Cisco Methods has introduced security updates to deal with vulnerabilities in various Cisco solutions that could be exploited by an attacker to log in as a root consumer and take handle of susceptible techniques.
Tracked as CVE-2021-40119, the vulnerability has been rated 9.8 in severity out of a utmost of 10 on the CVSS scoring system and stems from a weak spot in the SSH authentication system of Cisco Coverage Suite.
“An attacker could exploit this vulnerability by connecting to an affected device as a result of SSH,” the networking major spelled out in an advisory, including “A effective exploit could make it possible for the attacker to log in to an affected program as the root user.” Cisco explained the bug was discovered during inside security screening.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

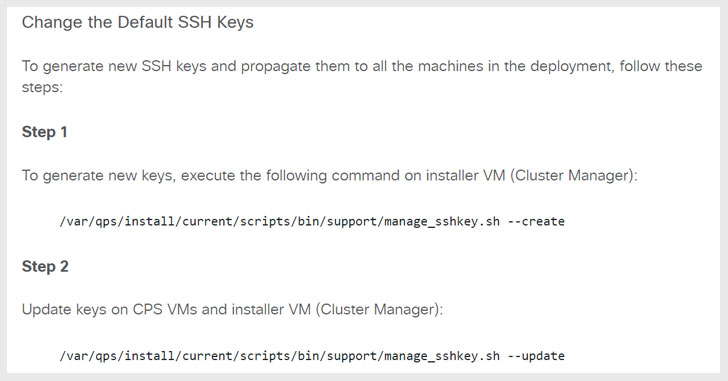
Cisco Policy Suite Releases 21.2. and afterwards will also mechanically create new SSH keys during set up, though demanding a guide course of action to modify the default SSH keys for gadgets being upgraded from 21.1..
Also dealt with by Cisco are many critical vulnerabilities impacting web-based mostly administration interface of the Cisco Catalyst Passive Optical Network (PON) Collection Switches Optical Network Terminal (ONT) that could allow an unauthenticated, distant attacker to log in making use of an inadvertent debugging account existing in the gadget and get about regulate, conduct a command injection, and modify the configuration of the unit.
The vulnerabilities impact the pursuing units —
- Catalyst PON Swap CGP-ONT-1P
- Catalyst PON Swap CGP-ONT-4P
- Catalyst PON Switch CGP-ONT-4PV
- Catalyst PON Change CGP-ONT-4PVC
- Catalyst PON Swap CGP-ONT-4TVCW
Marco Wiorek of Hotzone GmbH has been credited with reporting the 3 vulnerabilities that have been assigned the identifiers CVE-2021-34795 (CVSS rating: 10.), CVE-2021-40113 (CVSS score: 10.), and CVE-2021-40112 (CVSS score: 8.6).

Lastly, Cisco has remediated two extra high-severity flaws in Cisco Tiny Business enterprise Sequence Switches and Cisco AsyncOS that could allow for unauthenticated, remote adversaries to obtain unauthorized entry to the web-based administration interface of the switches and carry out a denial of services (DoS) attack —
- CVE-2021-34739 (CVSS score: 8.1) – Cisco Smaller Small business Series Switches session credentials replay vulnerability
- CVE-2021-34741 (CVSS score: 7.5) – Cisco Email Security Appliance (ESA) denial of services vulnerability
Discovered this report interesting? Adhere to THN on Fb, Twitter and LinkedIn to study much more exclusive articles we write-up.
Some sections of this post are sourced from:
thehackernews.com

 Bowser to Pay Nintendo $4.5M Restitution
Bowser to Pay Nintendo $4.5M Restitution