Web applications endure consistently evolving assaults, the place a web application firewall (WAF) is the first line of protection and a essential element of organizations’ cybersecurity strategies.
WAFs are finding extra advanced all the time, but as its core defense commences with effective sample matching, typically employing Standard Expressions, and classifying malicious website traffic to block cyber attacks.
Evading sample matching
Nevertheless, regretably, this approach is no silver bullet from determined attackers. Once it really is recognized that there is a security layer enabled, malicious actors obtain ways to bypass it, and most of the time, they even succeed.
It typically can be obtained when the very same attacking payload, blocked by WAF, can be disguised to make it ‘invisible’ to the pattern matching system to evade security.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Context-Precise Obfuscation
The web employs numerous technologies, and they all have diverse principles for what comprises legitimate syntax in their grammar, e.g., the browser by itself has (at minimum) 3 various grammars – HTML, CSS, and JavaScript.
Based on the context wherever the attack is targeted, payloads employing mixed circumstance, whitespace, responses work in the similar way as the initial payload.
Encodings
There are many approaches to encode the requests sent, such as typical encodings like URL, Hex, Base64, character encoding, etcetera. The parameter/payload can be encoded numerous moments with any mixture of encodings allowing for the encoded attack payload to slip by means of.
A taste of some of the evasions
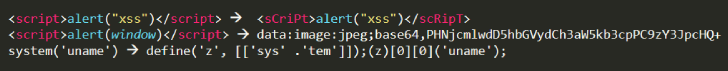
These evasions are not hypothetical, and there are identified scenarios of business WAFs currently being bypassed by things like Unicode encoding.
How does AppTrana take care of evasions
Serious-globe assaults frequently contain numerous actions, together with reconnaissance and a mixture of assaults, so conduct profiling, anomaly scoring present automatic mitigation, and security specialists, like the Indusface security research team, can promptly see if the attack is new or distinctive and choose correct action.
Some of the anti-evasion approaches utilized are outlined below.
Transformation
Evasions like the obfuscations and encodings above are taken care of by AppTrana using transformation features and canonicalization on the information ahead of jogging the inspection/pattern matching section. The order in which transformations are utilized matters a lot and can vary by context.
Anomaly scoring and Habits profiling
Some designs are too small or far too frequent to make entire security conclusions. AppTrana has policies that deal with selected occurrences as indicators, and, applying scoring mechanisms, it would make self-confident choices.
Info such as metrics are tracked throughout a person session, and the risk rating of that session is calculated. e.g., in a journey web-site, if a person moves unusually rapid to scheduling, it is very likely to be a bot, and a captcha could be thrown up.
Customized policies
AppTrana out of the box defense blocks a wide established of attacks and handles most of the evasions. Indusface Managed service involved with the AppTrana WAF augments this with custom made security created following knowledge the specific customer software in depth.
Assaults leveraging application habits/capabilities that can be misused/quirks can be managed only in this way.
How to evaluate WAF
Any security answer really should be on a regular basis evaluated in terms of blocking assaults, FPs, and general performance. A single, not so great, way of evaluating a WAF is to try all types of invalid requests, which includes trivial payloads, and see if the WAF blocks all of them. This is extremely simplistic as it ignores the enthusiasm of actual-earth attacks and the application’s vulnerabilities.
There are also old or obscure attacks on technologies or versions that are no for a longer period in use, so blocking or making it possible for such attacks do not give a lot data about the WAF capability.
How does Indusface consider AppTrana efficacy
As the attack and software landscape modifications, the Indusface security investigation team regularly evaluates its safety to increase coverage and make improvements to performance. It contains quickly reacting to new -days, handling assaults like DDOS, and any new attack techniques.
Bundled as part of AppTrana WAF support are a chopping edge automatic scanner and on-desire manual Penetration Tests support. The skilled guide pen testing workforce evaluates thousands of real-planet web-sites and is generally up-to-day to tackle the newest threats, instruments, and techniques. They also feed this data to the scanner and AppTrana WAF.
The WAF + PT + automated scanner is a exceptional and powerful mixture that will help the firm consider AppTrana WAF from a authentic-entire world standpoint employing the very same equipment and methods that attackers use.
Indusface evaluates AppTrana WAF frequently and comprehensively, together with screening for evasions. Integration with the scanner tunes security to vulnerabilities safely balancing security, usability, and effectiveness.
Utilizing Indusface’s AppTrana Managed WAF presents the customer self confidence that safety is becoming examined, evaluated, and up to date by authorities based mostly on attackers’ real-planet approaches and tools.
Observed this short article attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to browse far more exceptional material we write-up.

 Jack Daniel’s-Maker Suffers REvil Ransomware Breach
Jack Daniel’s-Maker Suffers REvil Ransomware Breach