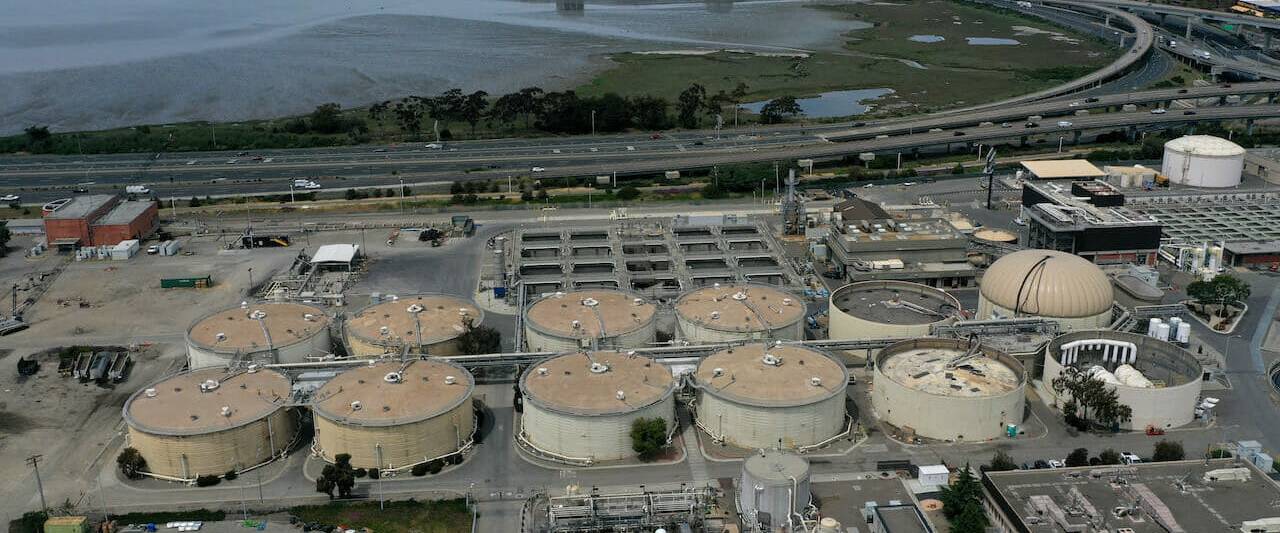
An aerial perspective of a wastewater treatment method plant in California. An try to poison the Oldsmar, Florida drinking water provide by hijacking a distant accessibility process demonstrates the critical danger tied to failure to properly secure operational technology. (Photo by Justin Sullivan/Getty Photos)
In the aftermath of the compromise and attempted sabotage of the Bruce T. Haddock H2o Therapy Plant in Oldsmar, Florida before this yr, threat analysts at ICS security enterprise Dragos conducted an investigation into the incident – and for a quick minute, it appeared as if they experienced discovered a bombshell.
Dragos found a watering-hole attack that had compromised a web site – operated by a Florida-based water utility contractor – that experienced been infecting people with destructive code. What’s more, a user at the Oldsmar plant had truly frequented the web-site on the incredibly day of the attack. The discovery set off alarm bells – yet Dragos, as it explained in this company site post – in the long run decided that its discovery was unrelated to the Oldsmar incident, in which an actor exploited TeamViewer to hijack plant controls and then tried out to enhance the quantity of lye in the water to hazardous amounts.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In accordance to Dragos, the objective of the malware dispersed in the watering-hole attack appears to be to gather knowledge on victims (e.g. working process, browser, existence of digicam and microphone and more) and conduct fingerprinting on them. Dragos believes the motivation at the rear of these steps is simply to prepare the attackers’ botnet, referred to as Tofsee, to superior imitate authentic browser activity so its long term actions will appear extra sensible to cyber solutions.
In the text of Sergio Caltagirone, vice president of threat intel at Dragos, the plan turned out to be a “nothingburger.” Nevertheless, there is a beneficial lesson to be gleaned in the way Dragos dealt with the celebration. The business observed the discovery about more than enough to disclose to pertinent events, but was thorough not to warn the typical public – not when it could not confidently attribute the Oldsmar incident to the watering-hole attack.
Putting the balance concerning giving well timed details and total information was important in this circumstance, stated Caltagirone, who in an interview with SC Media made available a recap of the company’s investigation and disclosure course of action.
Next the Oldsmar incident, the Dragos staff searched for clues or activity relevant to the attack. Consider me by the investigatory method and what led to the discovery of the watering-hole attack.
We were inspecting worldwide internet visitors telemetry. We have resources of knowledge that present us flows of information about the internet. And so we seem for anomalous and exciting exercise in there that arrives from opportunity victims. If we find a sufferer of anything happening… we will then pivot into what is heading on close to that incident to see what we can discover. So we were seeking at things like anomalous RDP traffic… we had been seeking for appealing targeted visitors all over TeamViewer… and finally we went by our to start with run of hypotheses were being like, “Well what else is listed here?”
Then what we do is one thing called… subtractive analysis, which is wherever you really get rid of anything that you feel is intriguing and you seem at what is remaining. We begun on the lookout at what was left in the knowledge and we commenced finding these flows from Oldsmar in the similar time period [of the attack] to a server sitting in Switzerland. And we had been like, “What’s going on listed here?. That is just unusual. Why is Oldsmar speaking to this server in Switzerland?”
We looked into it and we uncovered out that they were heading to this web page. We then talked to… not only just the owner of the web page but the hosting support as very well. They gave us a whole bunch of knowledge, and that is when we observed out there is this seriously obfuscated JavaScript code sitting on this internet site that has not been touched in 3 several years. And Oldsmar happened to touch this the morning of the attack.
Certainly, alarm bells went off. Because… we know adversaries in our ICS space are leveraging watering holes.
At the time you found out this, how did you deal with disclosure?
Right away, we termed a pair of water utility associations, and provided some states and some countrywide organizations and so forth.
We basically wrote up a fast summary: “Here’s what we located, here’s the site. If you’re touching this, we don’t however know what this is, but… you should in all probability glance into it.” And we constantly do that. We try out to offer men and women early warning just before we may possibly not know every thing which is occurring. And that way, of program, it can avert anything even worse.
Then it took us about two weeks to reverse-engineer all the JavaScript code. It was seriously closely obfuscated. And we located that it was utilizing these odd fingerprinting procedures to seize the encrypted handshake protocols that were being staying utilized by the site visitors.
It was capturing matters like browser specifics, what extensions have been mounted, and matters like that. And it was all remaining despatched back to a server being hosted in a Salesforce app – the Heroku application store, which is variety of like a virtual server. They were storing it within of this PostgreSQL databases. We contacted Salesforce and we labored with them on the again conclude of that stuff, which is where by we bought the telemetry of absolutely everyone who was speaking to the script.
And then we [followed the threat back to a] dark web marketplace. We ended up uncovering that [the attackers compromised] a WordPress web page that hadn’t been current in a although, and they hosted their script on it and they were being collecting browser fingerprints to mainly masquerade their botnet traffic, so that they could get previous Palo Alto and Cisco and all the firewalls that now can extra intelligently filter all that targeted traffic out.
We claimed it publicly, even though it was type of a nothingburger to some extent, as additional of an education piece that watering holes are out below – they hit these market web sites.
 Sergio Caltagirone, Dragos.
Sergio Caltagirone, Dragos.
It could have been a nothingburger, but wouldn’t you concur there is still a valuable lesson for cyber organizations about the significance of owing diligence, and practicing dependable reporting and attribution – in particular thinking of that the watering-hole attack was a red herring?
In a day and a 50 %, we assumed this massively intriguing issue happened that correlated to [the Oldsmar attack]… At times you assume you landed on a diamond mine… And then we finish up paying about a month of perform ripping all of this aside, finding out who’s driving it, why they have been doing it, and we ended up like, “Well this was just… a quite intriguing coincidence.”
Intelligence is critical… I imagine there is two issues you have received to stability. You have to stability completeness and timeliness, and commonly people things really do not appear with each other. Usually, if you want to be speedy, you can’t be full. If you want to be entire, you can not be rapid. It is one particular or the other in intel.
And so in our earth, wherever we sense that there is an instant want for defenders to take motion, we will sacrifice completeness for timeliness. But what we really don’t have a tendency to do is public disclosures. And the rationale for that is, it ends up muddying a great deal of the water… I adore the get the job done that reporters do but it brings about the reporters to [sense] blood in the drinking water and all people jumps on [it]. And a single of the factors my shoppers loathe is, in its place of defending their network, having to now reply to media requests or do the job with executives who are becoming questioned by their board or media.
A single of the points we attempt to balance is the frothiness of cybersecurity. When you generate these stories, there’s this massive froth that exists, and it does not allow defenders the house and time they require to do the study in protection of the surroundings. And so which is a person of the reasons why, even while this could have been a gigantic issue, we didn’t go general public. We went to the drinking water utility associations and we had been like, “hey, here’s what’s going on, here’s what we know.” We prevented the general public notification. Even although we may have gotten to extra people, it most likely would have induced additional problems. It would have produced our job harder, it would have designed the defender’s position more durable.
[Once we learned more,] we claimed, “okay, now that we know something a person way or one more, let’s go public and share the tale of how all of this is effective.” So it is a balancing act. The concern we constantly have in our head is: How will the information and intelligence very best get to the folks who can do a little something? And if it’s through the media – if I need to notify the media this mainly because additional electric utilities about the world will listen than if I talk to 20 governments these days – then sometimes we make the determination that the media is the very best outlet to advise the broader group.Soon after you found out that the malware’s main operation was fingerprinting, the up coming phase I imagine was to ascertain what the attacker’s possible drive was. As you ended up heading as a result of the attainable scenarios, what made you lean toward the theory that the attackers were being simply just attempting to make improvements to their botnet as opposed to some grander plan whereby the fingerprinting was one of many tools utilized in a likely sabotage incident?
We can under no circumstances rule out all hypotheses in any type of perform. But we take an alternative competing hypothesis approach… You establish proof either for or towards just about every of these hypotheses, and then you get to a checklist of… the most probably, and then you finish up [ranking] your hypotheses.
Finally, as we were digging deeper and further and deeper, we finished up obtaining the botnets dependable for what was likely on here, and how they have been working with it. And we worked with other security companies and utilities in the place that observed extra than we did on what the botnets had been executing, and it became extremely apparent.
Of training course, the problem right here is that botnets, by their incredibly character, just supply common degree access. They could be leveraged in any variety of methods to compromise a victim… They could get started off as [a minor] adversary and then all of a sudden they come across out that they’re inside of h2o utility and they are like, “Hey I know any individual in my authorities who would buy this form of accessibility.” And then all of a sudden they develop into substantially additional intriguing to men and women than they did as a botnet. So we are generally on the lookout for that.
But the problem is that all those are nonetheless pretty unusual gatherings, so we have to stability the probability of it going on with the true affect.
Inform me far more about the dark web market that you discovered was also subverted by the very same Tofnee botnet actor. What did you learn about the attackers from that?
The dark web web-site we fully grasp was a front conclusion for the controllers. So which is in which they have been essentially advertising accessibility to this ability. The function we did was in conjunction with various other security corporations who… were able to see what the botnet was accomplishing, what data they ended up going just after, what they have been working with the botnet for, and who they were marketing it to.
We regarded that the [attacker] profile did not match anybody who was likely to goal h2o. This was common commodity crimeware variety of stuff heading on. It experienced practically nothing to do with ICS. They certainly did not want interest. They weren’t attempting to blow something up, so to discuss, for the reason that they would destroy their very own functions. It was a really compact procedure, it was very small. General, when we talk about actor motivations and intent, absolutely nothing else lined up with what you see in terms of attacking water as a critical utility.
Most destructive operators out there have no interest in notoriety, and in simple fact it harms their operation… due to the fact it just puts far too significantly warmth on them. This is a person of the factors we hypothesize that crimeware does not commonly goal ICS.
Some parts of this post are sourced from:
www.scmagazine.com

 Feds Warn DarkSide May Not Stay Dark
Feds Warn DarkSide May Not Stay Dark