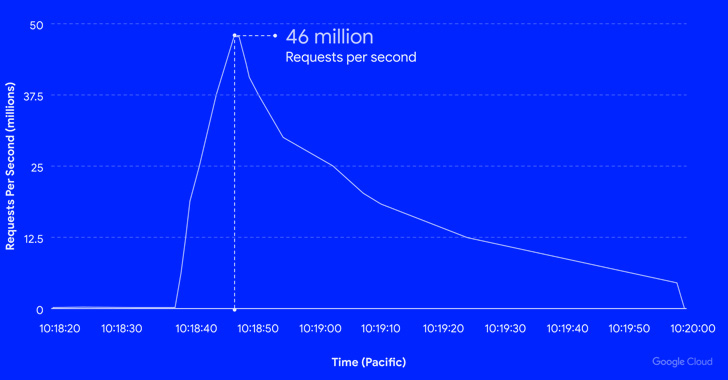
Google’s cloud division on Thursday disclosed it mitigated a collection of HTTPS dispersed denial-of-company (DDoS) attacks which peaked at 46 million requests per next (RPS), generating it the biggest these recorded to day.
The attack, which occurred on June 1, focusing on an unnamed Google Cloud Armor client, is 76% more substantial than the 26 million RPS DDoS attack repealed by Cloudflare earlier this June.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“To give a sense of the scale of the attack, that is like acquiring all the everyday requests to Wikipedia (a person of the top rated 10 trafficked internet sites in the earth) in just 10 seconds,” Google Cloud’s Emil Kiner and Satya Konduru mentioned.
It is really explained to have began about 9:45 a.m. PT with 10,000 RPS, before developing to 100,000 RPS 8 minutes later and even further ramping up in two minutes to hit a significant of 46 million RPS at 10:18 a.m. PT. In all, the DDoS assault lasted for a full of 69 minutes.
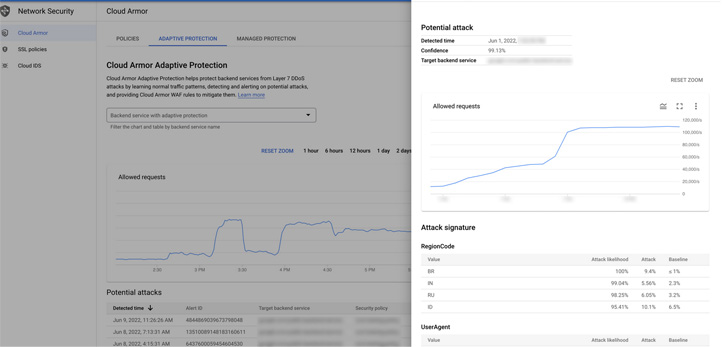
Google stated that the unexpectedly high volume of traffic originated from 5,256 IP addresses positioned in 132 nations around the world, with Brazil, India, Russia, and Indonesia by itself accounting for 31% of all the attack requests.
22% of the IP addresses (1,169) corresponded to TOR exit nodes, but ended up liable for just 3% of the attack site visitors.

“The attack leveraged encrypted requests (HTTPS) which would have taken added computing assets to create,” the business mentioned. “The geographic distribution and styles of unsecured providers leveraged to create the attack matches the Mēris relatives of attacks.”
In September 2021, the Mēris botnet was connected to a DDoS attack on Russian internet large Yandex that peaked at 21.8 million RPS. Parts of the botnet’s infrastructure have been sinkholed in late September 2021.
Found this short article exciting? Adhere to THN on Facebook, Twitter and LinkedIn to read through additional exclusive material we article.
Some areas of this post are sourced from:
thehackernews.com

 UK Carrier Claims to Block One Million Vishing Calls Per Day
UK Carrier Claims to Block One Million Vishing Calls Per Day