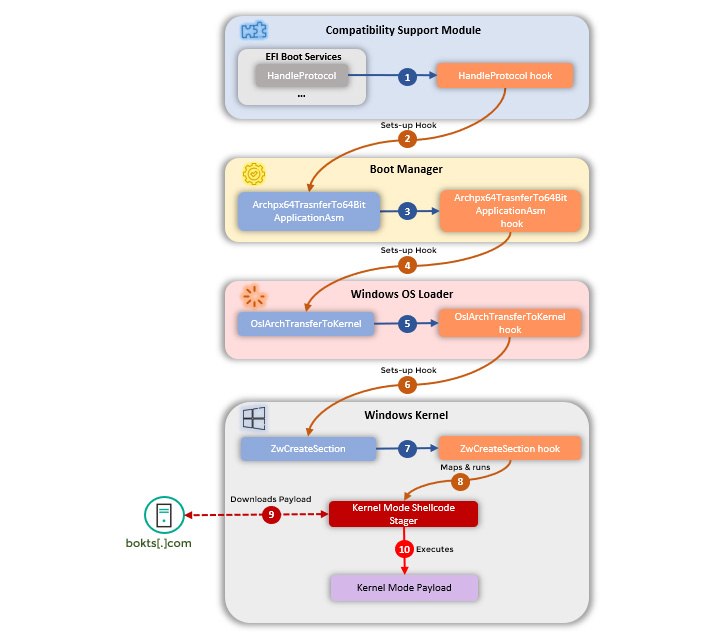
Although the first obtain vector of the bacterial infections is one thing of a thriller, the article-compromise actions entail introducing changes to a driver known as CSMCORE DXE to redirect code execution to a piece of attacker-controlled segment intended to be run throughout method startup, in the long run foremost to the deployment of a malware inside Windows.
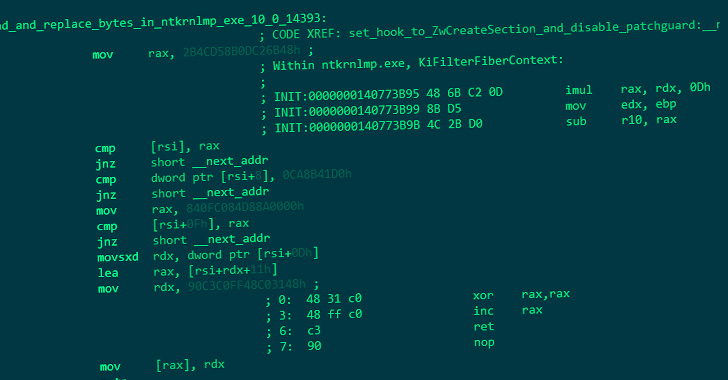
In other words, the objective of the attack is to tamper with the OS loading system to deploy a kernel-amount implant into a Windows equipment each and every time it really is booted, utilizing this entrenched accessibility to launch shellcode that connects to a distant server to fetch the precise destructive payload to be executed on the method.

The specific character of the up coming-stage malware been given from the server is unclear as however. What’s acknowledged is that this payload is retrieved from “update.bokts[.]com” as a sequence of packets made up of 528 byte-knowledge which is subsequently reassembled and interpreted as shellcode.
The “shellcodes obtained from the [command-and-control] server may possibly be stagers for attacker-supplied PE executables, and it is very most likely that lots of extra exist,” Kaspersky famous, incorporating it discovered a total of two variations of the rootkit, one which was used concerning the conclude of 2016 and mid-2017, and the newest variant, which was energetic in 2020.
Curiously, Chinese cybersecurity seller Qihoo360, which drop gentle on the early model of the rootkit in 2017, raised the risk that the code modifications may possibly have been the consequence of a backdoored motherboard attained from a second-hand reseller.
“The most placing element […] is that this UEFI implant would seem to have been utilized in the wild considering the fact that the finish of 2016 – extended in advance of UEFI attacks commenced becoming publicly described,” the scientists explained. “This discovery begs a final concern: if this is what the attackers have been using back again then, what are they making use of currently?”
Discovered this post attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to study much more unique written content we write-up.
Some components of this article are sourced from:
thehackernews.com

 McAfee and Visa offer 50% off antivirus subscriptions for small businesses
McAfee and Visa offer 50% off antivirus subscriptions for small businesses