An advanced persistent danger (APT) has been joined to cyberattacks on two biomanufacturing corporations that happened this yr with the support of a personalized malware loader known as “Tardigrade.”
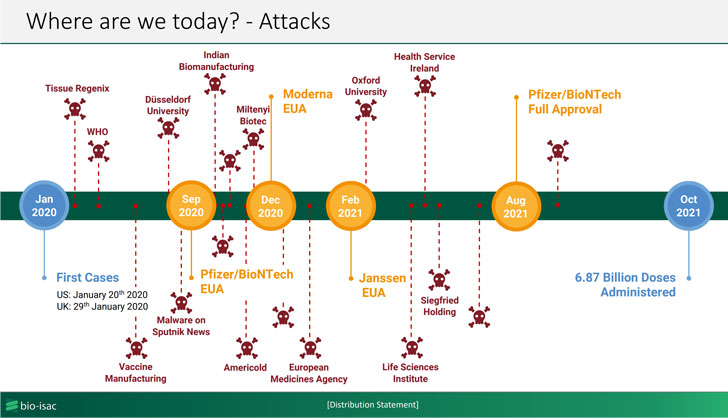
That is according to an advisory printed by Bioeconomy Facts Sharing and Assessment Heart (BIO-ISAC) this 7 days, which famous that the malware is actively spreading across the sector with the very likely target of perpetrating mental home theft, sustaining persistence for prolonged durations of time, and infecting the systems with ransomware.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

BIO-ISAC, which commenced an investigation next a ransomware attack concentrating on an unnamed biomanufacturing facility earlier this spring, characterised Tardigrade as a complex piece of malware with “a superior diploma of autonomy as effectively as metamorphic abilities.” The exact same malware was then employed to strike a second entity in Oct 2021.
The “actively spreading” intrusions have not been attributed to a precise menace actor or a nation, but the agency explained to The Hill that the initiatives mirrored previous attacks by a hacking group joined to Russia.
Spread by means of phishing emails or contaminated USB drives, Tardigrade is an innovative offshoot of SmokeLoader, a Windows-primarily based backdoor operated by a group identified as Smoky Spider and obtainable for sale on underground marketplaces dating all the way back to 2011, with the previous possessing capabilities to capture keystrokes, laterally transfer throughout the compromised network, and escalate privileges.

What is extra, the malware acts as an entry issue for additional malware payloads and is engineered to run autonomously even when minimize off from its command-and-manage server to have out its destructive routines. Businesses in the biomanufacturing field are advised to utilize computer software updates, enforce network segmentation, and exam offline backups of critical organic infrastructure to mitigate the threats.
“This malware is really hard to detect due to metamorphic actions. Vigilance on key personnel company computers is vital,” the scientists stated, adding “Lots of equipment in the sector use outdated functioning programs. Phase them off aggressively and accelerate upgrade timelines.”
Identified this report attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to browse much more distinctive content we post.
Some areas of this report are sourced from:
thehackernews.com


 Practicality of UK government’s cyber bill criticised by industry experts
Practicality of UK government’s cyber bill criticised by industry experts