Hackers are scanning the internet for weaknesses all the time, and if you do not want your group to drop victim, you will need to be the initially to uncover these weak spots. In other words and phrases, you have to undertake a proactive method to handling your vulnerabilities, and a critical initially move in accomplishing this is undertaking a vulnerability evaluation.
Read this manual to find out how to conduct vulnerability assessments in your firm and continue to be ahead of the hackers.
Vulnerability assessment tools
Vulnerability assessments are automated procedures carried out by scanners. This can make them accessible to a wide audience. Quite a few of the scanners are geared in the direction of cybersecurity experts, but there are answers customized for IT supervisors and developers in companies without the need of dedicated security teams.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Vulnerability scanners come in different sorts: some excel at network scanning, others at web purposes, IoT devices, or container security. If you’re a modest enterprise, you’re likely to discover a one vulnerability scanner masking all or most of your devices. Nonetheless, much larger firms with complex networks may possibly want to incorporate several scanners to attain the wished-for amount of security.
How do you complete a vulnerability evaluation?
With the proper tools in hand, you can complete a vulnerability evaluation by working by means of the adhering to steps:

1. Asset discovery
1st, you require to choose what you want to scan, which isn’t really always as straightforward as it appears. A person of the most typical cybersecurity issues going through businesses is a lack of visibility into their electronic infrastructure and its related units. Some good reasons for this include:
- Mobile Gadgets: Smartphones, laptops, and similar equipment are developed to disconnect and reconnect commonly from the business, as nicely as employee’s households and usually other distant locations.
- IoT Equipment: IoT equipment are element of the company infrastructure but may perhaps be linked generally to cellular networks.
- Cloud-Based mostly Infrastructure: Cloud services providers make it effortless to spin up new servers as wanted without IT involvement.
We would all appreciate to do the job in an group that was beautifully structured, but the reality is frequently messier. It can be challenging basically to preserve observe of what diverse teams are putting on-line, or altering, at any provided issue. This lack of visibility is problematic for the reason that it really is challenging to safe what you cannot see. Thankfully, the discovery factor of this method can be mainly automated.
For example, some contemporary vulnerability evaluation equipment, this kind of as Intruder, can complete discovery on public-going through methods and link straight to cloud companies to establish cloud-dependent infrastructure.
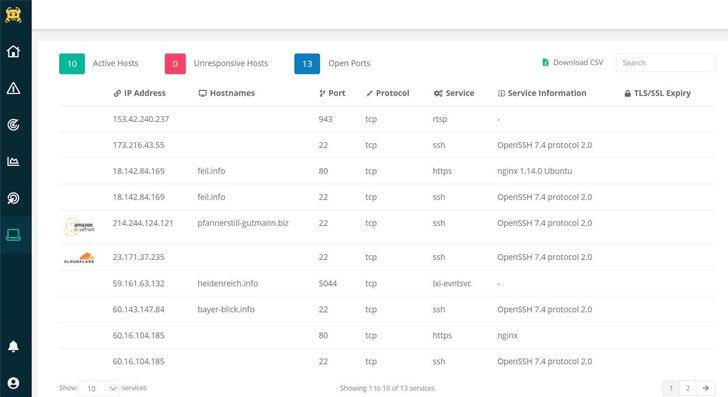 Screenshot of Intruder’s network webpage demonstrating learned systems
Screenshot of Intruder’s network webpage demonstrating learned systems
2. Prioritization
After you know what you have got, the upcoming query is irrespective of whether you can find the money for to run a vulnerability assessment on all of it. In a fantastic environment, you would be jogging a vulnerability assessment frequently on all of your methods. However, distributors typically cost for each-asset, so prioritization can help where budgets can not protect just about every asset the business owns.
Some examples of wherever you may possibly want to prioritize are:
- Internet-struggling with servers
- Client-facing apps
- Databases containing sensitive details
It can be worth noting that the two of the most frequent vectors for untargeted or mass attacks are:
So if you can not manage everything else, at least check out to get these coated in the identical buy.
3. Vulnerability scanning
Vulnerability scanners are built to discover acknowledged security weaknesses and supply direction on how to take care of them. Due to the fact these vulnerabilities are commonly publicly claimed, there is a whole lot of data readily available about susceptible application.
Vulnerability scanners use this facts to detect susceptible products and software in an organization’s infrastructure. The scanner initially sends probes to methods to discover:
- Open ports & jogging expert services
- Computer software variations
- Configuration settings
Dependent on this information, the scanner can often detect many identified vulnerabilities in the program becoming analyzed.
In addition, the scanner sends precise probes to determine specific vulnerabilities, which can only be tested by sending a safe exploit that proves the weak point is present.
These sorts of probes could establish widespread vulnerabilities these kinds of as ‘Command Injection’ or ‘cross-site scripting (XSS)’ or the use of default usernames and passwords for a system.
Dependent on the infrastructure that you happen to be scanning (and particularly how expansive any web-sites are), the vulnerability scan might get anyplace from a several minutes to a couple hrs.
4. Result investigation & remediation
After the vulnerability scan is total, the scanner gives an evaluation report. When studying and establishing remediation plans dependent on this report, you ought to look at the adhering to:
- Severity: A vulnerability scanner should label a prospective vulnerability primarily based on its severity. When arranging for remediation, concentration on the most significant vulnerabilities first, but prevent ignoring the relaxation endlessly. It is not uncommon for hackers to chain a number of delicate vulnerabilities to make an exploit. A fantastic vulnerability scanner will counsel timelines for when to repair every single issue.
- Vulnerability Exposure: Remembering the prioritization higher than – not all vulnerabilities are on community-dealing with methods. Internet-dealing with systems are extra probably to be exploited by any random attacker scanning the internet, building them a increased precedence for remediation. Right after that, you can want to prioritize any worker laptops with susceptible software installed. Moreover, any methods that host specially sensitive details or could adversely influence your organization may perhaps need to have to be prioritized forward of many others.
In most circumstances, there is a publicly released patch to proper a detected vulnerability, but it can typically require a configuration alter or other workaround also. Just after implementing a repair, it is also a good notion to rescan the procedure to make certain the deal with was used the right way.
If it is just not, the process may well continue to be vulnerable to exploitation. Also, if the patch introduces any new security issues, such as security misconfigurations (whilst uncommon), this scan could uncover them and let them to be corrected as nicely.
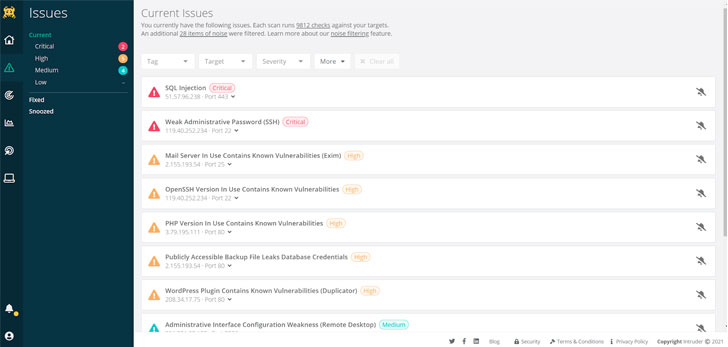 Intruder employs a special algorithm to prioritize issues that leave your techniques exposed, generating it specially easy to come across out what offers the maximum risk.
Intruder employs a special algorithm to prioritize issues that leave your techniques exposed, generating it specially easy to come across out what offers the maximum risk.
5. Continual cyber security
A vulnerability scan delivers a level-in-time snapshot of the vulnerabilities current in an organization’s digital infrastructure. Having said that, new deployments, configuration variations, recently discovered vulnerabilities, and other things can speedily make the group vulnerable once more. For this explanation, you need to make vulnerability administration a continuous method relatively than a one particular-time training.
Considering the fact that a lot of vulnerabilities are introduced when software package is designed, the most progressive software package growth providers integrate automatic vulnerability assessments into their constant integration and deployment (CI/CD) pipelines.
This allows them to identify and deal with vulnerabilities just before the software program is introduced, keeping away from the likely for exploitation and the need to develop and ship patches for vulnerable code.
To conclude
Regular vulnerability assessments are critical to a strong cybersecurity posture. The sheer number of vulnerabilities that exist and the complexity of the average company’s digital infrastructure indicate an organization is just about confirmed to have at the very least a single unpatched vulnerability that locations it at risk.
Discovering these vulnerabilities before an attacker can necessarily mean the change involving a unsuccessful attack and a high priced and uncomfortable knowledge breach or ransomware an infection.
1 of the good issues about vulnerability assessments is that you can do it yourself and even automate the method. By finding the ideal resources and accomplishing frequent vulnerability scans, you can radically lessen your cybersecurity risk.
The Intruder vulnerability evaluation platform
Intruder is a entirely automated vulnerability evaluation instrument intended to look at your infrastructure for upwards of 10,000 identified weaknesses. It can be made to preserve you time by proactively jogging security scans, checking network improvements, synchronizing cloud systems, and a lot more. Intruder generates a report outlining the issues and presenting actionable remediation tips – so you can obtain and correct your vulnerabilities prior to hackers get to them.
Intruder provides a 30-working day totally free demo of their vulnerability evaluation platform. Pay a visit to their web page right now to consider it for a spin!
Located this write-up exciting? Comply with THN on Fb, Twitter and LinkedIn to read through much more unique content we write-up.
Some elements of this post are sourced from:
thehackernews.com

 Emotet Group Harvested Over 4.3 Million Victim Emails
Emotet Group Harvested Over 4.3 Million Victim Emails