It did not acquire prolonged. Intelligence businesses and cybersecurity researchers had been warning that unpatched Exchange Servers could open up the pathway for ransomware bacterial infections in the wake of swift escalation of the attacks due to the fact very last 7 days.
Now it seems that threat actors have caught up.
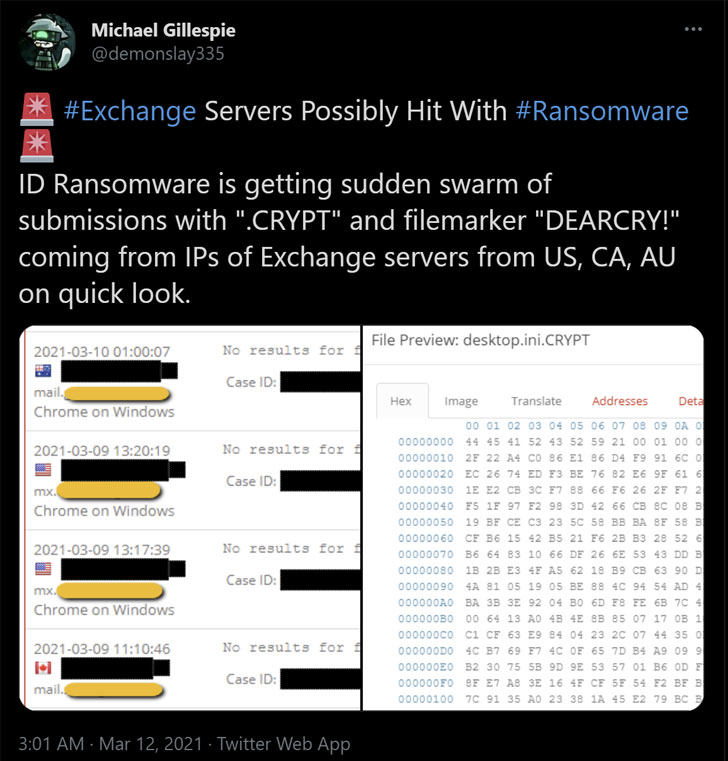
According to the newest reviews, cybercriminals are leveraging the greatly exploited ProxyLogon Trade Server flaws to put in a new pressure of ransomware known as “DearCry.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Microsoft noticed a new spouse and children of human operated ransomware attack clients – detected as Ransom:Get32/DoejoCrypt.A,” Microsoft researcher Phillip Misner tweeted. “Human operated ransomware attacks are using the Microsoft Exchange vulnerabilities to exploit shoppers.”
In a joint advisory posted by the U.S. Cybersecurity and Infrastructure Security Company (CISA) and the Federal Bureau of Investigation (FBI), the agencies warned that “adversaries could exploit these vulnerabilities to compromise networks, steal data, encrypt data for ransom, or even execute a destructive attack.”
Productive weaponization of the flaws makes it possible for an attacker to entry victims’ Exchange Servers, enabling them to achieve persistent technique accessibility and command of an business network. With the new ransomware menace, unpatched Servers are not only at risk of opportunity facts theft but also get most likely encrypted, blocking entry to an organization’s mailboxes.
Meanwhile, as nation-state hackers and cybercriminals pile on to choose gain of the ProxyLogon flaws, a proof-of-principle (PoC) code shared on Microsoft-owned GitHub by a security researcher has been taken down by the enterprise, citing that the exploit is underneath energetic attack.
In a statement to Vice, the organization said, “In accordance with our Suitable Use Guidelines, we disabled the gist next reviews that it contains evidence of strategy code for a not long ago disclosed vulnerability that is remaining actively exploited.”
The move has also sparked a discussion of its own, with scientists arguing that Microsoft is “silencing security researchers” by eradicating PoCs shared on GitHub.
“This is substantial, eliminating a security researchers code from GitHub from their very own merchandise and which has by now been patched,” TrustedSec’s Dave Kennedy stated. “It was a PoC, not a operating exploit — none of the PoCs have had the RCE. Even if it did, which is not their connect with on when the correct time to release is. It truly is an issue in their have merchandise, and they are silencing security scientists on that.”
This was also echoed by Google Undertaking Zero researcher Tavis Normandy.
“If the policy from the start out was no PoC/metasploit/and so forth — that would suck, but it’s their service,” Normandy claimed in a tweet. “As an alternative they stated Ok, and now that it’s become the standard for security pros to share code, they have elected themselves the arbiters of what is ‘responsible.’ How easy.”
If something, the avalanche of attacks should serve as a warning to patch all variations of the Exchange Server as quickly as possible, while also get techniques to discover indicators of indicators of compromise associated with the hacks, presented that the attackers ended up exploiting these zero-working day vulnerabilities in the wild for at least two months before Microsoft produced the patches on March 2.
We have achieved out to Microsoft for extra aspects, and we will update the story if we listen to again.
Observed this report exciting? Abide by THN on Fb, Twitter and LinkedIn to browse additional exclusive information we write-up.
Some elements of this post are sourced from:
thehackernews.com


