A new destructive marketing campaign has been observed hijacking GitHub accounts and committing malicious code disguised as Dependabot contributions with an intention to steal passwords from developers.
“The destructive code exfiltrates the GitHub project’s described insider secrets to a malicious C2 server and modify any existing javascript information in the attacked task with a web-form password-stealer malware code effecting any conclusion-consumer submitting its password in a web type,” Checkmarx reported in a technical report.
The malware is also made to seize GitHub strategies and variables to a distant server by suggests of a GitHub Motion.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

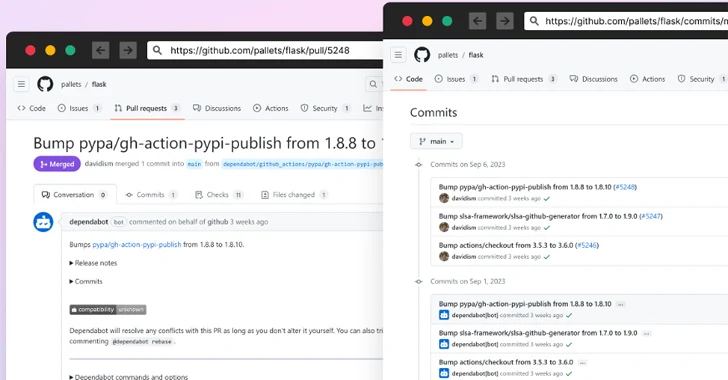
The computer software provide chain security agency reported it observed the atypical commits to hundreds of community and private GitHub repositories involving July 8 and 11, 2023.
It has emerged that the victims experienced their GitHub own accessibility tokens stolen and utilized by the menace actors to make malicious code commits to users’ repositories by posing as Dependabot.
Dependabot is built to warn people of security vulnerabilities in a project’s dependencies by immediately building pull requests to hold them up-to-date.
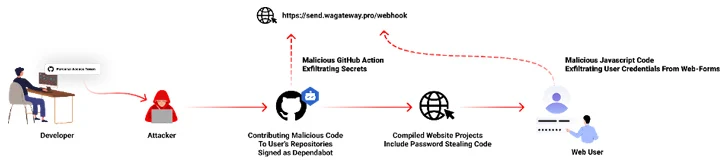
“The attackers accessed the accounts making use of compromised PATs (Own Obtain Token) — most probable exfiltrated silently from the victim’s progress natural environment,” the corporation claimed. Most compromised users are located in Indonesia.
On the other hand, the precise process by which this theft may have taken position is at present unclear, though it can be suspected that it may have concerned a rogue package deal inadvertently put in by the developers.
The growth highlights the ongoing tries on element of threat actors to poison open up-resource ecosystems and facilitate offer chain compromises.
This is evidenced by a new knowledge exfiltration campaign concentrating on both equally npm and PyPI that takes advantage of as quite a few as 39 counterfeit deals to obtain sensitive device data and transmit the aspects to a remote server.
Forthcoming WEBINARFight AI with AI — Battling Cyber Threats with Upcoming-Gen AI Equipment
Ready to tackle new AI-pushed cybersecurity worries? Be part of our insightful webinar with Zscaler to deal with the rising menace of generative AI in cybersecurity.
Supercharge Your Skills
The modules, printed in excess of various times concerning September 12 and 24, 2023, exhibit a progressive maximize in complexity, scope, and obfuscation strategies, Phylum said.
The Israeli company is also tracking what it characterised as a substantial typosquat marketing campaign aimed at npm, in which 125 deals masquerading as angular and respond are staying utilised to ship device information to a distant Discord channel.
Nonetheless, the activity appears to be portion of a “investigation job,” with the creator proclaiming that it’s done to “uncover out if any of the bug bounty programs I am taking part in receives affected by just one of the packages so that I could be the initial 1 to notify them and secure their infrastructure.”
“This is in violation of the npm Acceptable Use Policy, and these sorts of strategies place a pressure on folks tasked with keeping these ecosystems clear,” Phylum cautioned.
Located this posting fascinating? Stick to us on Twitter and LinkedIn to study much more exclusive information we submit.
Some sections of this write-up are sourced from:
thehackernews.com

 China’s BlackTech Hacking Group Exploited Routers to Target U.S. and Japanese Companies
China’s BlackTech Hacking Group Exploited Routers to Target U.S. and Japanese Companies