As the pandemic continues to speed up the shift towards operating from residence, a slew of electronic threats have capitalized on the wellness concern to exploit weaknesses in the remote get the job done infrastructure and have out destructive attacks.
Now according to network security system provider SAM Seamless Network, above 200,000 businesses that have deployed the Fortigate VPN alternative to empower staff members to connect remotely are vulnerable to gentleman-in-the-center (MitM) assaults that could make it possible for an attacker to current a valid SSL certificate and fraudulently acquire above a connection.
“We quickly found that under default configuration the SSL VPN is not as guarded as it need to be, and is susceptible to MITM assaults fairly simply,” SAM IoT Security Lab’s Niv Hertz and Lior Tashimov claimed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The Fortigate SSL-VPN client only verifies that the CA was issued by Fortigate (or a further reliable CA), hence an attacker can very easily current a certificate issued to a unique Fortigate router without raising any flags, and implement a person-in-the-center attack.”

To obtain this, the researchers set up a compromised IoT unit that’s utilized to induce a MitM attack shortly right after the Fortinet VPN customer initiates a link, which then steals the qualifications before passing it to the server and spoofs the authentication approach.
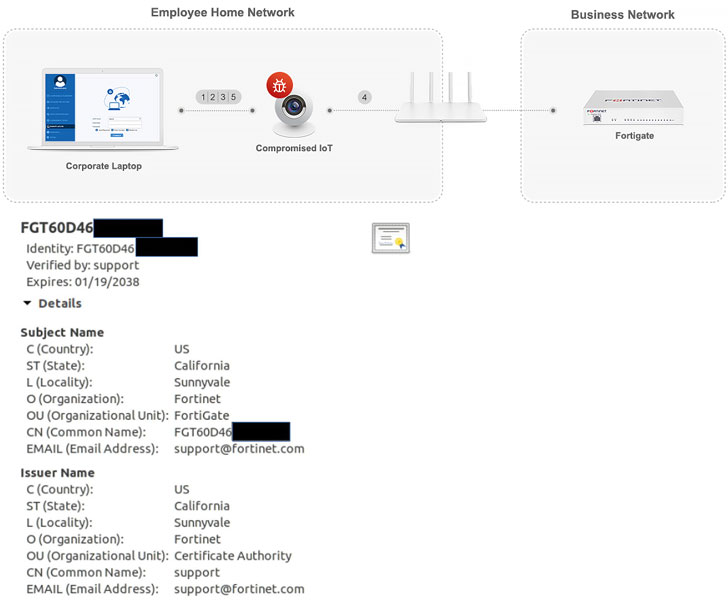
SSL certificate validation, which can help vouch for the authenticity of a web-site or a domain, generally functions by verifying its validity time period, electronic signature, if it was issued by a certification authority (CA) that it can have confidence in, and if the issue in the certificate matches with the server the consumer is connecting to.
The difficulty, in accordance to the researchers, lies in the use of default self-signed SSL certificates by organizations.
Offered that every Fortigate router will come with a default SSL certification that is signed by Fortinet, that very certificate can be spoofed by a third-party as extensive as it is really valid and issued possibly by Fortinet or any other trustworthy CA, as a result making it possible for the attacker to re-route site visitors to a server their control and decrypt the contents.
The major purpose for this is that the bundled default SSL certification utilizes the router’s serial number as the server identify for the certificate. While Fortinet can use the router’s serial amount to test if the server names match, the customer appears to not validate the server title at all, ensuing in fraudulent authentication.
In one circumstance, the scientists exploited this quirk to decrypt the targeted traffic of the Fortinet SSL-VPN consumer and extract the user’s password and OTP.
“An attacker can truly use this to inject his individual visitors, and in essence talk with any internal system in the small business, like level of sales, sensitive knowledge centers, and many others,” the organization claimed. “This is a key security breach that can lead to extreme facts exposure.”
For its part, Fortinet reported it has no plans to tackle the issue, suggesting that customers can manually switch the default certificate and make certain the connections are harmless from MitM assaults.
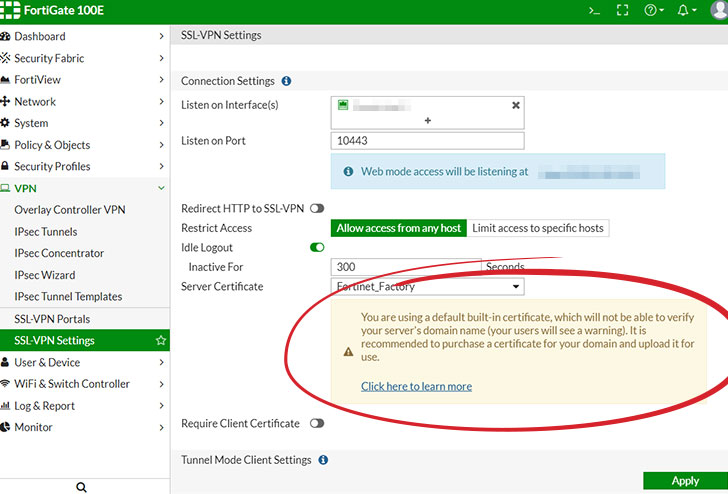
Presently, Fortinet provides a warning when making use of the default certification: “You are employing a default created-in certification, which will not be in a position to confirm your server’s domain title (your people will see a warning). It is advisable to obtain a certification for your area and upload it for use.”
“The Fortigate issue is only an case in point of the current issues with security for the compact-medium firms, specifically for the duration of the epidemic do the job-from-property schedule,” Hertz and Tashimov noted.
“These styles of corporations involve around enterprise grade security these days, but do not have the means and experience to retain organization security methods. More compact corporations demand leaner, seamless, straightforward-to-use security products and solutions that might be less versatile, but give substantially far better basic security.”
Observed this posting exciting? Stick to THN on Fb, Twitter and LinkedIn to study extra distinctive content we put up.
Some parts of this article is sourced from:
thehackernews.com


 Zerologon Windows Server Flaw Used in Active Attacks
Zerologon Windows Server Flaw Used in Active Attacks