A massive-scale unauthenticated scraping of publicly available and non-secured endpoints from more mature variations of Prometheus function checking and alerting solution could be leveraged to inadvertently leak sensitive facts, according to the latest analysis.
“Because of to the actuality that authentication and encryption help is rather new, numerous corporations that use Prometheus haven’t but enabled these capabilities and so many Prometheus endpoints are fully exposed to the Internet (e.g. endpoints that operate before variations), leaking metric and label dat,” JFrog scientists Andrey Polkovnychenko and Shachar Menashe claimed in a report.
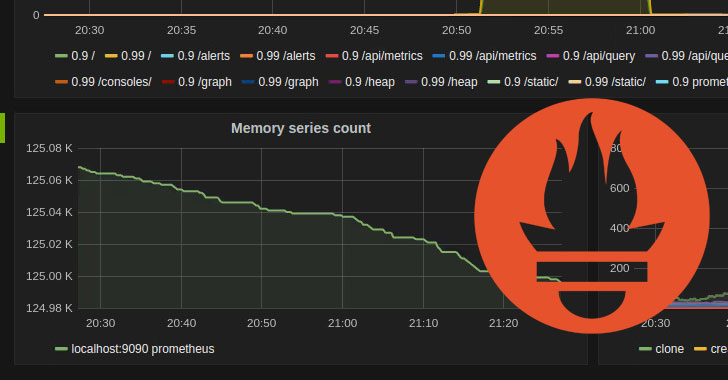
Prometheus is an open up-supply process checking and alerting toolkit utilised to gather and approach metrics from diverse endpoints, along with enabling straightforward observation of program metrics this sort of as memory use, network use, and software package-specific defined metrics, these kinds of as the selection of unsuccessful logins to a web software. Guidance for Transport Layer Security (TLS) and basic authentication was released with variation 2.24. launched on January 6, 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The conclusions arrive from a systematic sweep of publicly-uncovered Prometheus endpoints, which were accessible on the Internet without having demanding any authentication, with the metrics identified exposing application variations and host names, which the researchers stated could be weaponized by attackers to conduct reconnaissance of a target environment right before exploiting a individual server or for put up-exploitation strategies like lateral movement.
Some of the endpoints and the facts disclosed are as follows –
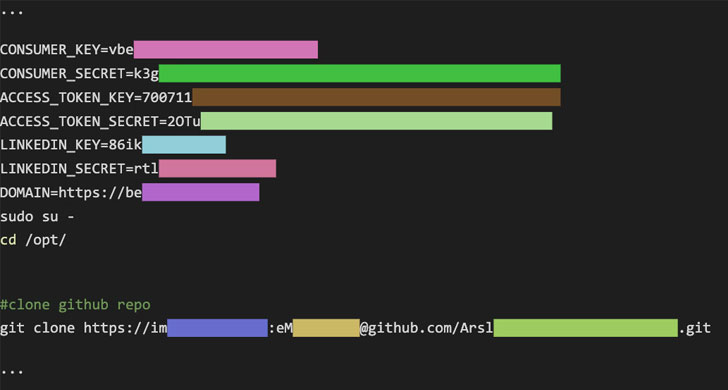
- /api/v1/position/config – Leakage of usernames and passwords delivered in URL strings from the loaded YAML configuration file
- /api/v1/targets – Leakage of metadata labels, like setting variables as effectively as consumer and equipment names, added to target machine addresses
- /api/v1/status/flags – Leakage of usernames when offering a whole route to the YAML configuration file

Even a lot more concerningly, an attacker can use the “/api/v1/standing/flags” endpoint to question the standing of two administration interfaces — “web.empower-admin-api” and “web.empower-lifecycle” — and if discovered manually enabled, exploit them to delete all saved metrics and even worse, shut down the checking server. It truly is worth noting the two endpoints are disabled by default for security motives as of Prometheus 2..
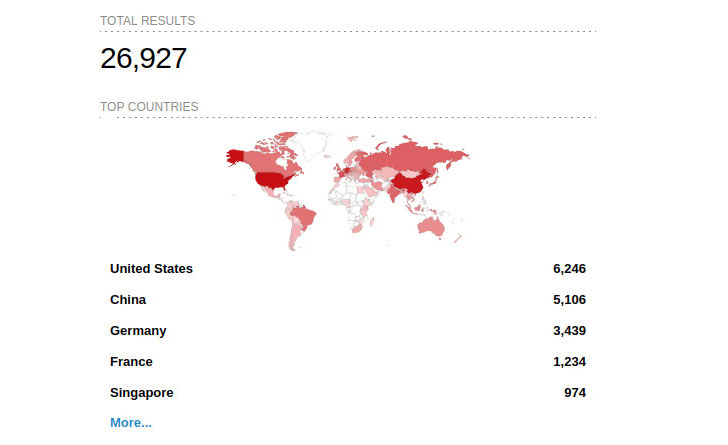
JFrog stated it identified about 15% of the Internet-facing Prometheus endpoints had the API administration setting enabled, and 4% had database management turned on. A complete of close to 27,000 hosts have been discovered through a research on IoT research motor Shodan.
Apart from recommending corporations to “query the endpoints […] to help validate if delicate details may perhaps have been exposed,” the scientists observed that “state-of-the-art people requiring more robust authentication or encryption than what is provided by Prometheus, can also set up a independent network entity to deal with the security layer.”
Uncovered this report fascinating? Follow THN on Fb, Twitter and LinkedIn to browse much more distinctive written content we post.
Some areas of this posting are sourced from:
thehackernews.com

 The Ultimate SaaS Security Posture Management (SSPM) Checklist
The Ultimate SaaS Security Posture Management (SSPM) Checklist