A new Iranian threat actor has been learned exploiting a now-dealt with critical flaw in the Microsoft Windows MSHTML system to focus on Farsi-talking victims with a new PowerShell-centered details stealer designed to harvest comprehensive facts from infected machines.
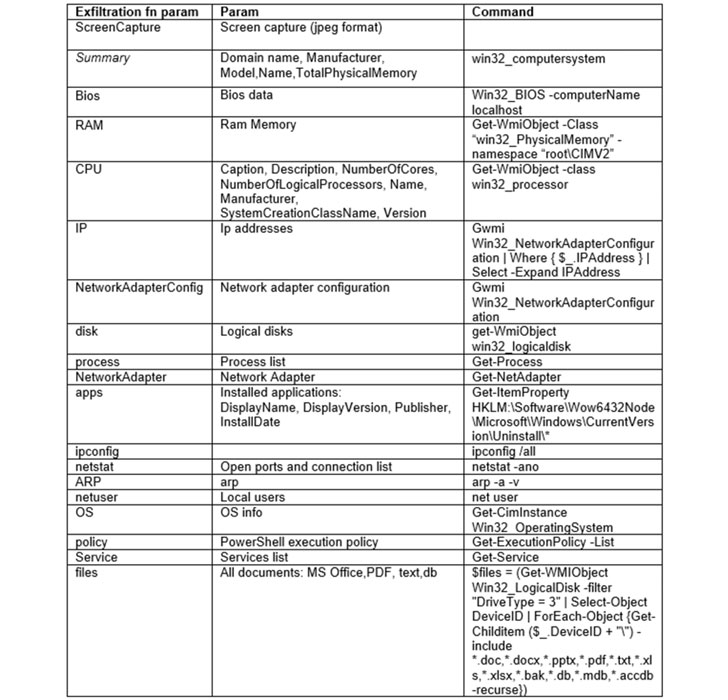
“[T]he stealer is a PowerShell script, quick with strong assortment abilities — in only ~150 lines, it gives the adversary a large amount of critical info such as monitor captures, Telegram information, doc selection, and considerable information about the victim’s setting,” SafeBreach Labs researcher Tomer Bar stated in a report published Wednesday.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Just about fifty percent of the targets are from the U.S., with the cybersecurity agency noting that the attacks are probable aimed at “Iranians who live overseas and might be observed as a danger to Iran’s Islamic routine.”
The phishing marketing campaign, which started in July 2021, concerned the exploitation of CVE-2021-40444, a remote code execution flaw that could be exploited applying specifically crafted Microsoft Place of work documents. The vulnerability was patched by Microsoft in September 2021, weeks following experiences of active exploitation emerged in the wild.
“An attacker could craft a destructive ActiveX handle to be utilised by a Microsoft Office document that hosts the browser rendering engine. The attacker would then have to influence the user to open up the destructive document. People whose accounts are configured to have much less person legal rights on the program could be fewer impacted than customers who function with administrative person rights,” the Windows maker experienced mentioned.
The attack sequence explained by SafeBreach begins with the targets acquiring a spear-phishing email that comes with a Word document as an attachment. Opening the file triggers the exploit for CVE-2021-40444, resulting in the execution of a PowerShell script dubbed “PowerShortShell” that’s capable of hoovering sensitive information and facts and transmitting them to a command-and-management (C2) server.

Though bacterial infections involving the deployment of the data-stealer ended up observed on September 15, a working day after Microsoft issued patches for the flaw, the aforementioned C2 server was also employed to harvest victims’ Gmail and Instagram qualifications as aspect of two phishing campaigns staged by the similar adversary in July 2021.
The enhancement is the most up-to-date in a string of attacks that have capitalized on the MSTHML rendering motor flaw, with Microsoft beforehand disclosing a specific phishing campaign that abused the vulnerability as component of an preliminary accessibility marketing campaign to distribute custom made Cobalt Strike Beacon loaders.
Uncovered this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to read much more special information we publish.
Some components of this report are sourced from:
thehackernews.com


 Ukrainian Cops Bust Mobile Device Hacking Group
Ukrainian Cops Bust Mobile Device Hacking Group