As many as 5 vulnerabilities have been uncovered in Ovarro’s TBox remote terminal units (RTUs) that, if still left unpatched, could open up the doorway for escalating attacks against critical infrastructures, like distant code execution and denial-of-provider.
“Effective exploitation of these vulnerabilities could consequence in remote code execution, which may cause a denial-of-provider problem,” the U.S. Cybersecurity and Infrastructure Security Company (CISA) claimed in an advisory printed on March 23.
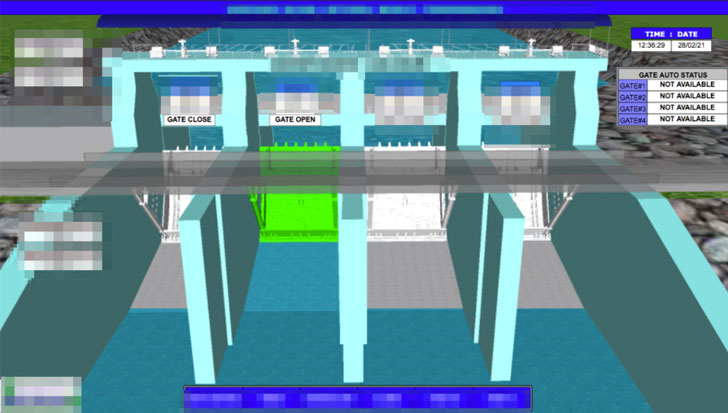
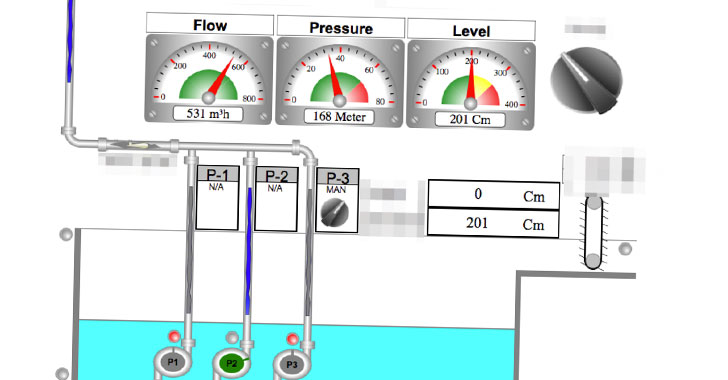
TBox is an “all-in-a single” remedy for automation and regulate systems for supervisory handle and details acquisition (SCADA) programs, with its telemetry computer software employed for remote control and checking of property in a quantity of critical infrastructure sectors, such as h2o, ability, oil and gasoline, transportation, and system industries. TBox equipment can be programmed employing a program suite identified as TWinSoft, which will allow for the generation of interactive web internet pages, the place people will be in a position to watch and handle their web-site belongings.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The flaws were detected and documented to CISA by Uri Katz, a security researcher for operational technology security corporation Claroty. They influence a number of merchandise, such as TBox LT2, TBox MS-CPU32, TBox MS-CPU32-S2, TBox MS-RM2, TBox TG2, and all variations of TWinSoft prior to 12.4 and TBox Firmware prior to 1.46.
Claroty observed that of all the internet-accessible TBox RTUs that have been uncovered online, approximately 62.5% of the equipment necessary no authentication, therefore likely enabling attackers to exploit the HTTP assistance and just take management of the models. Most of the products are said to be found in Canada, Germany, Thailand, and the U.S.
Even further investigation into the remote terminal units revealed numerous vulnerabilities in its proprietary Modbus protocol applied for communications that could be leveraged to operate malicious code in TBox (CVE-2021-22646), crash a TBox procedure (CVE-2021-22642), and even decrypt the login password (CVE-2021-22640) by capturing the network visitors amongst the RTU and the software program.
A fourth flaw found in Modbus file accessibility capabilities granted an attacker elevated permissions to study, change, or delete a configuration file (CVE-2021-22648), although CVE-2021-22644 produced it attainable to extract the tough-coded cryptographic crucial.
As a proof-of-concept, the scientists chained 3 of the above flaws — CVE-2021-22648, CVE-2021-22644, and CVE-2021-22646 — to accessibility the configuration file, extract and decode the challenging-coded critical, and ultimately deploy a malicious update offer in the RTU.
Specified the prevalence of TBox RTUs in critical infrastructure, the investigate demonstrates the dangers included in exposing this sort of gadgets straight on the Internet, thereby posing a menace to the integrity of automation procedures and public security alike.
“Connecting unprotected critical infrastructure factors to the internet carries with it unacceptable dangers that industrial enterprises ought to make by themselves conscious of,” Claroty’s Katz and Sharon Brizinov famous.
“That may perhaps audio like an evident assertion, but it is turning out to be ever more distinct that quite a few corporations usually are not heeding the warnings from scientists about exposing misconfigured web-dependent interfaces on the net and mitigating handle program program and firmware vulnerabilities in a timely manner.”
Discovered this short article fascinating? Follow THN on Fb, Twitter and LinkedIn to browse extra unique content we write-up.
Some areas of this article are sourced from:
thehackernews.com

 ClubCISO Appoints Stephen Khan as its New Chair
ClubCISO Appoints Stephen Khan as its New Chair